Triangle Postgres Group Explores pgrx for Building Database Extensions in Rust
Patrick Reynolds, a former Distinguished Engineer at GitHub now at PlanetScale, made the case at a Raleigh meetup that pgrx makes Rust a viable replacement for C in Postgres extension work.

Writing a PostgreSQL extension has always required a reckoning with C: raw pointers into Postgres memory contexts, manual lifecycle management, and failure modes that can take down the entire database server process. Patrick Reynolds, a software engineer at PlanetScale and former Distinguished Engineer at GitHub, made the case last week that this no longer has to be the tradeoff.
Reynolds spoke at the Triangle Postgres Users Group meetup on March 24, hosted by Atomic Object in Raleigh, covering pgrx, a Rust framework that wraps Postgres' C-language extension API behind memory-safe, idiomatic abstractions. The talk drew Postgres-focused engineers and Rust developers curious about where the two ecosystems intersect at the database kernel boundary.
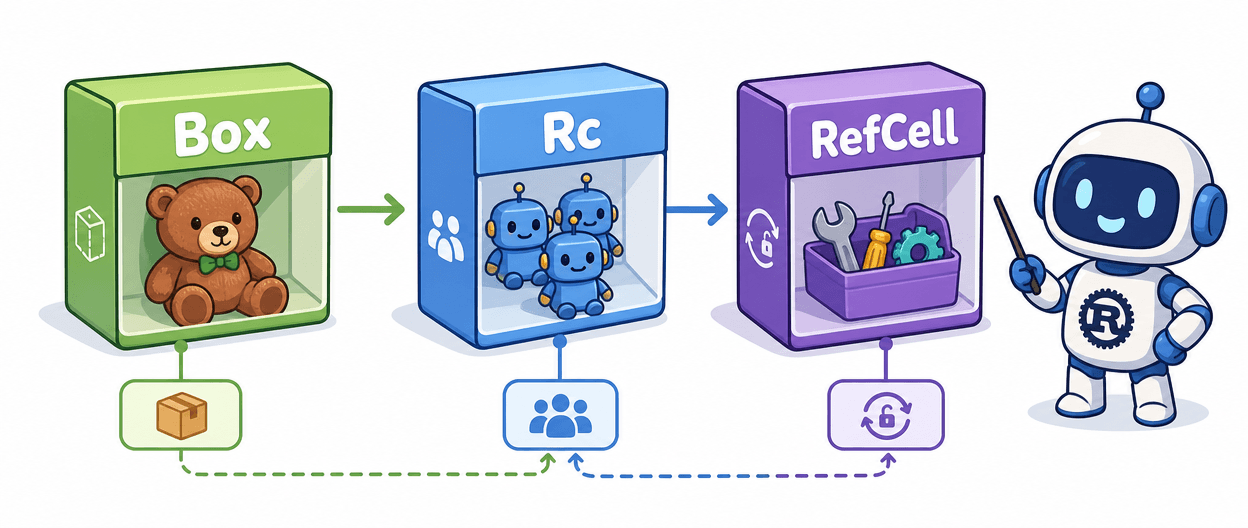
The argument for Rust here is not aesthetic. Postgres extensions execute inside the server process itself, so a bad pointer dereference or a mishandled memory context doesn't produce a polite error message; it crashes everything. pgrx surfaces Postgres' own memory context model through Rust's ownership and lifetime system, making entire classes of use-after-free bugs impossible to express at the type level. For teams already running Rust in application code, pgrx offers the same basic contract: if it compiles, it probably won't corrupt the database.
Reynolds' position at PlanetScale, which operates Postgres as a managed cloud service, means the talk extended well past theory into deployment realities. One of the sharper operational edges with pgrx-built extensions is ABI compatibility across Postgres major versions: extensions must be compiled against the specific version they'll run on, and pgrx ships a versioned shared-object feature specifically to manage the transition window during upgrades. Sessions started before `ALTER EXTENSION my_extension UPDATE` runs will keep loading the old shared library until they reconnect. Targeting an unsupported ABI is possible with ` features unsafe-postgres`, a flag that flags exactly what it says. The framework is currently at v0.17.0, which migrated the codebase to Rust edition 2024, and the maintainers have been candid in the project README that it has not reached v1.0.0 precisely because soundness questions around the FFI boundary are still being resolved, even as it runs in production at multiple organizations.
For engineers who want to try it, the entry point is three commands. Install the toolchain subcommand with `cargo install cargo-pgrx locked`, run `cargo pgrx init` to download and compile the supported Postgres versions locally, then `cargo pgrx new my_extension` to scaffold a working crate. The resulting directory contains a Cargo.toml, a .control file, and a src/lib.rs with a working example function. Running `cargo pgrx run` compiles the extension as a shared library, installs it into the local Postgres instance, and drops you into a psql shell without touching a production server.
A natural first project is a custom Postgres type with domain validation baked in: define a struct, implement the pgrx type traits, and Postgres gains a new SQL type whose internal invariants are enforced at compile time rather than by convention in application code. This is the category of work where pgrx earns its keep most clearly, moving guarantees down the stack to the layer where they are hardest to circumvent.
Reynolds bringing that perspective from PlanetScale's operational experience gave the Triangle Postgres Users Group something more valuable than a framework overview: a practitioner's honest account of where the sharp edges actually are, and which ones are worth crossing anyway.
Know something we missed? Have a correction or additional information?
Submit a Tip