IronClaw 0.23.0 Advances Multi-Tenant Isolation and Secure Tool Sandboxing
nearAI's IronClaw 0.23.0 ships multi-tenant isolation phases 2-4 and tightened WASM sandboxing, marking the Rust agent runtime's clearest move yet toward production readiness.
Rust's grip on privacy-first AI infrastructure tightened when nearAI published ironclaw-v0.23.0 on March 27, completing the multi-tenant isolation architecture that hosters and SaaS operators need to run independent agent tenants without risking cross-contamination.
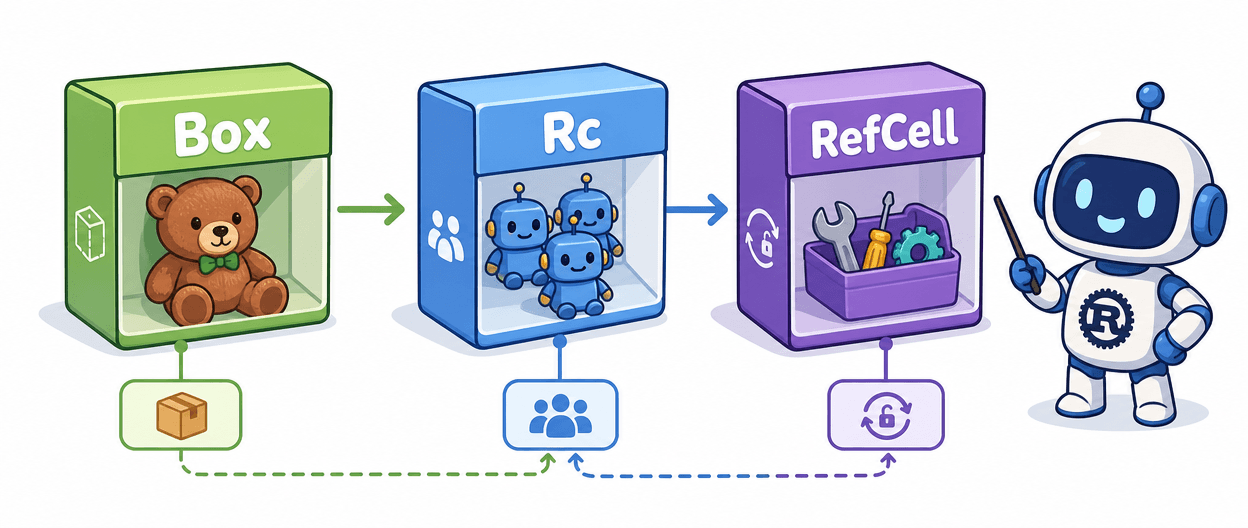
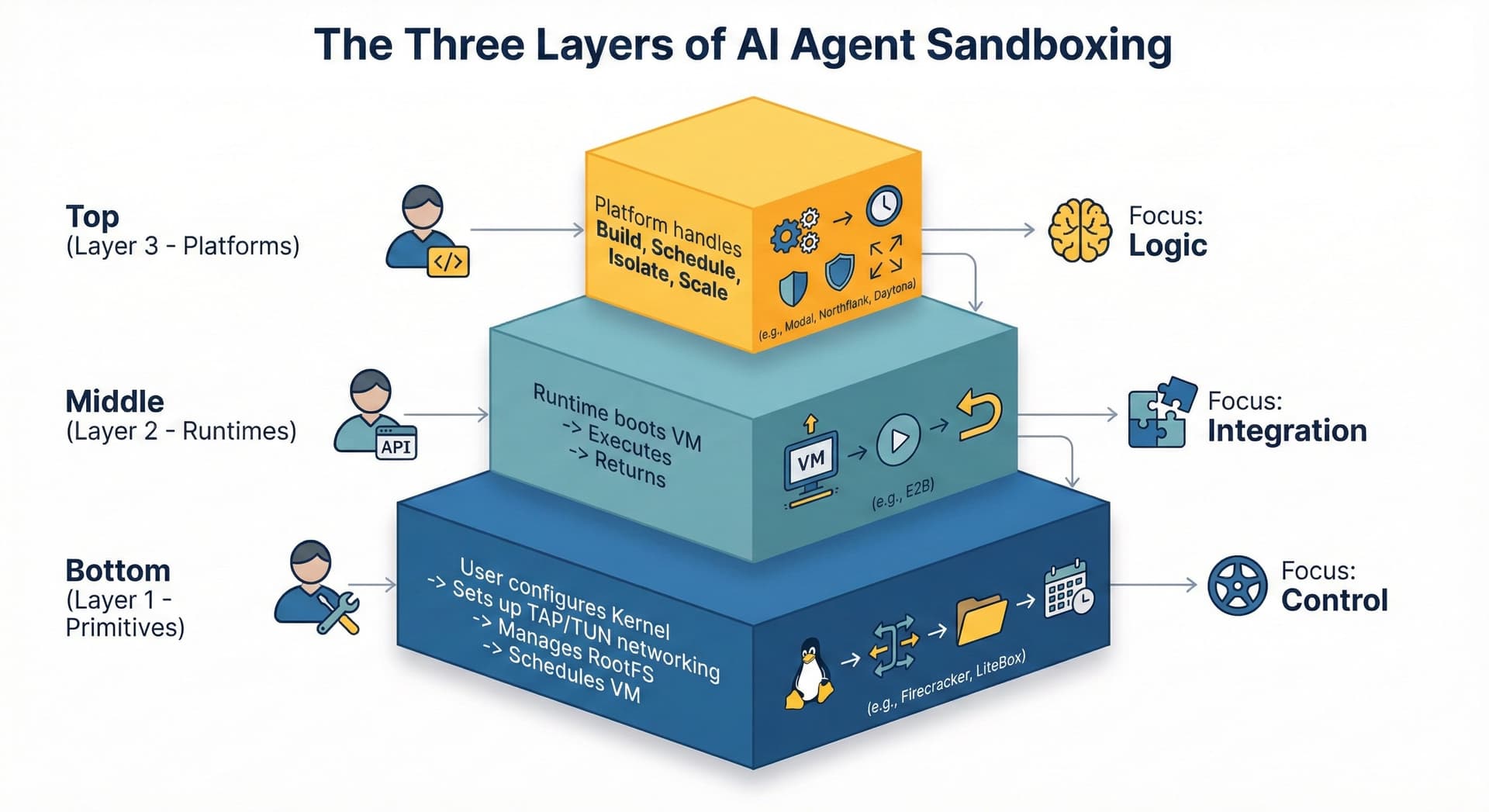
IronClaw entered the agent runtime landscape as a hardened alternative to frameworks like OpenClaw and PicoClaw that prioritized feature velocity above all else. Where those projects let developers rapidly compose tools and skills, IronClaw was designed around a more demanding set of constraints: every untrusted tool runs inside an isolated WASM sandbox, secrets are encrypted at the process boundary, and the runtime assumes a world where many independent tenants share the same infrastructure.
The 0.23.0 release advances that foundation through phases 2, 3, and 4 of multi-tenant isolation. Each phase addressed a distinct layer of the problem: process boundary separation, resource quotas per tenant, and tenant-level observability. The combined effect is a runtime where operators can prevent a single misbehaving tenant from cascading failures into others, enforce hard limits on resource consumption, and trace debugging signals back to specific tenants without leaking cross-tenant context.
Reliability improvements to the routines system arrived alongside the isolation work. Execution paths in IronClaw's job scheduler had been susceptible to leaving orphaned work or producing state inconsistencies when failures interrupted mid-run sequences; the 0.23.0 fixes close those gaps.

Networking and observability also saw meaningful changes: channel-relay authentication was strengthened, URL overrides for relay endpoints are now supported, and telemetry improvements make cross-tenant debugging considerably more practical in production.
For teams ready to actually deploy the runtime, 0.23.0 also ships prebuilt installers for macOS, Linux (both musl and glibc variants), and Windows, removing the need to compile from source for standard deployment targets.
The release marks IronClaw's clearest transition yet from a research and hobby prototyping tool into a platform-ready product. Organizations self-hosting agent infrastructure instead of relying on managed vendors need exactly this kind of operational maturity: reduced blast radius, compliance-friendly isolation primitives, and auditable binaries. Rust's memory safety and WASM-native toolchain make it the natural substrate for that kind of system, and IronClaw's continued development is another data point confirming the language's consolidation at the privacy-first AI infrastructure layer.
Know something we missed? Have a correction or additional information?
Submit a Tip