ShinyHunters and extortion groups publish massive data dumps, U.S. targets hit
Extortion syndicates published and threatened to release stolen troves, forcing consumer brands, universities and tech firms into emergency response and public disclosures.
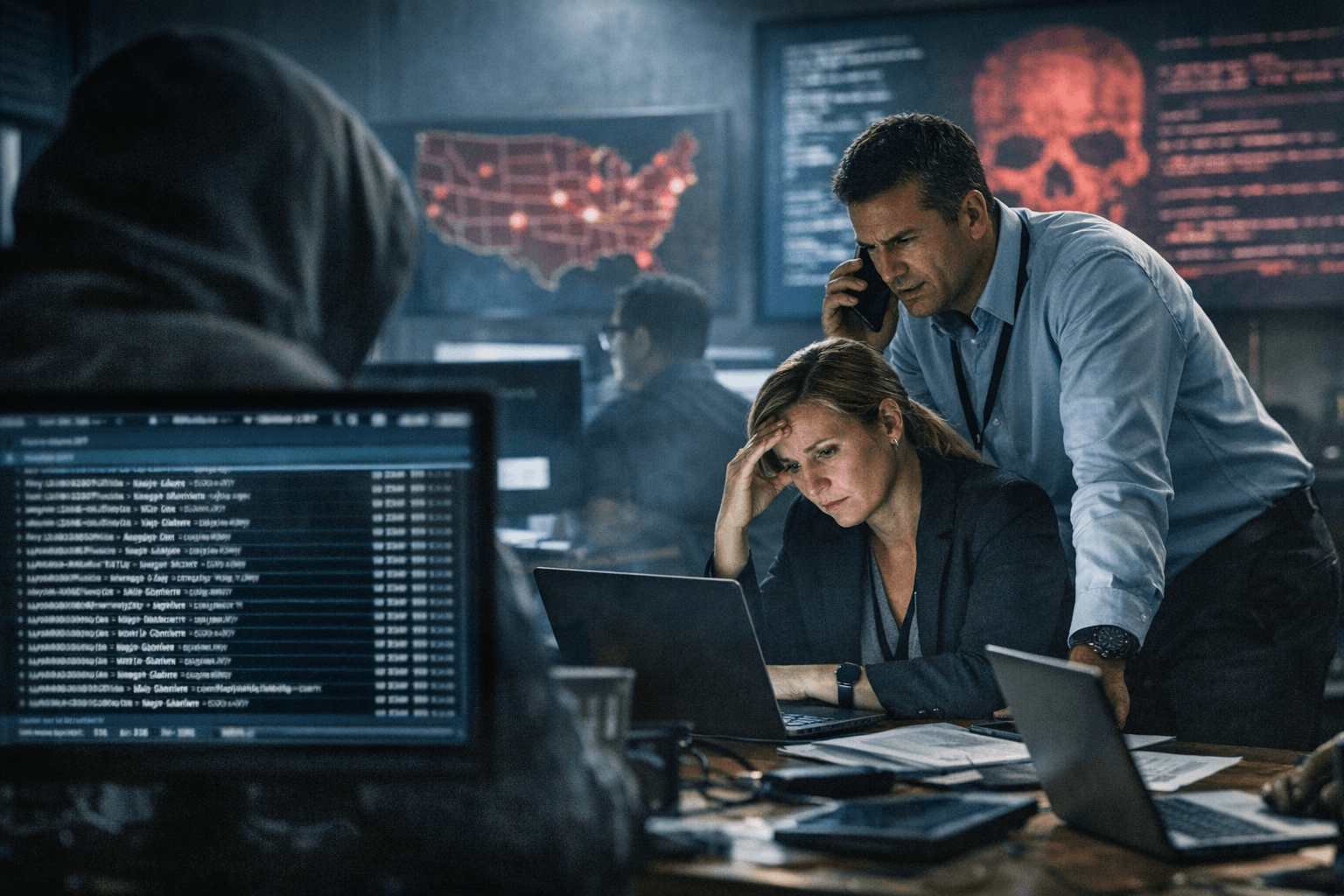
Extortion syndicates including ShinyHunters intensified a broad campaign of public data dumps and publication threats on Feb. 25, 2026, after a month already marked by multiple, high-impact intrusions. The disclosures targeted consumer brands, education institutions and technology firms and forced affected organizations into emergency containment, disclosure and remediation actions.
The campaign revived a familiar playbook: criminals exfiltrate customer, student and employee records, demand payment, then escalate by posting portions of the material to public leak sites and criminal forums or threatening full releases. The tactic converts stolen files into immediate leverage, amplifying reputational damage and triggering regulatory reporting obligations for organizations that hold personal or sensitive data.
