AI Recruiting Startup Mercor Confirms Breach Tied to LiteLLM Compromise
Lapsus$ claims 4TB stolen from Mercor via poisoned LiteLLM packages, exposing resumes, video interviews, and KYC documents of job-seekers on the AI hiring platform.

Mercor, the AI recruiting startup valued at $10 billion, confirmed it was caught in a cascading supply chain attack after extortion group Lapsus$ claimed to have stolen roughly 4 terabytes of data from its systems, including contractor resumes, recorded video interviews, and identity verification documents. The breach traces back to a March 24, 2026 compromise of the open-source LiteLLM Python library on PyPI, a package downloaded roughly 3.4 million times per day.
The vector was precise: a cybercriminal group called TeamPCP obtained the LiteLLM maintainer's PyPI credentials through a prior compromise of Trivy, an open-source security scanner used in LiteLLM's own CI/CD pipeline. TeamPCP then uploaded two malicious package versions, 1.82.7 and 1.82.8, that embedded a credential stealer targeting SSH keys, cloud credentials, and authentication secrets. The packages were live for approximately three hours before PyPI quarantined them, but the window was enough. Any development environment that installed or upgraded LiteLLM between roughly 10:39 and 16:00 UTC on March 24 was potentially exposed. Version 1.82.8 was particularly aggressive, introducing a .pth file that triggered the malicious payload at ordinary Python interpreter startup, not just on import.
Mercor spokesperson Heidi Hagberg confirmed the company had moved promptly to contain and remediate the situation, describing Mercor as "one of thousands of companies" affected by the LiteLLM compromise. "We are conducting a thorough investigation supported by leading third-party forensics experts," Hagberg said, adding that the company would "continue to communicate with our customers and contractors directly as appropriate." Hagberg declined to answer whether any customer or contractor data had been accessed, exfiltrated, or misused, or whether the incident was directly connected to the Lapsus$ extortion claim.
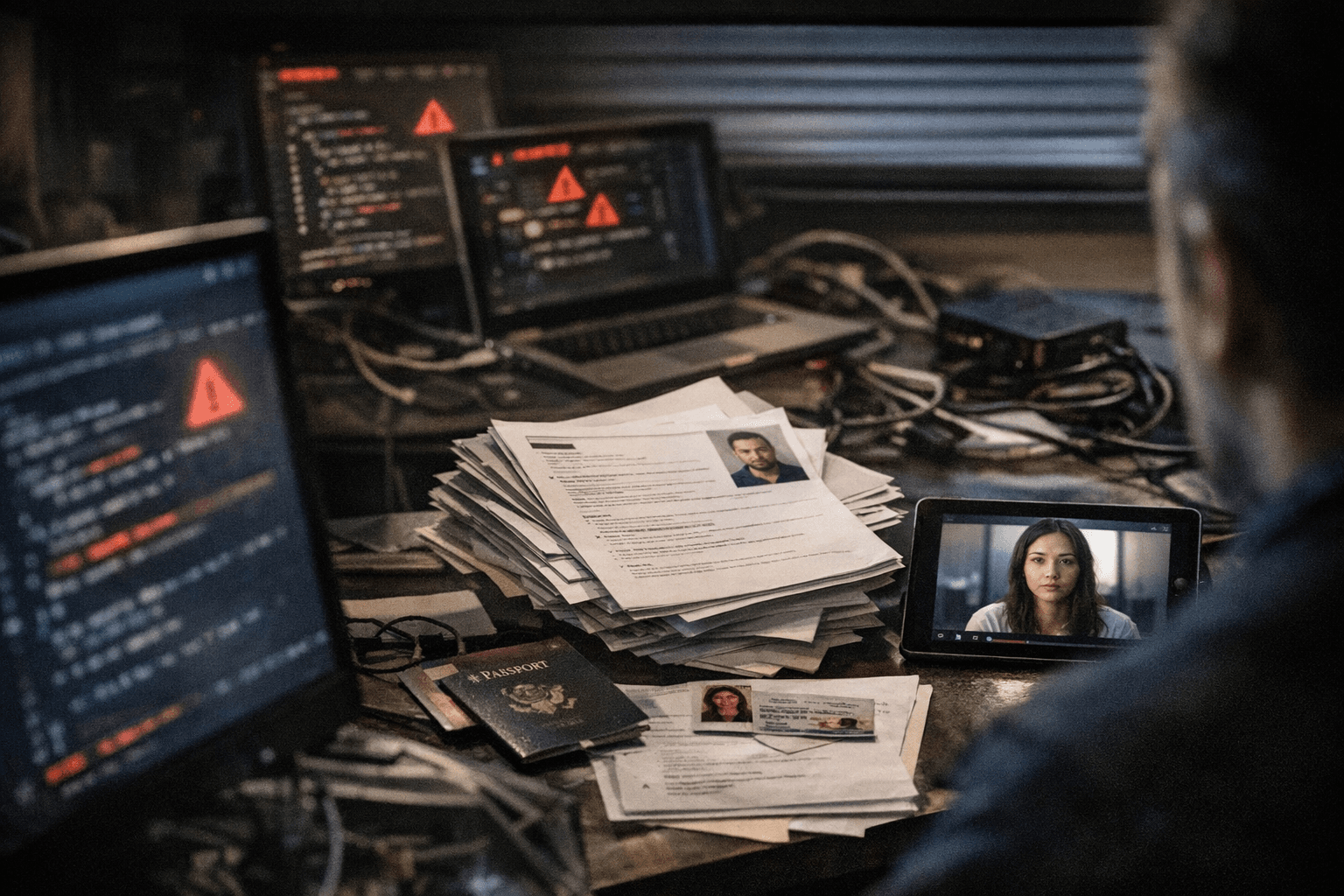
