Embedded World 2026 Puts Rust in the Spotlight for Automotive Safety Systems
Rust is taking center stage at Embedded World 2026 in Nürnberg, where a session on automotive safety and a live toolchain qualification demo are making the case for production-ready deployment.

Rust is getting a serious audition on the automotive safety stage this week in Nürnberg. Embedded World 2026, running March 10–12 at the Nuremberg exhibition center, has made the language a recurring theme across conference sessions and exhibitor floors, with presenters and toolchain vendors alike treating it not as a curiosity but as a genuine candidate for safety-critical deployment.
The most direct address comes from Sjoerd van der Zwaan, whose talk "Rust on the Road: Navigating Challenges and Opportunities in Automotive" is scheduled for March 11 at 13:45 on the embedded world Conference program. The session targets the practical tension between growing industry interest in Rust and the certification realities of safety-critical automotive development, where language choice carries regulatory weight alongside engineering merit.
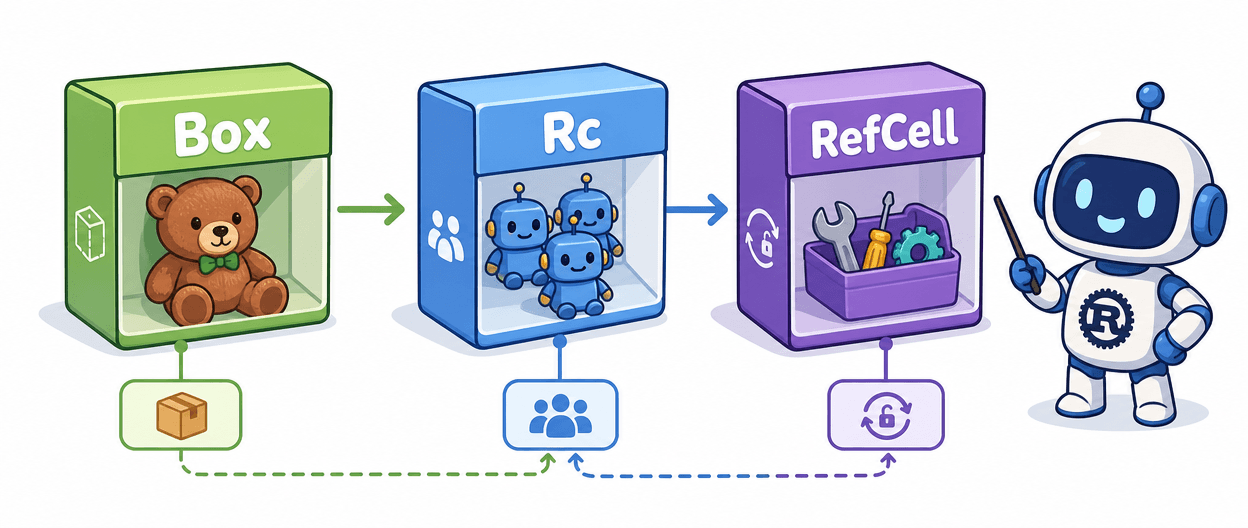
The technical case for Rust in this domain is well-rehearsed but still worth stating plainly: performance, type safety, concurrency guarantees, and memory safety make it a natural fit for the kinds of embedded use-cases where a bad pointer dereference can mean more than a crash. The harder problem, and the one getting real floor time at this show, is what happens when Rust code doesn't live in isolation. More embedded projects are migrating critical subsystems from C to Rust while keeping large existing C codebases in place, and that hybrid architecture introduces a specific failure mode: untrusted C code, combined with trusted Rust code, can crash or compromise the Rust side indirectly. The concept that keeps coming up in session descriptions is "freedom-from-interference," the requirement that untrusted code portions cannot affect the behavior of trusted ones. Achieving it in mixed-criticality systems means reaching for partitioning tools borrowed from automotive and avionics: separation kernels, time-triggered scheduling, and hardware-enforced isolation. Hypervisors are the common mechanism for application partitioning in practice, though the underlying memory separation principle is also present in traditional OS process management.
