Canvas cyber incident disrupts Yuma County schools, raises privacy concerns
Canvas was taken offline after a cyberattack, briefly cutting off Yuma County classrooms and putting student messages, IDs and emails in the privacy spotlight.
A Canvas cyber incident rattled Yuma County schools by interrupting one of the main platforms teachers use to post assignments, share notes and collect work, while also raising fresh questions about student privacy. For families who depend on Canvas for daily classroom updates, the disruption was more than a software hiccup. It threatened access to grades, course messages and the routine communication that keeps schoolwork moving.
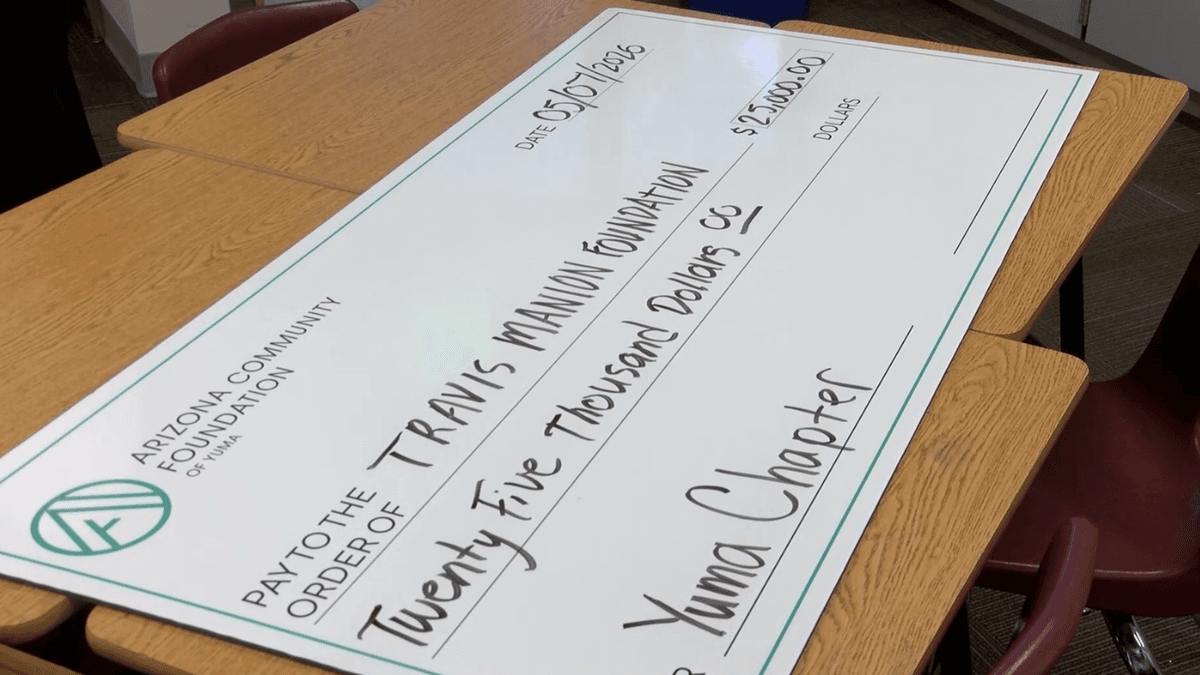
Instructure, the company behind Canvas, placed the platform in maintenance mode on May 7 and later restored it for most users that night. ABC News reported that Instructure first detected unauthorized activity on April 29 and identified additional unauthorized activity on May 7. The company said the data involved included names, email addresses, student ID numbers and messages, while passwords, dates of birth, government identifiers and financial information were not found to be involved.
