RustSec flags steamworks panic bug that can crash game authentication
A panic in steamworks can take multiplayer auth offline when a bad ticket hits ValidateAuthTicketResponse_t, and versions before 0.13.1 need an upgrade.
A RustSec alert is now putting a sharp edge on one of the most common Steam integration paths in Rust games: authentication can panic, and that panic can knock a client or server offline. The advisory, RUSTSEC-2026-0121, says the steamworks crate can fail while processing raw ValidateAuthTicketResponse_t callback data when m_eAuthSessionResponse is k_EAuthSessionResponseAuthTicketNetworkIdentityFailure.
The practical risk is denial of service for game clients and servers that call begin_authentication_session to validate players. In the affected flow, a malicious client can present an authentication ticket whose network identity does not match the verifier’s network identity, and that mismatch can trigger the panic. RustSec reported the issue on May 5, 2026 and issued the advisory on May 6. GitHub later published the same bug as GHSA-g588-cjg3-6g78 on May 11, rating it Moderate with a CVSS v4 base score of 6.3.
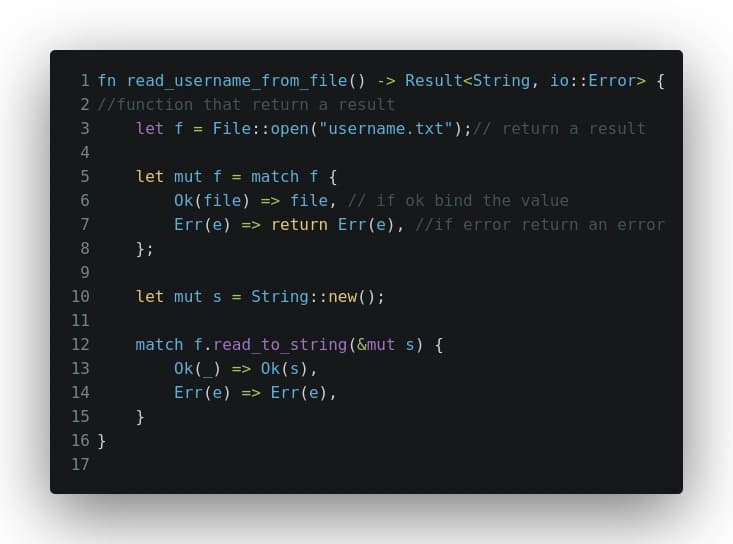
The affected entry points are steamworks::Client::process_callbacks, steamworks::Client::register_callback, steamworks::Server::begin_authentication_session, steamworks::User::begin_authentication_session, and steamworks::ValidateAuthTicketResponse::from_raw. Any deployment pinned to steamworks before 0.13.1 is exposed, including 0.13.0. The fix is straightforward: move to 0.13.1 or later.
Valve’s own Steamworks documentation shows why the bug lands in such a sensitive spot. BeginAuthSession triggers a ValidateAuthTicketResponse_t callback, and identity is not confirmed until that callback comes back with success. Steamworks also uses session tickets for peer-to-peer multiplayer sessions and for listen and dedicated servers, so this is not some obscure admin path. It sits right in the middle of the authentication handshake that many Rust multiplayer projects rely on to decide whether a player gets in.
The good news is that this is not a memory-corruption problem. The bad news is that callback-driven auth code that assumes Steam will always return a benign state can still fall over hard, right when a lobby is filling up or a server is validating a join. For anyone shipping a networked game with steamworks-rs, upgrading past 0.13.1 is the fastest way to close the door on the crash.
Know something we missed? Have a correction or additional information?
Submit a Tip