Wasmtime Patches 12 Security Flaws, 11 Found Using LLM-Based Analysis Tools
Wasmtime's biggest-ever advisory batch fixed 12 flaws, with 11 discovered via LLM-based tools in a three-week sprint by maintainers from Mozilla, UCSD, Akamai, and F5.
The Wasmtime project published the largest single batch of security advisories in its history, and the story behind how 11 of 12 vulnerabilities were discovered may matter as much as the patches themselves.
Bytecode Alliance maintainers released patched versions 43.0.1, 42.0.2, 36.0.7, and 24.0.7 of Wasmtime, the Rust-implemented WebAssembly runtime, addressing 12 distinct security advisories including two at Critical severity. The batch tripled Wasmtime's entire advisory output from 2025 and doubled the project's all-time tally of Critical-level findings in a single coordinated release.
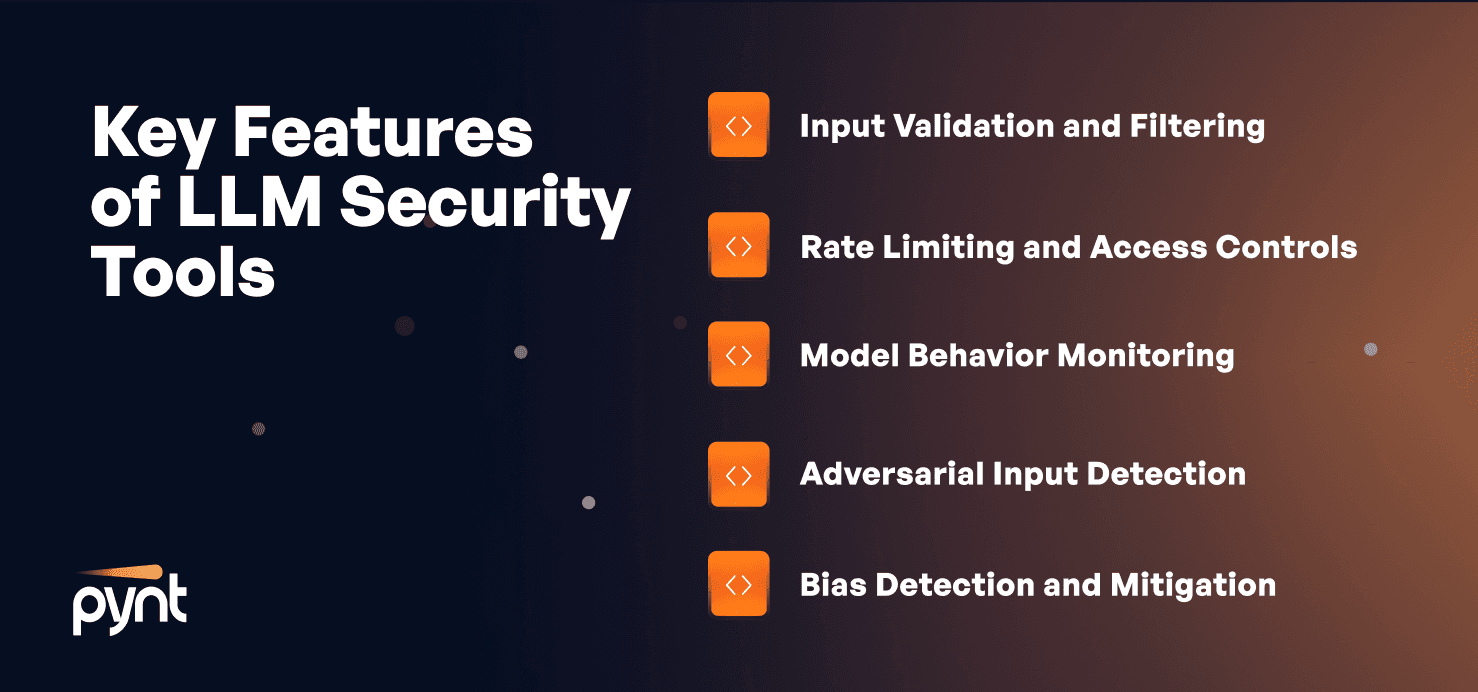
Eleven of those 12 advisories were discovered not through traditional fuzzing or manual review, but through new LLM-based analysis tooling. Over a three-week sprint, maintainers from Bytecode Alliance member organizations including Mozilla, UCSD, Akamai, and F5 built and deployed a multi-agent harness that combined automated code search, multi-agent analysis, and exploit reproduction capabilities to probe Wasmtime's codepaths and backends. The harness went beyond flagging suspicious patterns; it generated proof-of-concept exploits and test vectors to confirm each finding before it was logged as an advisory.
Wasmtime has long been one of the more security-conscious Rust codebases in production use. The project maintains regulated unsafe code practices validated through Miri testing, uses cargo vet for dependency auditing, continuously fuzzes tier-1 features, and applies Spectre mitigations against speculative-execution attack vectors. The Bytecode Alliance team framed the LLM-assisted sprint as complementary to those existing practices, not a replacement for them, and committed to continued investment in the tooling.

Operators running Wasmtime should upgrade immediately. The patched branches are 43.0.1, 42.0.2, 36.0.7, and 24.0.7; the two Critical-severity advisories make the upgrade urgent regardless of deployment context.
The coordinated disclosure sets a precedent for how Rust-based infrastructure projects can approach emerging security tooling. A multi-institution team applied LLM analysis offensively, confirmed exploitability programmatically, and published through a structured advisory process. The Bytecode Alliance maintainers were explicit about what that signals: these tools are reshaping the vulnerability-discovery landscape, and projects that don't adopt them defensively are likely to encounter adversaries who already have.
Know something we missed? Have a correction or additional information?
Submit a Tip

