OpenClaw CVE Wave Sparks Demand for Rust-Based Agent Runtime Alternatives
Tens of thousands of exposed OpenClaw instances and a high-severity privilege escalation CVE are pushing infrastructure teams toward Rust-first agent runtimes with WASM sandboxing.
Tens of thousands of exposed OpenClaw instances surfaced in scanner results circulated during the week of March 24-30, 2026, a figure that landed alongside a cluster of new CVEs and transformed what had been quiet infrastructure anxiety into an active security crisis for anyone running agent workloads at scale.
The most severe disclosure, CVE-2026-32922, arrived on March 29 via Armosec and other specialist teams. It describes a high-severity privilege escalation path affecting self-hosted OpenClaw deployments, the same deployment model that drove OpenClaw's explosive adoption earlier in the year. The underlying pattern is familiar to anyone who has watched a developer platform outgrow its defaults: unauthenticated local gateways left open during testing, unvetted skills accumulating in public registries, and secrets passed directly to LLM-adjacent tool code without sandboxing. Security vendors summarized the exposure plainly, warning that "when self-hosted gateways are misconfigured, the blast radius extends far beyond a single user's chat history."
That blast radius is no longer theoretical. A non-trivial percentage of skills available in community marketplaces have been flagged as malicious or demonstrably vulnerable, creating open pathways for credential leakage and remote code execution on any instance pulling from public registries.
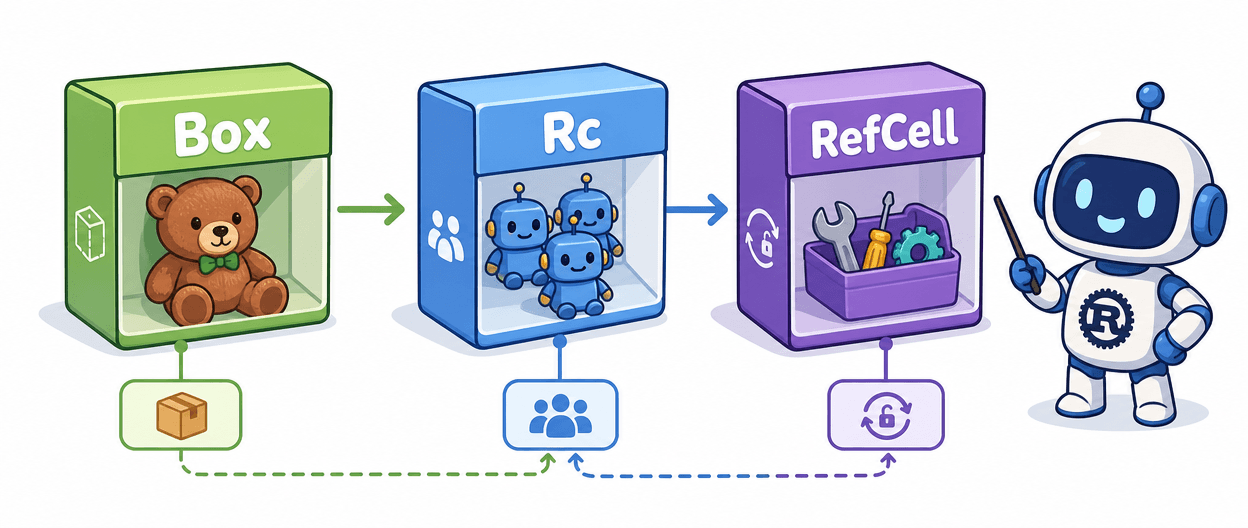
This is where the argument that Rust makes you safe deserves careful qualification, because it cuts both ways. Memory safety eliminates whole classes of bugs, but sandboxing failures, over-permissioned tool grants, and a slow update pipeline can expose a Rust binary just as readily as a Python service. The structural advantage that Armosec's analysis implicitly reinforces is that runtimes built around capability-based isolation and WASM tool sandboxing shrink the attack surface that insecure defaults can open. Rust does not confer that architecture automatically; it enables it more cleanly than most alternatives.
ZeroClaw and IronClaw, both Rust-first agent runtimes, have been direct beneficiaries of the OpenClaw advisory wave. Both projects advertise WASM-based tool isolation, credential vaults that avoid handing secrets to untrusted tool code, and single-binary distribution that makes deployment and auditing considerably less opaque. For infra teams already fluent in Rust's ownership model, the leap to an auditable native binary runtime requires far less justification today than it did a month ago.
The immediate operational priorities are concrete. Audit every self-hosted OpenClaw gateway for unauthenticated endpoints, since CVE-2026-32922 targets exactly that surface. Rotate any credentials that may have passed through tool invocations during the exposure window. Pull the current hardening guide from OpenClaw maintainers, who issued emergency releases alongside the advisories. Enforce allow-listing on community registry skills rather than pulling from the full public catalog, and instrument telemetry on tool invocations so anomalous credential requests surface before they escalate into full compromise.
The OpenClaw episode is, in a sense, the Rust agent runtime community's most effective recruiting event of 2026. Real-world crises convert theoretical safety arguments into procurement conversations, and a CVE wave touching tens of thousands of self-hosted instances is the kind of empirical evidence that actually moves infrastructure roadmaps.
Know something we missed? Have a correction or additional information?
Submit a Tip