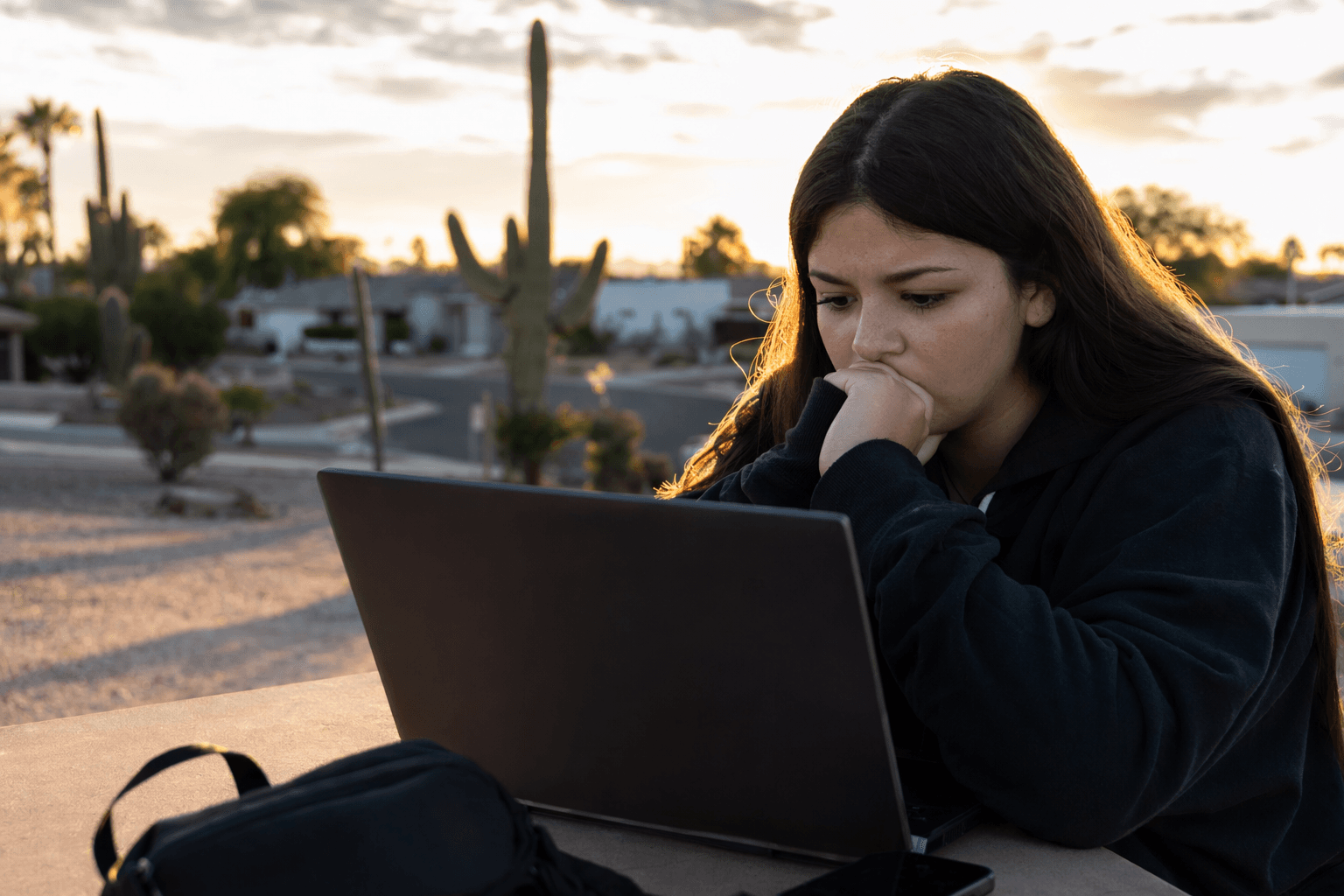
The local impact matters because Yuma County schools rely on Canvas as part of everyday instruction, not as an optional extra. When the system went down, students and parents could lose access to class announcements, homework postings, grading updates and direct messages from teachers. Even after the platform came back online, districts and campuses had to reckon with the possibility that notices, deadline changes or account checks may still be needed if any local users were among those affected.
The scale of the attack reached well beyond Arizona. PBS reported that the hacking group ShinyHunters claimed responsibility, and said nearly 9,000 schools worldwide were affected. TechRepublic reported the group claimed data tied to 275 million users and nearly 9,000 schools was stolen. In Arizona, World Online reported that Arizona State University, ASU Prep, Northern Arizona University and the University of Arizona Global Campus were affected, while Grand Canyon University said it was not impacted because it does not use Canvas.

Instructure said its precautionary steps include enforcing multi-factor authentication on privileged accounts, reviewing admin access and rotating API tokens or keys where applicable. For Yuma County families, the practical next move is to watch district notices closely, change any password that may have been reused on other sites, turn on multi-factor authentication where it is offered, and check Canvas messages, grades and assignments for anything unusual. A platform used for daily schoolwork can recover quickly; the questions around who saw what, and which local families may need follow-up notices, can last much longer.
Know something we missed? Have a correction or additional information?
Submit a Tip