CareCloud Reports Hackers Accessed Patient Health Records for Eight Hours
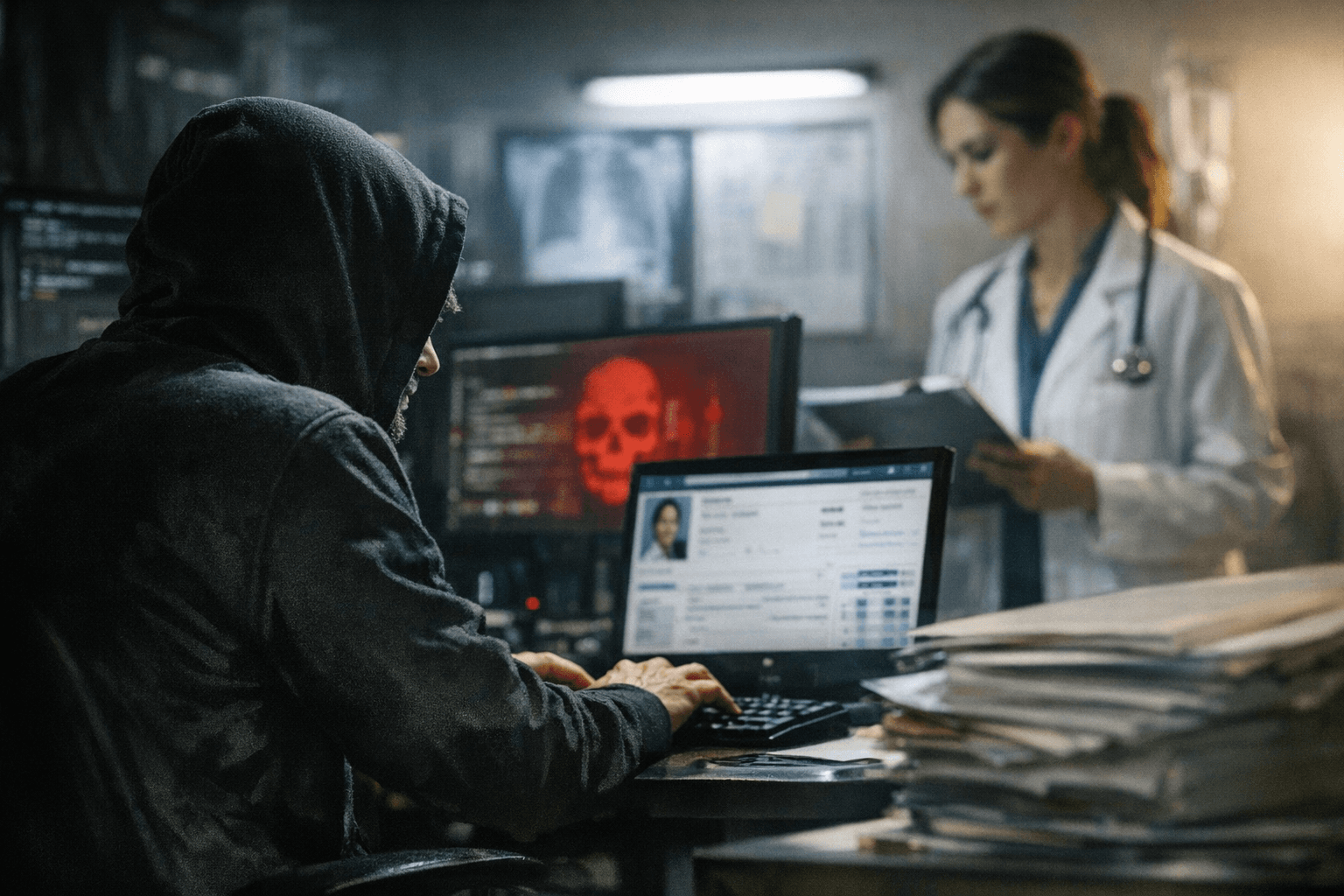
Hackers accessed patient health records stored in one of CareCloud's six EHR environments for roughly eight hours on March 16, and the company has yet to confirm whether data was stolen.

An unauthorized intruder spent approximately eight hours inside one of CareCloud's six patient electronic health record environments on March 16 before the Somerset, New Jersey-based health technology company restored systems that same evening, according to a March 27 SEC filing. The company has not yet determined whether any patient data was taken.
CareCloud, which provides EHR and practice management services to more than 45,000 physicians and clinics that collectively serve millions of patients, said the breach was contained to a single environment within its CareCloud Health division. Investigators believe the intruders are no longer in the network after restoration steps taken the same day, and the company said its other platforms, divisions, and data environments were not affected.
What the company cannot yet say is whether any patient data was stolen. CareCloud said it is still assessing whether data was accessed or exfiltrated, including the categories and volume involved, and it has not disclosed how many patients or providers may be affected. The company also has not clarified whether the compromised environment contained backups or was logically isolated from other systems, nor confirmed whether the affected environment was among the data CareCloud believes is hosted on Amazon Web Services.
In response to the breach, CareCloud engaged outside cyber-response specialists, notified its cyber insurer, and reported the matter to law enforcement. Remediation is underway.
The eight-day gap between detection and the company's materiality determination reflects the timeline of corporate disclosure under current securities rules: CareCloud notified investors on March 24 that it considered the breach material and filed a formal SEC disclosure on March 27. The company said it did not expect the incident to materially affect its financial position, but deemed the matter significant under securities rules because of the sensitivity of potentially affected patient information and the possibility of remediation, notification, legal, regulatory, and reputational consequences.
That framing leaves patients in a holding pattern. Electronic health records are among the most prized targets in cybercrime, containing Social Security numbers, insurance data, diagnoses, and medication histories that retain value for bad actors over years. Security experts have warned that EHR breaches can enable identity theft, insurance fraud, and targeted extortion. For providers, disruption to billing and clinical workflows is a documented consequence of vendor-level compromises. Additional disclosures or patient notifications could follow if the review confirms that data was accessed or exfiltrated; state breach notification laws may require CareCloud to notify individuals and regulators depending on what the investigation ultimately finds.
The incident fits a broader pattern that has been accelerating across the healthcare sector. Recent cyberattacks hit medical-technology companies Stryker and Masimo, underscoring how software and service providers represent a single point of failure for the practices that depend on them. The 2024 Change Healthcare attack remains the starkest example of that dynamic, cascading across thousands of practices and disrupting care nationwide. CareCloud's footprint of more than 45,000 providers means the final scope of this breach could be substantial, though the company has not responded to further requests for comment as the investigation continues.
Know something we missed? Have a correction or additional information?
Submit a Tip

