Hackers Claim San Felipe Del Rio
WorldLeaks posted a dark-web claim March 31 threatening to release SFDRCISD student records, staff payroll data, and family contacts within 48 hours — putting 10,500 students at risk.
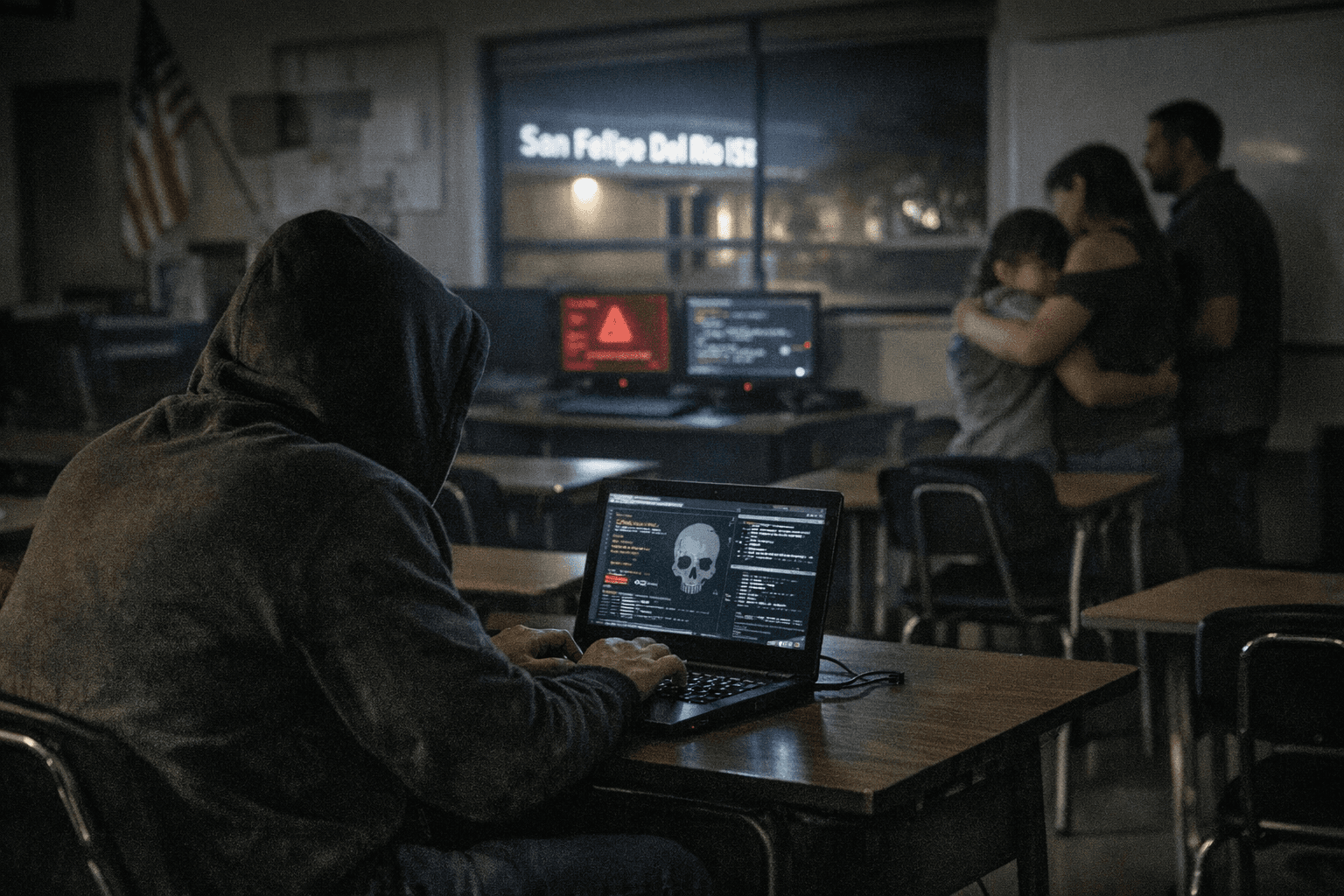
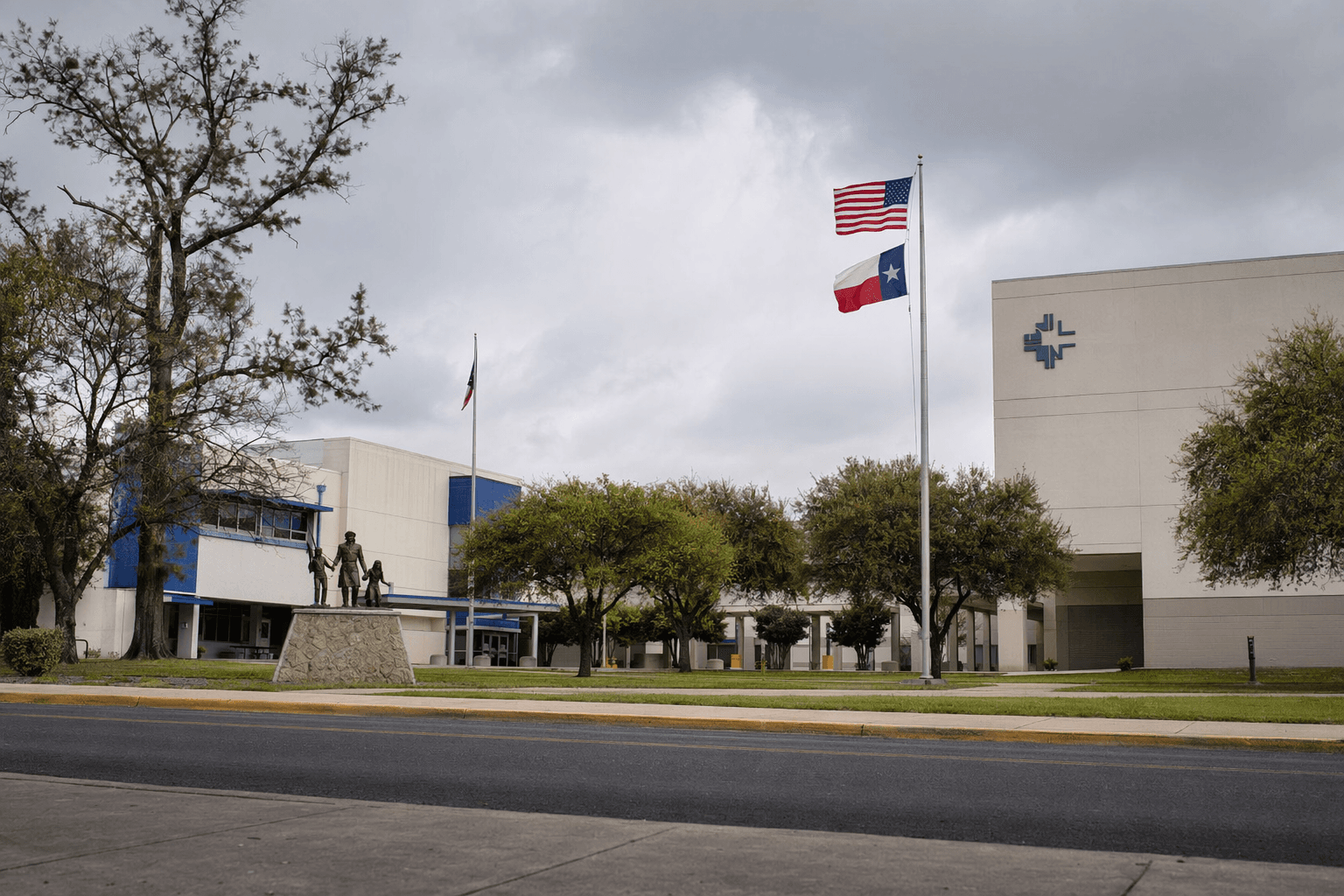
The gap between a March 19 network outage at San Felipe Del Rio CISD and a March 31 dark-web posting by WorldLeaks tells the full story: student records, staff payroll files, and family contact information for roughly 10,500 students and their families are now in the hands of an extortion group that has already hit Nike, Dell, and the City of Los Angeles.
WorldLeaks posted its claim at 9:09 a.m. on March 31, naming San Felipe Del Rio CISD as its latest victim and threatening to publish stolen data within one to two days. That deadline has now passed, putting the district's files at risk of full public exposure.
The group, formerly known as Hunters International before rebranding in January 2025, does not encrypt files. Its model is pure data theft and public extortion: steal sensitive records, post a countdown on a dark-web leak site, and pressure organizations to pay by threatening exposure. Operating what cybersecurity researchers call an extortion-as-a-service platform, WorldLeaks has amassed at least 117 confirmed victims since emerging from the same lineage as the Hive ransomware operation.
What is at stake locally is specific. Student records in a K-12 district typically include enrollment details, grades, disciplinary histories, special-education status, and Social Security numbers collected during registration. Staff payroll data carries direct-deposit banking information, SSNs, and home addresses. Family contact files compile phone numbers, home addresses, and emergency contacts for every enrolled child.
