libghidra brings typed Rust automation to Ghidra reverse engineering
libghidra let Rust scripts drive Ghidra decompilation, renaming, and project handling through a typed RPC API. It shipped as 0.0.1 alpha with a sync client built on ureq and prost.

Reverse engineers, malware analysts, and RE automation builders got a new way to treat Ghidra like infrastructure instead of a GUI when allthingsida launched libghidra, a typed API for Ghidra program databases that exposed decompilation, symbol work, xrefs, and project management through Rust, Python, and C++ clients. The pitch was simple and sharp: automate the parts of Ghidra that usually slow serious analysis down, and do it without touching Java.
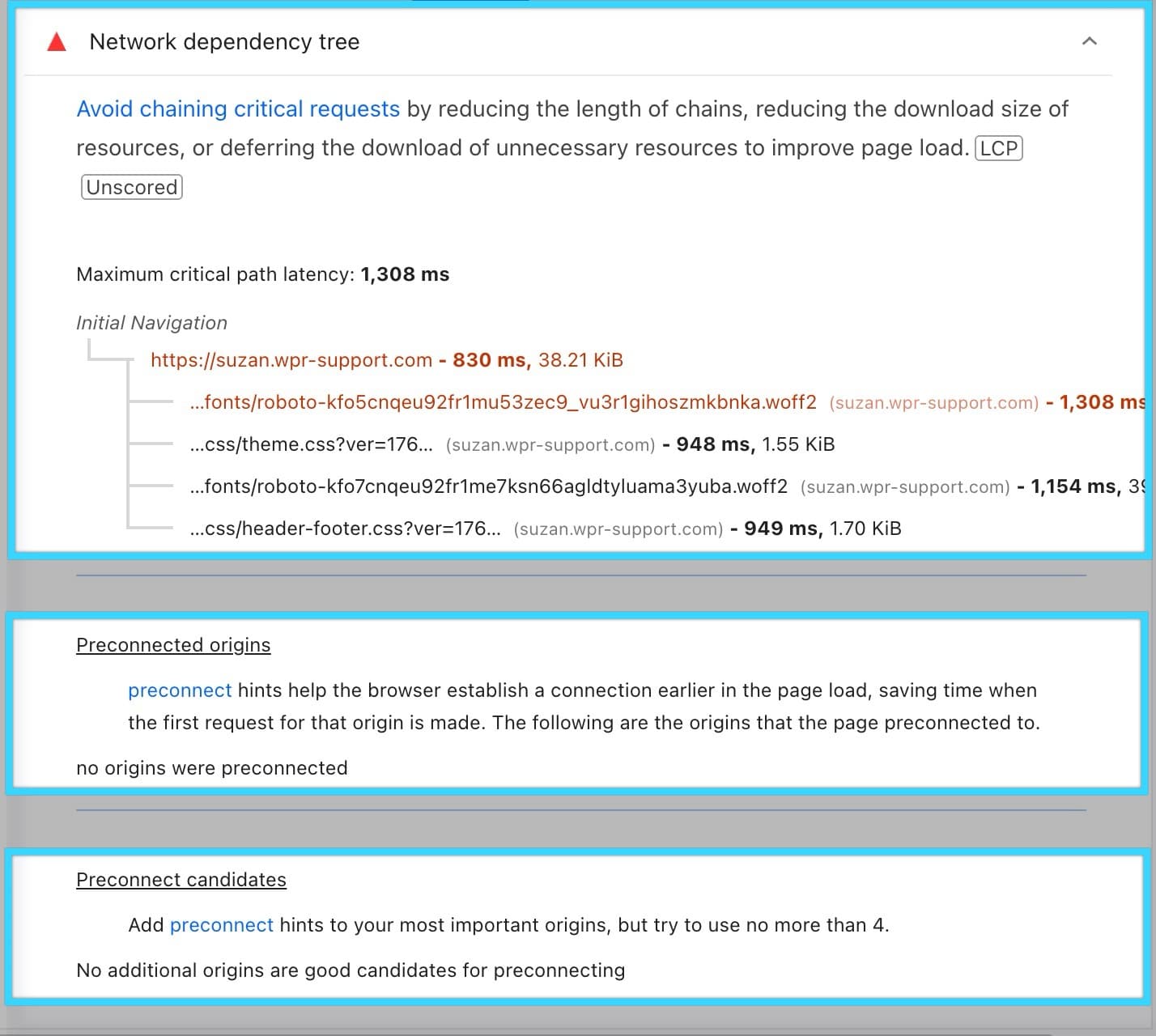
The release landed as 0.0.1 alpha, but it already pointed at a practical workflow. The shortest evaluation path was to install the LibGhidraHost extension into Ghidra 12.0.4 or newer and start the server from the Ghidra GUI. From there, LibGhidraHost served typed protobuf RPCs over HTTP at POST /rpc, with a default bind of 127.0.0.1:18080. That makes the tool feel closer to an analysis service than a desktop plugin, which is exactly the kind of shift that helps when you want to wire Ghidra into repeatable pipelines or AI-driven agents.
The Rust side was built with the same automation-first posture. The client was synchronous, so it did not require an async runtime, and it used ureq for HTTP transport and prost for protobuf serialization. It also added automatic retry with exponential backoff and jitter, a small but important touch for long-running automation jobs that have to survive flaky local services or transient failures. The examples already covered decompilation, memory patching, comments, data items, symbols, type-system editing, CFG analysis, function signatures, switch tables, dominators, loops, and headless end-to-end workflows.
The project sat on top of Ghidra itself, the National Security Agency’s software reverse engineering framework, which runs on Windows, macOS, and Linux and supports both user-interactive and automated modes. That foundation matters because libghidra did not try to replace Ghidra’s analysis engine; it turned it into something scriptable from languages the Rust community already uses. The repository was brand new on April 21, 2026, and a follow-up commit on the same day fixed Python versioning and macOS arm64 build issues, a sign that the cross-platform story was already being tightened. The release also fit into a broader AllThingsIDA pattern: Elias Bachaalany has already shipped other reverse-engineering automation tools, including IDA SQL and IDA C++ tooling, and libghidra extended that same automation mindset to Ghidra.
Know something we missed? Have a correction or additional information?
Submit a Tip