Canonical Targets Rust-Based ntpd-rs as Ubuntu's Default Time Sync Tool
Canonical named Rust-based ntpd-rs as Ubuntu's next default time daemon, with Let's Encrypt already running it in production and NTS support changing the security math.
Every stale TLS certificate, every container timestamp that cracks a reproducible build, every Git commit that lands before the one it depends on: these are time sync failures. They are quiet, they are routine, and they are the entire reason why Jon Seager, VP Engineering at Canonical, announced on March 26 that Ubuntu is adopting ntpd-rs as its default time synchronization client and server.
"I am thrilled to announce the next target in our campaign to replace core system utilities with memory-safe Rust rewrites in Ubuntu," Seager wrote in a post titled "Ntpd-rs: it's about time!" on the Ubuntu Community Hub. "In upcoming releases, Ubuntu will be adopting ntpd-rs as the default time synchronization client and server."
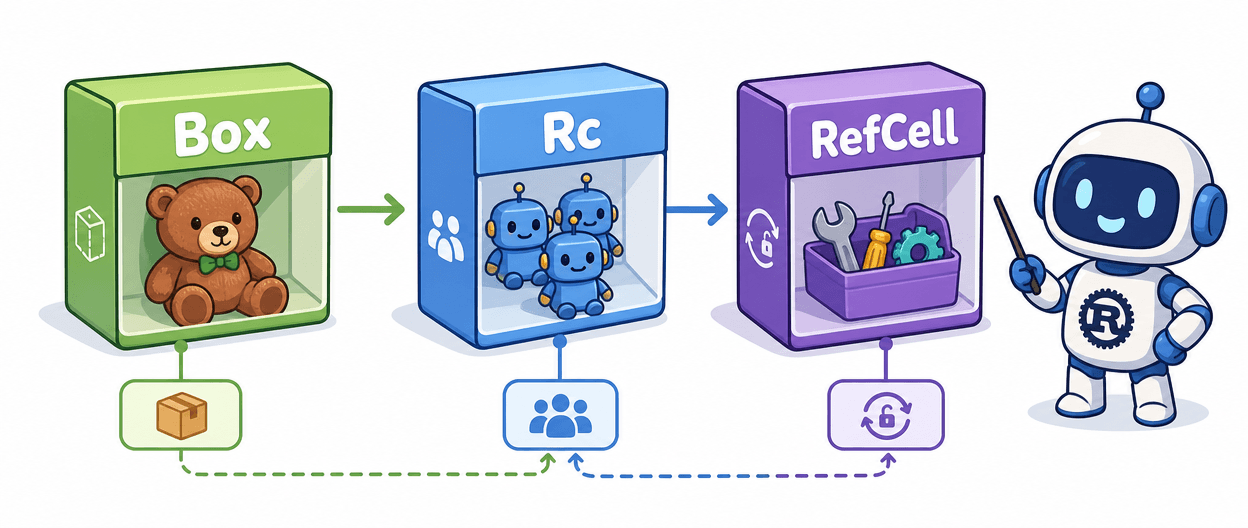
Trifecta Tech Foundation is a nonprofit and Public Benefit Organisation that creates open-source building blocks for critical infrastructure software. Canonical will fund Trifecta Tech Foundation to build new features, enhance security isolation, and ultimately deliver a unified, memory-safe time synchronization utility for the Linux ecosystem. This follows earlier Rust work in Ubuntu including Rust Coreutils and sudo-rs. The external validation that makes this credible: Let's Encrypt already deployed ntpd-rs, first in staging and later in production, providing operational validation outside Ubuntu.
The planned introduction will be phased: ntpd-rs will initially be available in the package repositories for testing in Ubuntu 26.10. From Ubuntu 27.04 onwards, it is intended to run by default, with integrated PTP functionality and a unified binary for NTP, NTS, and PTP. Canonical is financing the development work between July 2026 and January 2027 through the Trifecta Tech Foundation. The 26.04 LTS ships without it.
Since time synchronization plays a key role in TLS certificate validation and the consistency of distributed systems, the choice of the underlying implementation is crucial. The security argument centers on Network Time Security (NTS), an authenticated extension to NTP that eliminates the unauthenticated attack surface behind classical amplification attacks and time-shifting exploits. Combine that with a memory-safe codebase and you close two distinct threat classes in a daemon that runs continuously with external network exposure.
To test ntpd-rs on Ubuntu 26.10 against your existing setup, install it, stop your running daemon (chrony or systemd-timesyncd), and run `ntp-ctl status` once you have configured an observation socket in your `ntp.toml`. The two metrics to anchor on are offset, the gap between your system clock and the reference server (target: under 10ms on a typical broadband connection), and jitter, the variance across consecutive measurements (ideally under 5ms on a stable network). Run `chronyc tracking` before the swap for a baseline. For NTS, point the `[[source]]` block in `/etc/ntpd-rs/ntp.toml` at an NTS-capable server such as `time.cloudflare.com`; the TOML config format is the first migration friction point for anyone accustomed to chrony's `chrony.conf` syntax.
Homelab operators running Proxmox or Kubernetes should watch one additional detail: on hardware with a drifting real-time clock, ntpd-rs will by default refuse to step the clock by more than 1800 seconds on a running system. Adjust `startup-step-panic-threshold` in the `[synchronization]` block if your hardware clock wanders significantly between reboots; otherwise the daemon may silently decline to correct a large initial offset and leave your container timestamps adrift.
Community feedback has been measured rather than strongly oppositional, with early responses questioning whether a unified NTP, NTS, and PTP implementation is necessary for typical desktop systems, and whether NTS offers tangible benefits for most users given the added complexity. Canonical's timeline indicates a gradual transition: ntpd-rs will first be available as an optional component before any decision is made to replace existing defaults.
For Rust maintainers tracking distro adoption signals, the funding model matters as much as the decision: Canonical is paying Trifecta Tech Foundation directly to close feature gaps and harden process isolation, not simply packaging upstream code. That arrangement tends to generate sustained investment in the cryptography and low-level networking crates the broader ecosystem depends on, long after the headline moves on.
Know something we missed? Have a correction or additional information?
Submit a Tip