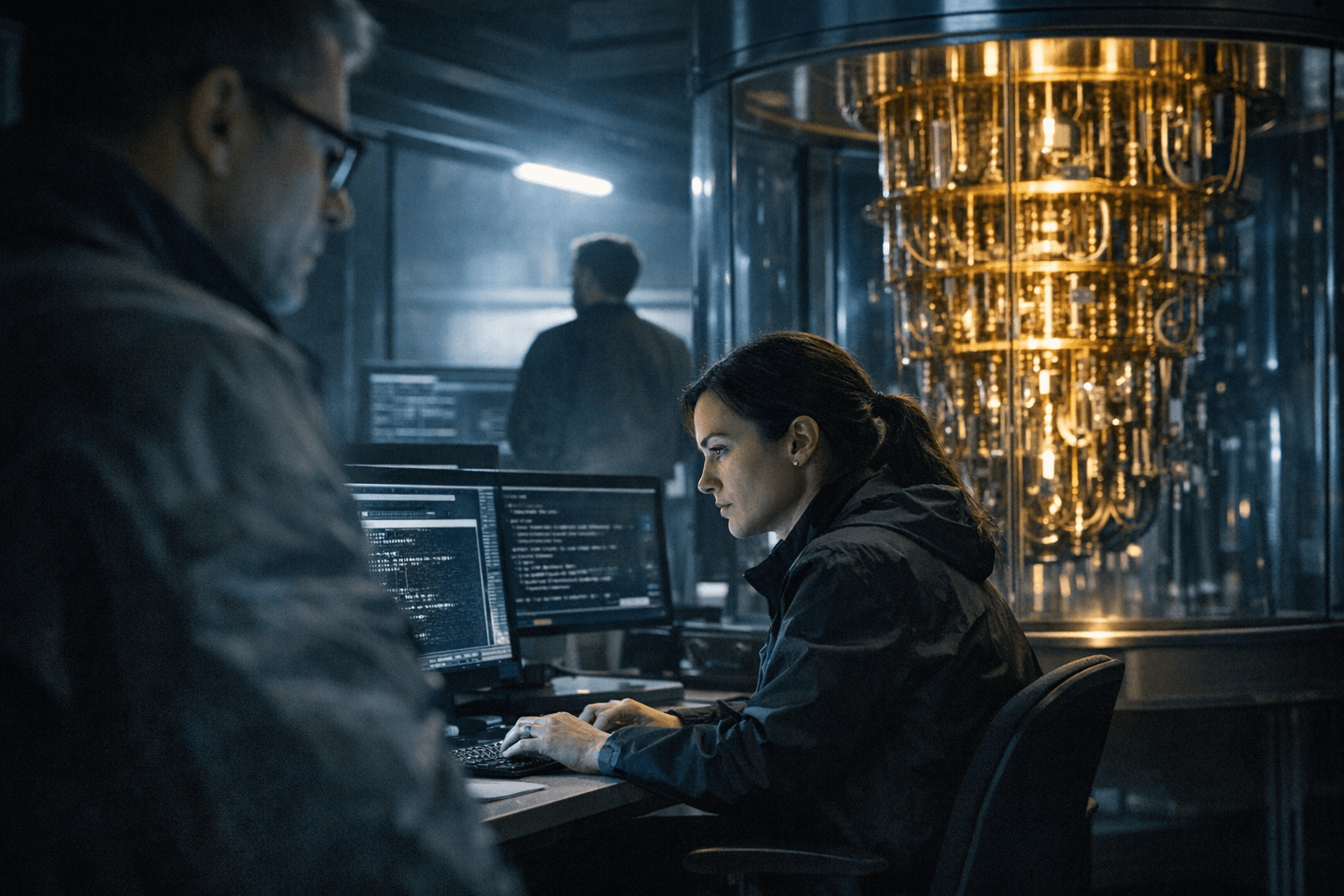
Operational effects were immediate. Security teams at affected companies scrambled to revoke credentials, isolate compromised systems and notify customers and students. Legal and compliance units began preparing breach notice letters and regulatory filings in multiple jurisdictions. For education institutions, exposure of student and staff records raised risks of identity theft and possible misuse of academic data. For technology firms, disclosure of internal project files and credentials created cascading risks for third-party partners and cloud-hosted services.
The surge compounds a taxing landscape for incident response. Organizations face not only the costs of forensic investigation and system recovery but also potential regulatory penalties and class-action litigation. Public disclosures compel firms to reveal limited details while they investigate, a process that can further erode customer trust and market value. For smaller institutions with lean IT staffs, the disruption of a single leak can force weeks of remediation and long-term investments in security architecture.