That combination creates direct identity-theft pathways. Criminals using stolen child SSNs can open fraudulent credit accounts that go undetected for years because minors rarely monitor credit. Payroll data enables fraudulent tax filings. Family contact lists fuel targeted phishing calls and texts that impersonate the district, often claiming a child is ill or in trouble, to extract money or additional personal information.
The district first acknowledged a disruption on March 19, when it released a statement saying it was restoring in-network systems and monitoring for suspicious activity after administrators detected anomalous email behavior. In a subsequent post, the district confirmed that "most all in-network systems, including internet and phone systems, went down." Technology staff partnered with a Regional Security Operations Center to investigate and restore critical infrastructure; schools maintained normal operations throughout.
Place a credit freeze on your child's file with all three major bureaus now. For minors, the freeze requires a manual request with documentation to Equifax, Experian, and TransUnion, but it blocks anyone from opening new credit in that child's name. Staff should freeze their own files and alert their banks to potential account-number exposure. Change any password that matches one used for district portals or email. Treat any call, text, or email claiming to be from SFDRCISD with heightened skepticism over the next 30 days, particularly messages requesting personal details, login credentials, or payment.
For direct information on the incident, contact Director of Technology Integration and Communication Services Rene Luna at (830) 778-4164 or rene.luna@sfdr-cisd.org. Superintendent Dr. Carlos H. Rios can be reached at (830) 778-4007 or carlos.rios@sfdr-cisd.org.
The district has not yet publicly confirmed what data, if any, was exfiltrated. WorldLeaks, with 117 known victims on its ledger, has not been known to make empty claims.
Know something we missed? Have a correction or additional information?
Submit a Tip