Claude Mythos Audits Rust Standard Library, Finds Soundness Bugs
Swival’s leak turned an embargoed Rust stdlib audit into a live test of safe Rust, exposing a Windows readlink bug and other soundness concerns.
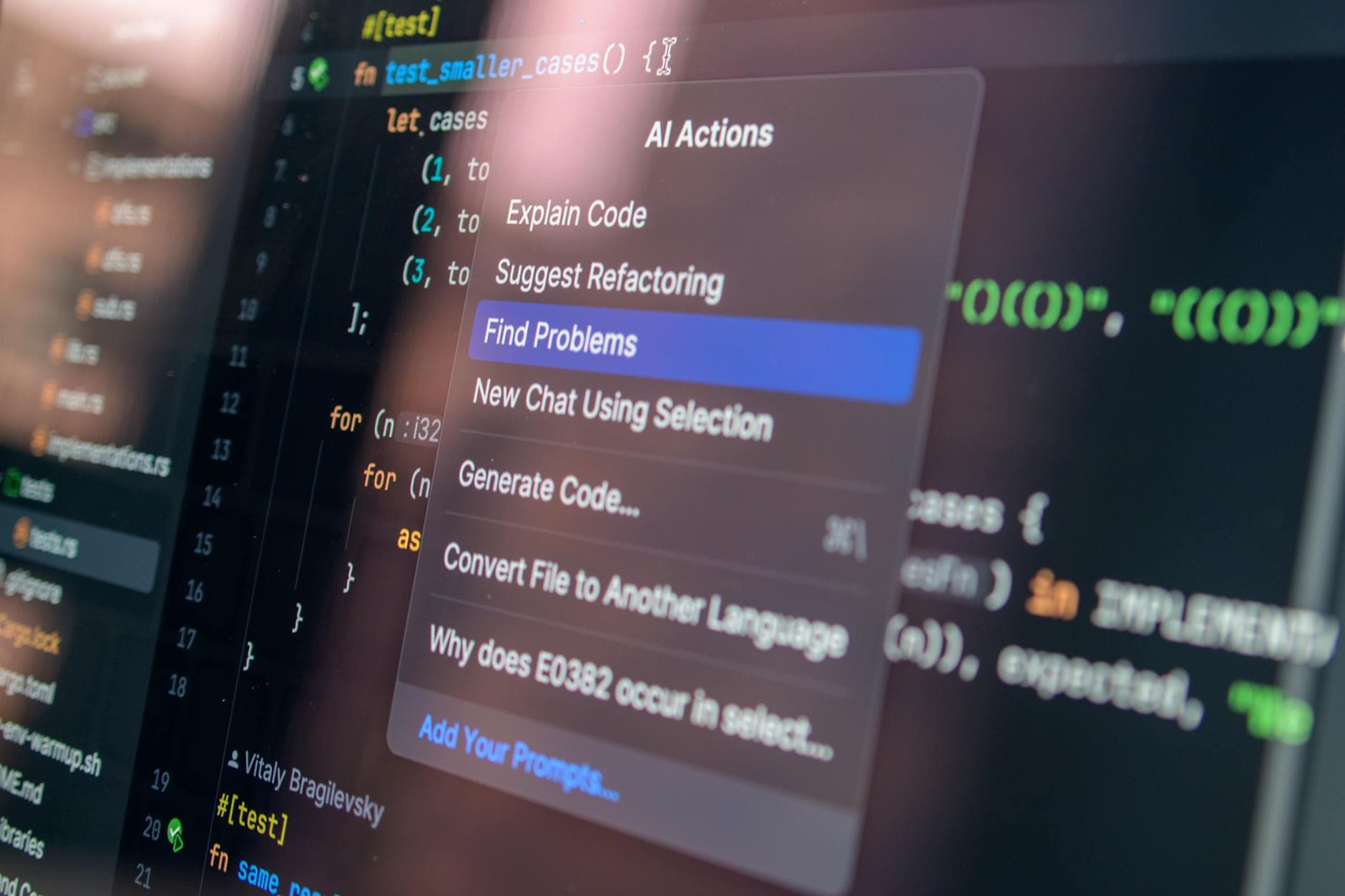
Claude Mythos was supposed to help harden Rust’s standard library, not leak its sharpest findings into public view. But when Swival’s repository surfaced embargoed audit material, the story shifted fast: an AI-assisted review for the Rust Foundation had uncovered real bugs and soundness issues in the code that Rust crates rely on by default, including flaws serious enough to matter far beyond one crate or one platform.
That matters because Rust’s standard library is not just another dependency. Official docs call it the “foundation of portable Rust software,” and every crate gets it by default. When a bug slips into that layer, the impact can ripple through the ecosystem, especially in the parts of the library that bridge safe Rust and operating-system behavior. The public audit material, described as a security audit of the Rust standard library and supporting crates, paired each finding with a write-up and a patch. Lower-severity issues were public; the more serious ones remained under embargo until the leak.
One public example shows why the Rust community took the audit seriously. A finding titled “Unchecked Reparse Name Bounds” was labeled a medium-severity validation gap in library/std/src/sys/fs/windows.rs:773. In plain terms, safe public readlink(path) on Windows could run into out-of-bounds pointer arithmetic and slice creation if malformed filesystem reparse data supplied bad substitute-name offsets or lengths. The patch fixed that by validating the returned byte count and checking bounds before constructing the UTF-16 slice. It is the kind of bug Rust developers assume safe code will not hit, which is exactly why it landed as a jolt.
The broader context makes the leak even louder. Anthropic launched Project Glasswing on April 7, 2026, naming AWS, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks as partners, while committing up to $100 million in usage credits and $4 million in donations to open-source security organizations. Anthropic’s red-team writeup also said Claude Mythos Preview could find and exploit zero-days across every major operating system and web browser, and that more than 99% of the vulnerabilities it found had not yet been patched at the time. The oldest was a now-patched 27-year-old OpenBSD bug.
For Rust, the episode lands in a familiar but uncomfortable place. The project has patched long-standing unsoundness before, including a Rust 1.45.0 fix for integer and float casting. Yet the March 20, 2026 retraction of a Rust blog post over criticism of LLM use showed how sensitive the community remains about artificial intelligence in Rust governance and communication. The message from this leak is narrower and more concrete: safe Rust still depends on the soundness of the standard library, and when that layer meets malformed platform data, the edge cases are exactly where immediate review matters.
Know something we missed? Have a correction or additional information?
Submit a Tip