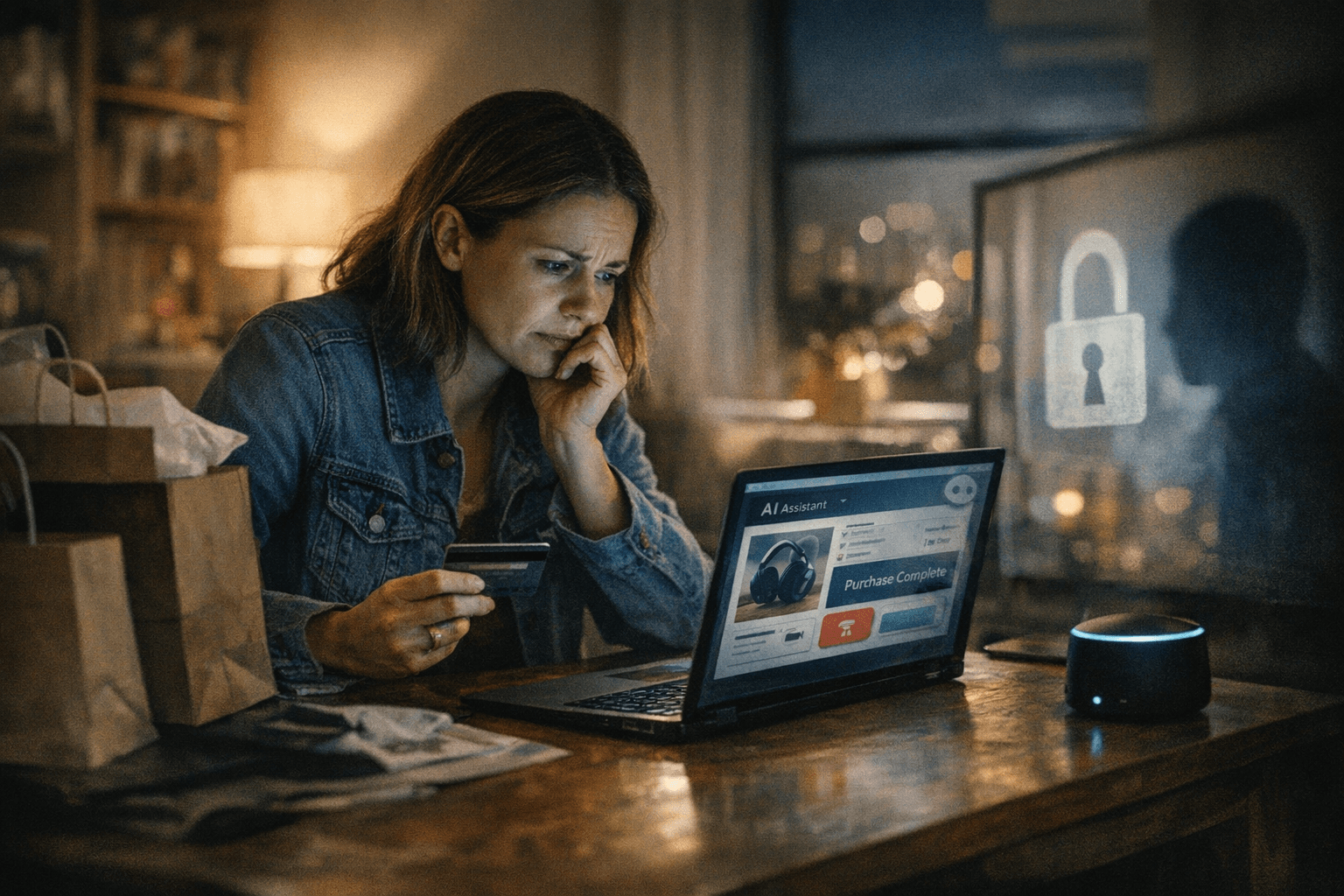
Law enforcement and cybersecurity practitioners say the economic incentive behind these operations remains strong: stolen data can be monetized through sale, extortion or secondary fraud. Platforms that host leaks and forums that facilitate auctions or solicit ransom payments have normalized a marketplace where personal and corporate data are traded openly, pressuring victims to consider payment to limit exposure even when payment does not guarantee deletion of stolen materials.
The societal consequences extend beyond immediate victims. Widespread publication of credential dumps and personal records fuels phishing, account takeover and financial fraud, raising costs for banks, insurers and consumers. Educational records exposed in data dumps can have lifelong consequences for students and staff, and may undermine confidence in institutions that house sensitive developmental and medical information.
Defensive measures remain standard but critical: rapid detection and containment, multifactor authentication, credential rotation, network segmentation and robust backup strategies. Equally important are data-minimization practices and legal preparedness for timely breach notification. Public-private cooperation and pressure on hosting platforms to remove leak material quickly can blunt some harms, but experts warn these measures will not eliminate the incentive structure that makes extortion profitable.
As the campaign continues, companies and institutions must assume their records are potential targets and act accordingly. The immediate consequence of Feb. 25 is not merely another series of disclosures; it is a reminder that mass data exfiltration and public shaming have become persistent, operational threats that require sustained, expensive defenses and rapid, transparent responses.
Sources:
Know something we missed? Have a correction or additional information?
Submit a Tip