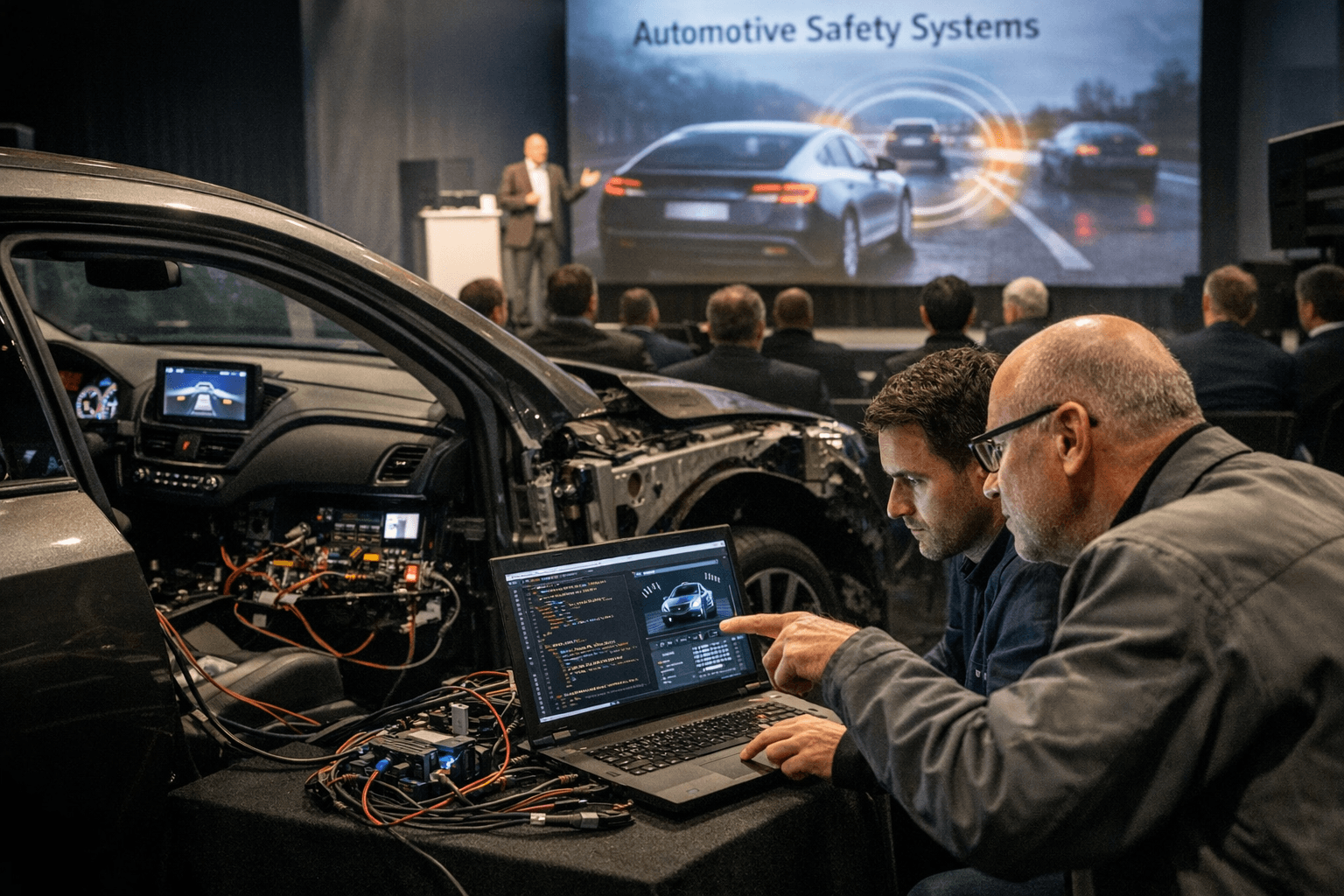
On the exhibitor floor, Solid Sands B.V. is bringing the toolchain qualification angle to Hall 4, Booth 4-548, where the Amsterdam-based company is sharing a stand with software verification specialists BUGSENG. Their joint demonstration focuses on Continuous Qualification of C and C++ toolchains implemented in practice, pairing Solid Sands' compiler and library qualification expertise with BUGSENG's Eclair technology. The booth conversations are oriented around maintaining qualified toolchains, supporting continuous qualification workflows, and managing compliance across automotive, industrial, and emerging autonomous systems. Solid Sands' positioning in this space builds on its recent acquisition of the Plum Hall compiler, extending its qualification coverage. The company's stated direction is toward lifecycle assurance: "Our technology continuously evaluates the safety envelope of each build against its baseline qualification, automatically re-qualifying when appropriate or alerting teams when intervention is required, enabling organizations to maintain confidence in their toolchains over time."
That framing captures something real about where the embedded Rust conversation is actually headed. Getting the language into a safety-critical codebase is one problem; keeping the toolchain demonstrably qualified across every subsequent build is another, and arguably the less glamorous one that determines whether any of this lands in a shipping vehicle. The combination of language-level adoption discussions and continuous toolchain qualification infrastructure on display at Embedded World 2026 suggests the ecosystem is moving on both fronts simultaneously.
Know something we missed? Have a correction or additional information?
Submit a Tip