Critical DoS Flaw in libp2p-rust Gossipsub Triggers Panics Before Version 0.49.3
CVE-2026-33040 lets unauthenticated attackers crash any libp2p-rust Gossipsub node by sending a single PRUNE message with a u64::MAX backoff value.
A denial-of-service vulnerability in the official Rust implementation of libp2p has given unauthenticated remote attackers a trivially repeatable path to crashing any application that exposes a Gossipsub listener, and the fix landed only in version 0.49.3 of the libp2p-gossipsub crate.
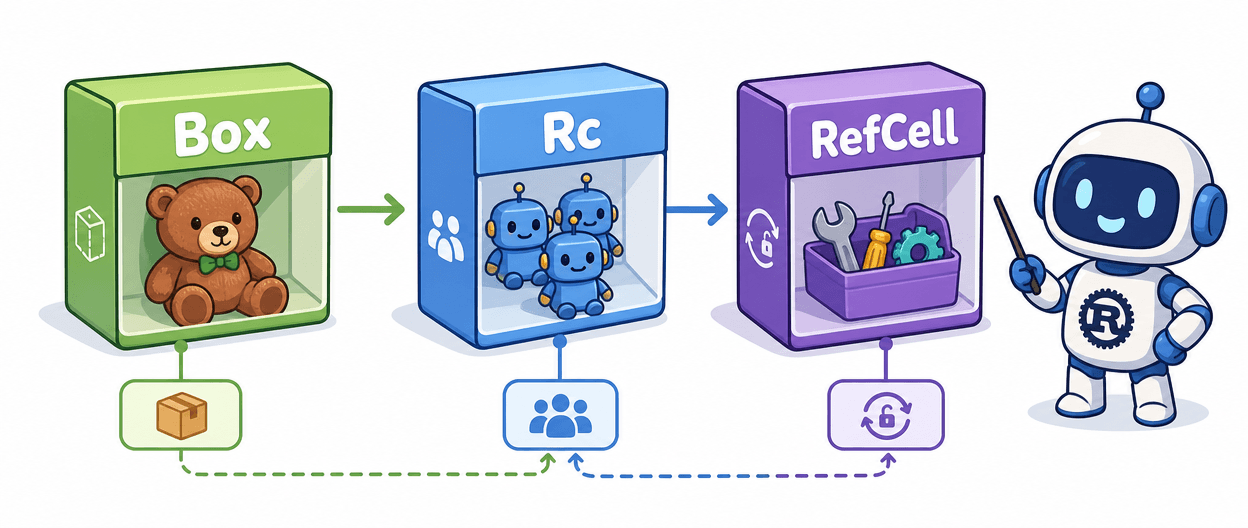
The bug, tracked as CVE-2026-33040, lives in how Gossipsub handles PRUNE control messages. When a peer gets pruned from a mesh, Gossipsub uses a backoff value to decide how long that peer stays excluded. In versions prior to 0.49.3, the implementation accepted that backoff value directly from the incoming message and fed it into time arithmetic using Rust's Duration and Instant types without any bounds checking. Send a PRUNE message with an extremely large backoff, say u64::MAX, and the arithmetic overflows or wraps around. The overflow triggers a panic in the networking state machine and the process dies.
What makes this particularly ugly is the exploitation profile. No authentication is required. No prior relationship with the target node is needed. An attacker only needs to reach the service port over a normal libp2p connection, send the crafted PRUNE message, watch the node go down, then reconnect and replay the same message to keep it down. The attack is as repeatable as the attacker has patience for.
The blast radius extends well beyond any single application. libp2p is the networking substrate for a significant slice of the blockchain and decentralized storage ecosystem. Any project running libp2p-rust with Gossipsub enabled and using the affected backoff-handling path is exposed. That includes infrastructure components where availability isn't just a quality-of-life concern but a protocol correctness requirement.
The root cause is a classic input validation gap that Rust's type system doesn't automatically prevent: the code trusted attacker-controlled numeric input and passed it directly into arithmetic on Duration and Instant values. Rust panics on overflow in debug builds by default, but in production the behavior depends on compile flags and context. Either way, the networking state machine hits an unrecoverable state.
The fix is straightforward: update the libp2p-gossipsub crate to version 0.49.3. No configuration workaround or partial mitigation is documented in the available advisories. If you're running any libp2p-rust deployment with Gossipsub and haven't pinned to 0.49.3 yet, that's the only action that closes the hole. Check your Cargo.lock, not just your Cargo.toml, to confirm the resolved version is actually 0.49.3 and not an older dependency pulled in transitively by another crate.
Know something we missed? Have a correction or additional information?
Submit a Tip