Pydantic Launches Monty, a Rust-Built Python Interpreter for AI Agents
Pydantic's Rust-built Python interpreter Monty crossed 5K GitHub stars with a security model so strict that open(), eval(), and exec() simply don't exist inside it.

Pydantic's new open-source project Monty cleared 5,000 GitHub stars and landed on GitHub Trending shortly after its release, drawing the kind of immediate community attention that signals a genuine gap being filled. The project is a Python interpreter written entirely in Rust, built from scratch as a bytecode VM that uses Ruff's parser to transform Python source into its own bytecode format. Pydantic is explicit about what it is not: "Not CPython-with-restrictions. Not Python compiled to WASM."
The motivation is straightforward and specific to the AI agent moment. LLM-generated code has to run somewhere, and the current options force a choice between trusting arbitrary output completely or spinning up containers that introduce hundreds of milliseconds of latency. Pydantic's own benchmark table puts Docker startup at 195ms, third-party sandbox services at roughly 1,000ms or more, and Pyodide at 2,800ms. Monty's listed startup in that same table is 0.004ms, because, as the project documentation states, "Monty starts in microseconds because it's embedded in the parent process." A separate benchmark on a weather agent example shows 4.8ms with type checking enabled and 4.5 microseconds without it. The original project announcement cited a 0.06ms figure; the Pydantic team's own materials present the more granular breakdown, and those numbers reflect different measurement conditions.
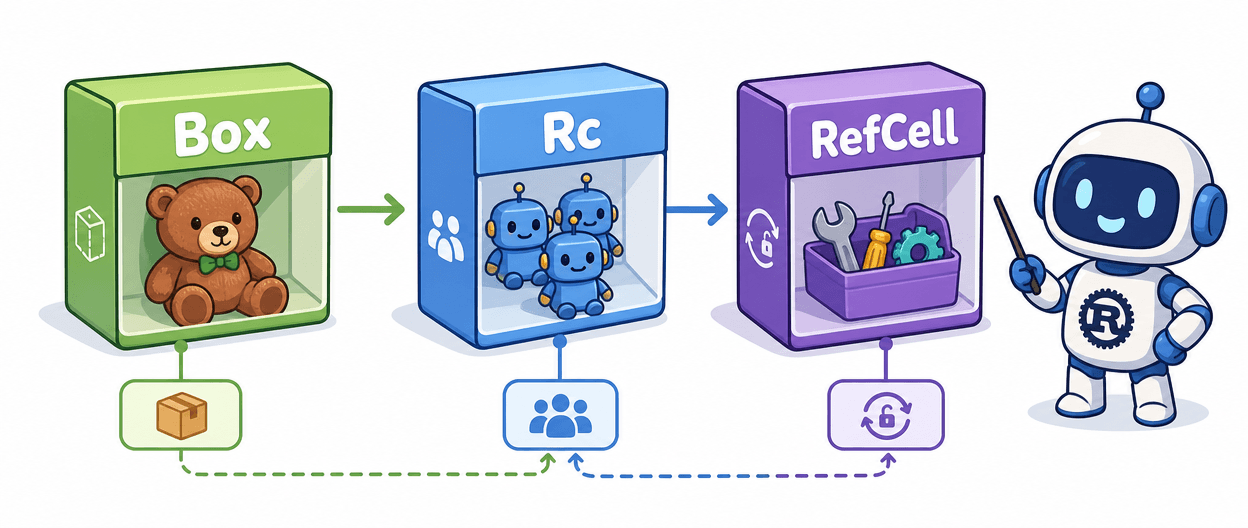
The security architecture is what makes the performance comparison meaningful. Monty takes a deny-by-default approach in which functions like open(), __import__(), eval(), and exec() do not exist inside the interpreter. The os and sys modules are stubs returning safe values; sys.version, for example, returns "3.14.0 (Monty)". Subprocess execution, file access, and environment variables are all blocked unless the host developer explicitly grants them. Pydantic frames this as the difference between a firewall that blocks known-bad ports and one that blocks everything and then allowlists specific traffic. For cases where some file interaction is needed, Monty provides an in-memory filesystem abstraction rather than opening host access.
Execution flows from LLM output through Monty's parser and type checker, into bytecode, and then to execution, with callbacks into the host environment in Python, Rust, or JavaScript whenever an external function is invoked. The interpreter can serialize its entire state into bytes, enabling workflows to be paused and resumed across restarts, which Pydantic describes as enabling "durable agent workflows that survive restarts."

At version 0.0.3, the current release, Monty does not yet support class definitions, match statements, context managers, generators, or most standard library modules. The project covers what the team calls "the core Python features needed for typical LLM-generated code" while remaining explicit that it is not a complete Python implementation. Planned maturity includes shims for popular libraries including requests, polars, duckdb, and playwright, always added by explicit allowlisting rather than restriction removal.
Monty is a Rust binary with no CPython dependencies, running on Linux, macOS, Windows, and anywhere Rust can be compiled, including embedded systems and edge devices. Bindings exist for Rust and JavaScript/TypeScript. The project is also positioned as a predecessor to deeper Pydantic AI integration; the CodeExecutionToolset referenced in Pydantic's weather agent demo is described as forthcoming in Pydantic AI.
Community reaction on Hacker News was characteristically divided. User globular-toast pushed back on the premise: "I don't get what 'the complexity of a sandbox' is. You don't have to use Docker. I've been running agents in bubblewrap sandboxes since they first came out." User vghaisas raised legitimate use-case questions about whether the real power of terminal agents depends on network and filesystem access that Monty deliberately removes. User SafeDusk saw it differently: "Sandboxing is going to be of growing interests as more agents go 'code mode.'" The skepticism reflects genuine architectural tradeoffs Monty's team will need to address as the project moves beyond its early version status.
Know something we missed? Have a correction or additional information?
Submit a Tip