For job-seekers and contractors on Mercor's platform, the categories of data at risk are significant. Lapsus$ released a sample that included Slack data, ticketing records, and two videos purportedly showing conversations between Mercor's AI systems and contractors. The group claims the full haul includes 211 gigabytes of database records containing resumes and personal information, nearly 3 terabytes of stored files including video interviews with face and voice data, and KYC documents and passports. Lapsus$ also claims it gained access to Mercor's Tailscale VPN environment. Founded in 2023, Mercor works with OpenAI and Anthropic to source specialized domain experts, including scientists, doctors, and lawyers, and processes more than $2 million in daily payouts.
The mechanics of the attack illustrate exactly how a single compromised open-source dependency can cascade through an entire technology stack. LiteLLM serves as a unified proxy, routing AI application traffic across more than 100 model providers. Its deep integration across thousands of AI systems meant that TeamPCP's poisoned packages functioned less like targeted malware and more like an infrastructure trap. The related Trivy compromise demonstrates how attackers are now deliberately daisy-chaining open-source projects: compromising a security scanner to reach a developer tool, then using that tool to reach production environments.
For any startup running AI workloads, the Mercor breach illustrates three controls that should be non-negotiable. Dependency pinning, locking package versions to a specific cryptographic hash rather than a floating version range, would have blocked the malicious upgrade from reaching production automatically. Regular software composition analysis audits, using tools that flag newly published versions against known-good baselines, would have surfaced TeamPCP's changes within the three-hour window they were live. And secrets management hygiene, ensuring that developer credentials, SSH keys, and cloud tokens are scoped, rotated, and isolated from CI/CD pipelines, removes the upstream foothold that TeamPCP exploited in the first place. LiteLLM itself has since changed its compliance process, moving from Delve to Vanta following the incident.
The connection between TeamPCP's infrastructure attack and Lapsus$'s extortion claim remains formally unresolved. Investigators have not publicly explained how Lapsus$ obtained data allegedly exfiltrated through TeamPCP's campaign. What is clear is that for a recruiting platform holding biometric video interviews and government-issued identity documents, the answer to that question carries far more than reputational weight.
Know something we missed? Have a correction or additional information?
Submit a Tip

