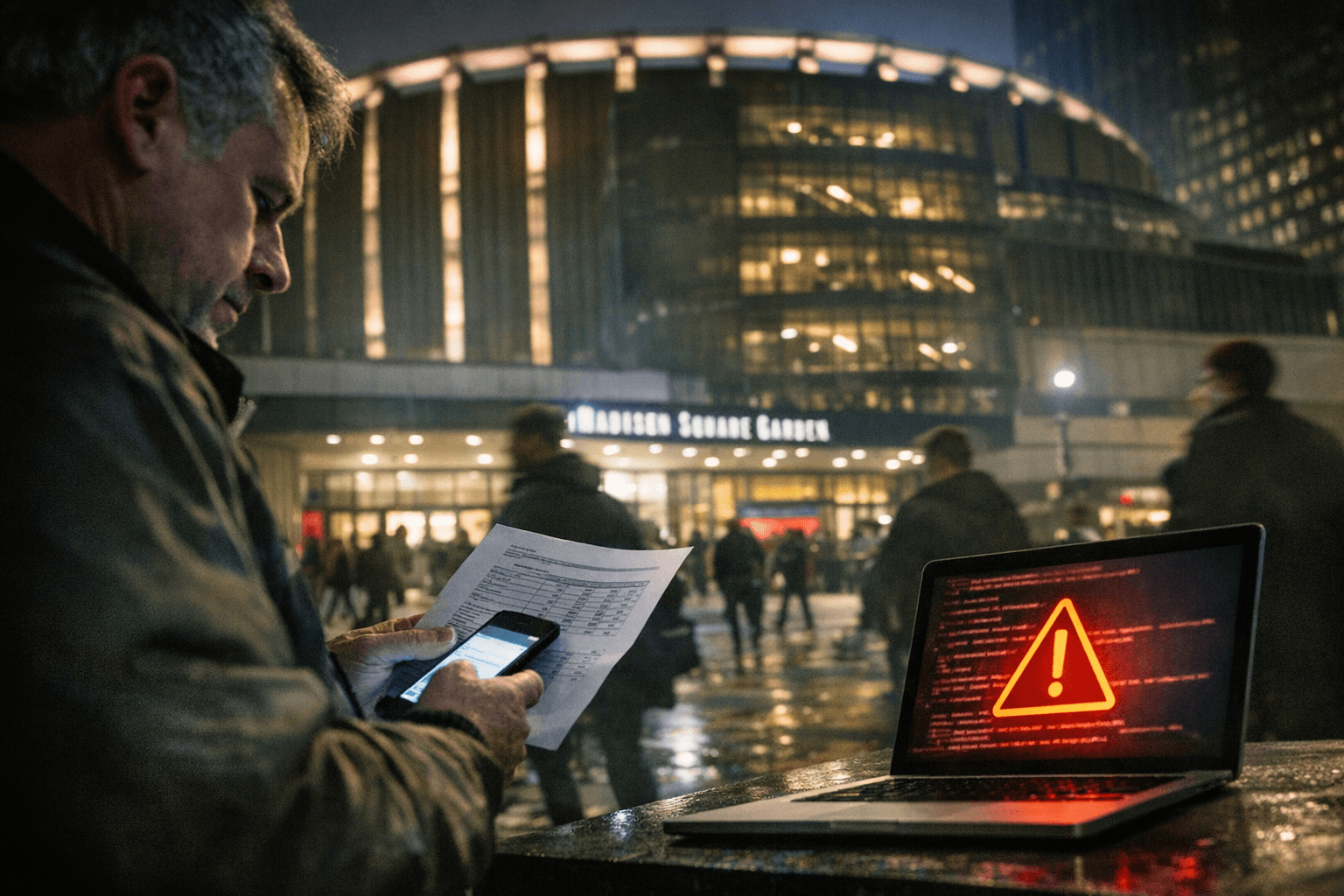
Madison Square Garden Entertainment notifies 131,070 people after Oracle EBS breach
Madison Square Garden Entertainment disclosed a vendor-hosted Oracle EBS intrusion and began notifying 131,070 affected individuals, exposing names, SSNs and payroll records.

Madison Square Garden Entertainment Corp. began notifying 131,070 people that personal information held in a vendor-hosted Oracle E‑Business Suite instance was accessed by an unauthorized party, UpGuard reported, placing the company among a wave of victims tied to an Oracle zero-day campaign.
Investigators and reporting outlets trace the intrusion to August 2025, although sources differ on the precise window and discovery date. Comparitech quoted an MSG notice saying, "Oracle notified its customers that a previously undisclosed condition in the application had been exploited by an unauthorized person to gain access to data from the application" and that "the investigation determined in late November 2025 that an unauthorized person gained access to some data from the application in August 2025." UpGuard and ClassActionU, by contrast, list a broader intrusion period from August 10 to October 21, 2025, and report the incident was discovered on December 16, 2025.
UpGuard's summary lists the total individuals affected as "131,070" and identifies the exploited vulnerability as CVE‑2025‑61882, attributing the operation to the Clop ransomware group in a key facts section. Comparitech reported that Clop claimed responsibility in November 2025 and added MSG to its data leak site, while noting MSG has not publicly acknowledged Clop's claim. UpGuard's post contains a contradictory line stating "No specific threat actor has been identified in connection with this security event," underscoring uncertainty in public attributions.
The exposed records include full names, physical addresses, Social Security numbers and business files tied to hiring and payments, according to UpGuard and ClassActionU. SecurityWeek reported that MSG told the Maine Attorney General's Office that 11 Maine residents were affected, and Databreachdaily said MSG reported the incident to state authorities in California and Maine. Databreachdaily also reported that the unnamed third‑party vendor implemented Oracle's recommended mitigations and that law enforcement has been notified.
MSGE is offering at least one year of complimentary credit monitoring and identity protection through Cyberscout, a TransUnion company, as reported by ClassActionU and Databreachdaily. ClassActionU and UpGuard also encouraged affected people to activate those services and consider safeguards such as credit freezes and enhanced account authentication, steps commonly advised after large SSN exposures.
The incident sits within a broader campaign that Comparitech described as expansive: the outlet reported Clop claimed 456 ransomware attacks in 2025, and that 31 confirmed breaches from that campaign accounted for roughly 3.75 million compromised records. Other named victims included universities and technology firms, a pattern that highlights the systemic risk of zero-day exploits in widely used enterprise applications.
The case raises policy and governance questions about third-party risk management, incident disclosure timelines and regulatory oversight. State breach-notification rules require timely reporting and often trigger enforcement or litigation; ClassActionU has signaled potential class-action interest on behalf of affected individuals. Journalists and security analysts say verification of the 131,070 figure, the identity of the managing vendor, and whether any ransom was paid remain outstanding.
For consumers and officials, the episode underscores two practical demands: companies must disclose clearer, source-attributed timelines and remediation steps after supply-chain or vendor-hosted breaches, and regulators must assess whether current reporting requirements produce enforceable accountability.
Know something we missed? Have a correction or additional information?
Submit a Tip