Baltimore City Employee's Violent Threats, Toxic Messages Violated Technology Policy, OIG Finds
A city employee threatened to "kill" and "crack skulls" of coworkers using government computers, a new OIG report finds — completed before City Hall stripped the watchdog's record access.

A Baltimore City employee sent multiple Microsoft Teams messages from their City account to staff members and employees in other agencies using profanity, writing about causing harm, and making insulting comments about other city workers — and did so on government systems that carry an explicit warning: "Users have no expectation of privacy when using City IT resources."
The investigation began in the spring of 2025, after current and former employees reported concerns about the employee's "hostile management style." The OIG reviewed emails and Teams messages spanning over a year and a half, uncovering numerous violations of the City's Technology Acceptable Use Policy. The resulting public synopsis, Case #26-0031-I, was released by Inspector General Isabel Mercedes Cumming's office at City Hall, Suite 635, 100 N. Holliday Street.
The misconduct extended beyond crude language. The OIG found that the employee encouraged a staff member to bypass the city's own permitting process for their personal residence, telling them to "leverage your relationship." When the staff member expressed guilt, saying it felt wrong to "jump in line," the employee dismissed the concern, writing "nobody else respects process."
Because many of the communications involved people who reported to this employee, the OIG warned that the messages potentially could create and foster a toxic or hostile workplace environment for city employees.
The Mayor's Office responded in a letter dated February 4, 2026, acknowledging receipt and stating only that "the appropriate response to this personnel matter will be undertaken." No timeline or details about disciplinary action were mentioned.
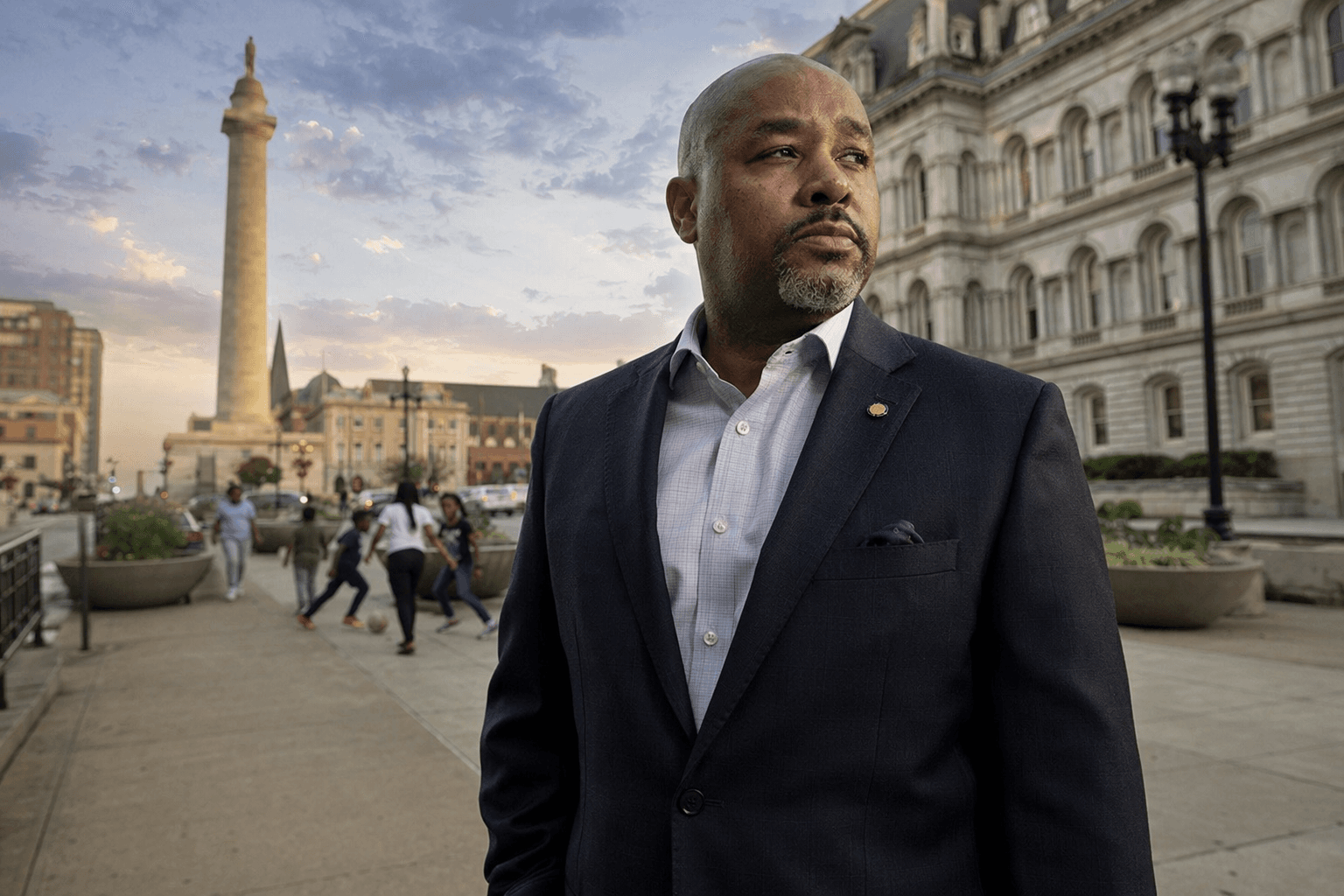
Inspector General Cumming noted in the opening letter of the OIG report that the City of Baltimore removed the OIG's direct access to records, files, and communications on February 6, 2026, and that this investigation was completed before then. The two-day gap between the Mayor's Office response and the access cutoff has drawn attention to the broader conflict between the watchdog office and Mayor Brandon Scott's administration over the scope of the OIG's investigative powers.
The technology-use finding is not an isolated incident. The OIG has issued a string of prior reports documenting misuse of City computers and communications systems, including one case in which a Department of Transportation employee was found sending numerous inappropriate emails to an external recipient, and another in which a city employee was terminated after misusing his work computer to access thousands of explicit images.
The Case #26-0031-I report lands amid a broader wave of scrutiny over the Mayor's Office of Neighborhood Safety and Engagement. Inspector General Cumming said fraud connected to the now-defunct SideStep youth diversion program cost taxpayers "thousands of dollars" and she referred her team's findings to law enforcement. A review of Workday invoices for SideStep community-based organizations showed the city issued approximately $694,798.86 to those groups under the program. The program was limited to the Western District and stopped operating in 2024.
The SideStep investigation also surfaced a significant data breach: a MONSE employee sent a diversion table containing post-arrest diversions to a relative's Gmail account, with the list covering cases from 2018 through September 2022 and including individuals' dates of birth and charges. The list contained approximately 701 names, many of them juveniles. MONSE said it was "not identified any malicious use of the data or further mishandling related to this singular email," but added that "regardless of intent, such disclosure is completely unacceptable and violates MONSE's existing data policy, as well as State law."
The findings from the latest OIG report have been referred to law enforcement for further criminal investigation, though it remains unclear which law enforcement agency is continuing the probe.
MONSE records have been at the center of a dispute between Mayor Scott's administration and Cumming over the availability of data to the inspector general. In January, Scott's staff announced they were cutting access to city legal records for Cumming's team after discovering a member of her staff had "unfettered" access to a city attorney's documents; the administration argued the access violated attorney-client and work product privileges.
Tips on fraud, waste, or abuse in Baltimore City government can be reported to the OIG hotline at 443-984-3476 or 800-417-0430.
Know something we missed? Have a correction or additional information?
Submit a Tip