Malicious Rust Crate "logtrace" Pulled After RAT Download Code Discovered
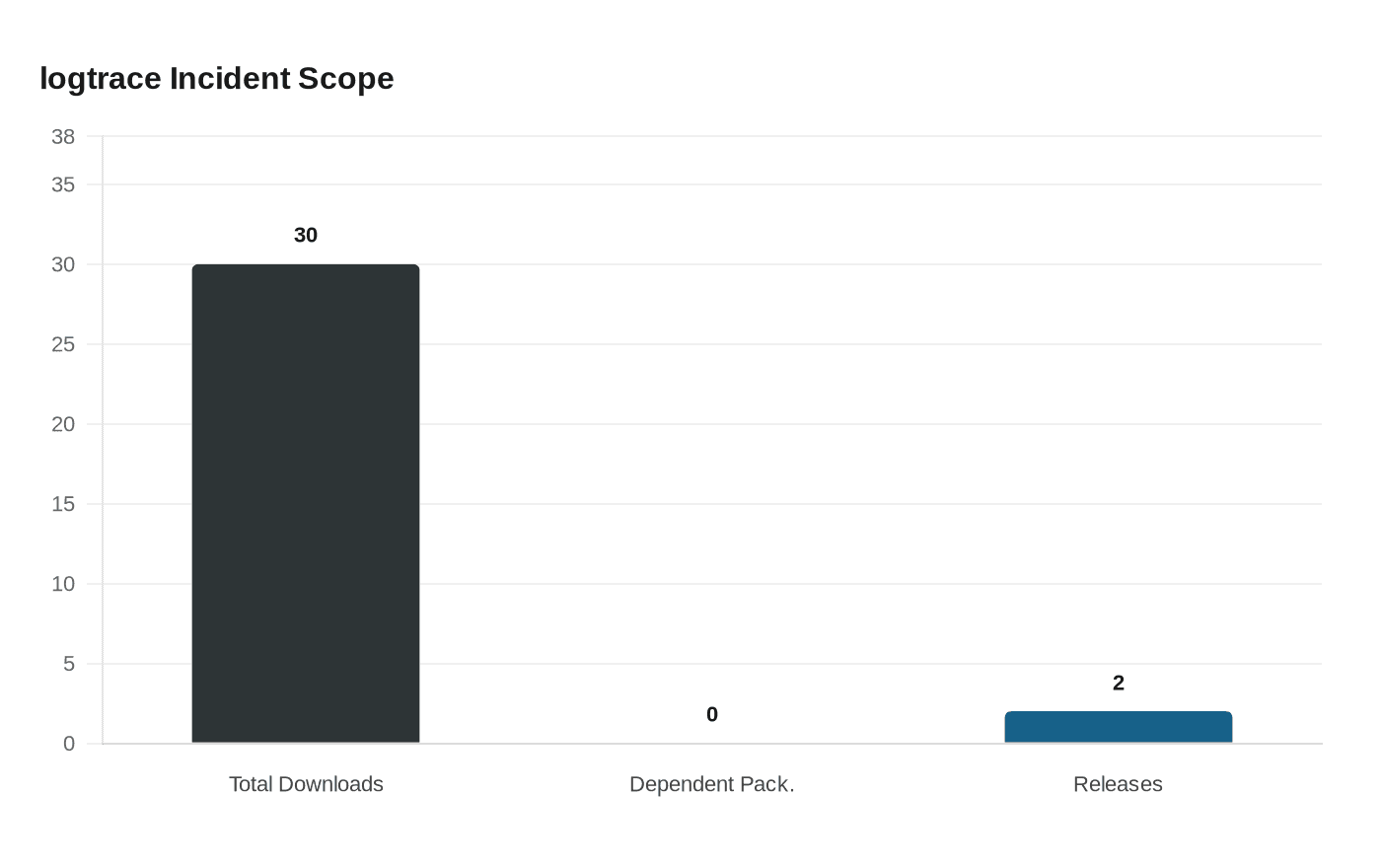
Socket.dev caught logtrace downloading a RAT onto developer machines; only ~30 downloads occurred before crates.io pulled it and RustSec filed advisory RUSTSEC-2026-0081.

A crate named logtrace landed on crates.io on April 1, 2026 carrying code designed to pull a remote-access trojan onto developer machines. Socket.dev detected and reported it, triggering a takedown and a formal RustSec advisory before the package accumulated more than 30 combined downloads across its two releases.
RustSec published RUSTSEC-2026-0081 on April 5, confirming the removal and crediting Socket.dev for the catch. At the time of discovery, no other crate in the public registry had declared logtrace as a dependency, which limited transitive exposure. That did not eliminate risk for the roughly 30 developers who pulled it directly.
The payload mechanism was deliberate in its subtlety. Rather than bundling malware into the crate's source, logtrace's code attempted to fetch and execute a RAT from a remote host at runtime. That approach sidesteps the compilation-time visibility that Cargo's open-source model normally provides. A developer reading the published Rust source would not see a binary embedded in the code; instead, a network call buried in initialization logic fetches the payload after the package is installed. It takes remarkably few lines of Rust to implement this behavior, which is exactly what makes the pattern so replicable and so attractive to attackers surveying language ecosystems for soft targets.

CI pipelines are the natural prey. Build environments routinely run with access to source trees, environment variables, and signing credentials; a RAT that lands during a `cargo install` or `cargo build` step could exfiltrate API keys or repository tokens before any human reviews the logs.
The incident arrived in an ecosystem that has been actively tightening defenses. In February 2026, the crates.io team updated its malicious crate notification policy, routing all malware alerts through RustSec advisories rather than individual blog posts, a change designed to cut noise while keeping genuine threats publicly documented. The logtrace advisory was an early test of that updated pipeline, and the response time, from April 1 publication to April 5 advisory, suggests the coordination between Socket.dev, the crates.io security team, and the RustSec maintainers held up.
For teams that want to close the most obvious gaps before the next incident, a short audit sequence covers the fundamentals. Running `cargo audit` against a project's `Cargo.lock` checks the full RustSec database; the logtrace advisory is already indexed there. Layering in `cargo deny` lets teams enforce crate allowlists and block unreviewed or newly published packages before they reach production. Reviewing the lockfile itself for unexpected additions, particularly crates with sparse download histories, surfaces typosquats and impostor packages at a glance. Keeping the dependency tree lean reduces attack surface directly: every crate not in the tree cannot be weaponized. Finally, isolating build steps that fetch remote artifacts and stripping credentials from CI environments where untrusted code runs closes the worst-case blast radius even if a malicious crate does slip through.
Thirty downloads and zero dependent packages make this about as contained as a supply-chain attack gets. That outcome is a reflection of fast coordination across the detection and response chain. The harder question is whether the next attempt picks a more convincing name, waits longer to activate, and finds a CI environment where no one is watching the outbound network calls during a build.
Know something we missed? Have a correction or additional information?
Submit a Tip
