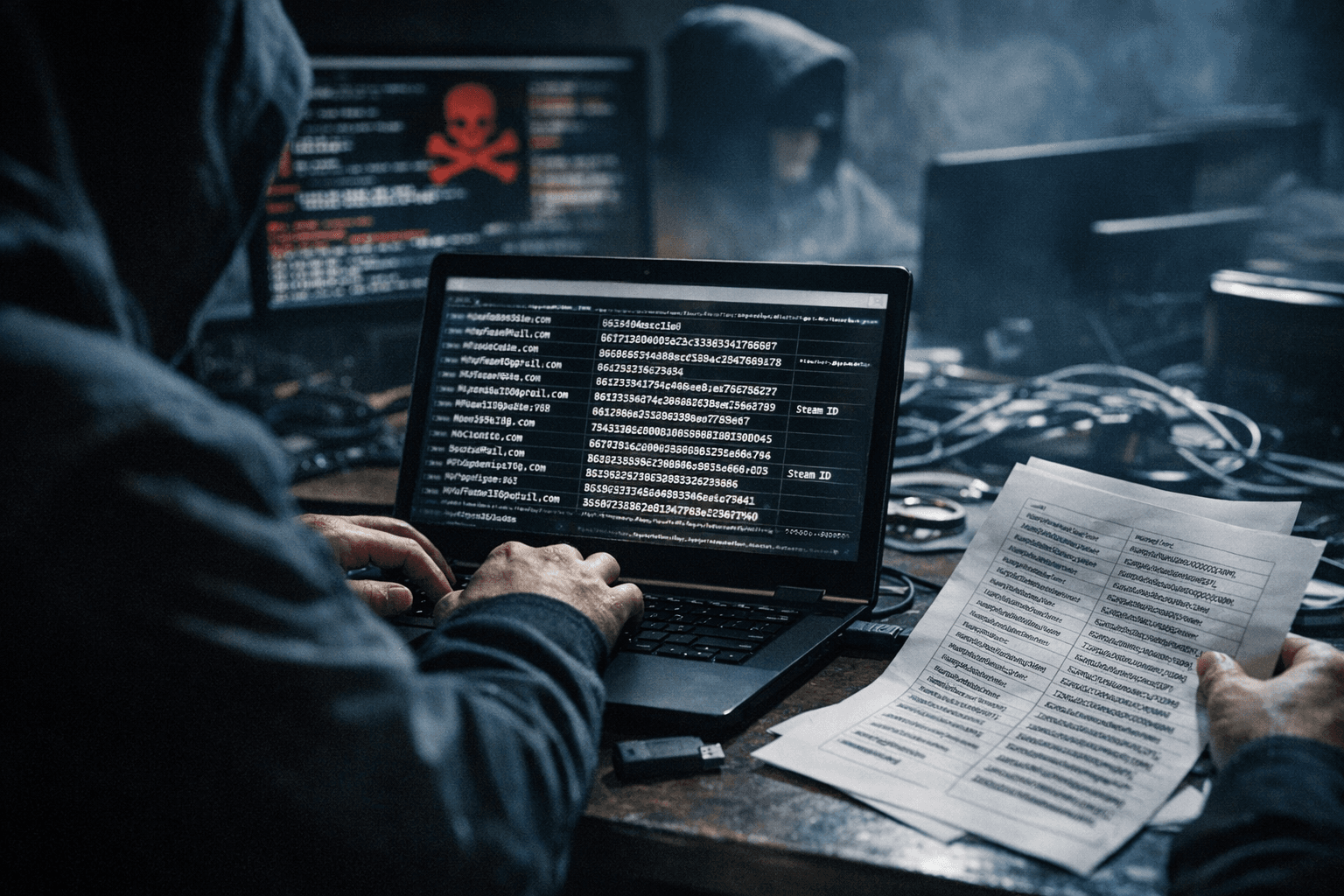
Alleged FiveM Server SQL Dump Exposes Emails, Password Hashes, Game IDs
Brinztech warned on March 1, 2026 that a threat actor claims to have exfiltrated a full SQL dump from a major FiveM server, allegedly containing emails, password hashes, Steam and Discord IDs, and donation logs.

Brinztech published an alert on March 1, 2026 reporting that a threat actor "claims to have exfiltrated a full SQL dump from the server’s backend," and that the listing targets a major FiveM server. The alert lists exposed items as "Usernames, registered email addresses, and potentially IP addresses used during gameplay sessions," plus "password hashes (often stored in MD5 or Bcrypt, depending on the server’s legacy scripts) and salt values," and in-game metadata including "Steam IDs, Discord IDs, in-game currency balances, and historical transaction logs for server 'donations' or store purchases."
The Brinztech analysis frames the incident as an infrastructure compromise, saying the dump points to either "a compromise of the server’s database management system or an exploit within a custom-coded web portal used for player stats and whitelisting." Brinztech lists likely attack vectors as "potential SQL injection or unauthorized file upload on the server’s web panel" and raises persistence concerns with the wording "Persistence through Web Shells: The nature of the leak suggests a potential SQL injection or unauthorized file upload on the server’s web panel. This implies that the threat actor may have left behind 'backdoors' to maintain persistent access to the server’s live traffic and future player data."
Brinztech classifies the breach as a "Tier 1" threat, citing "the high rate of password reuse among the gaming community," and explicitly warns of "Social Engineering and Doxxing: The combination of Steam/Discord IDs and IP addresses allows for sophisticated doxxing. Malicious actors can use this data to track players across different platforms, leading to harassment or 'swatting' risks within the competitive RP community." The alert also contains a contact header listing "perm_phone_msgCall & WhatsApp : +971 52 603 9711."
This alleged SQL dump arrives months after Cfx.re publicly acknowledged a separate security failure in August 2025. Cfx.re issued a statement used across reporting outlets that said, "Recently, we identified a security issue in our asset escrow system that allowed bad actors to extract encrypted assets from the game client and bypass the safeguards designed to prevent those assets from being used by servers without the permission of the original creator." Cfx.re added, "We take the security of our platform extremely seriously, and our team is working to resolve this issue as quickly as possible."
Cfx.re also announced enforcement measures in the aftermath of the asset escrow problem, warning that "While we work on a fix, we are immediately implementing two-week suspensions to all servers who are confirmed to have used leaked assets without authorization from the original creator. Moving forward, any servers caught with leaked assets again will be permanently terminated. As a reminder, only Tebex-accredited creators are authorized resellers of FiveM and RedM assets. Please ensure any creators are Tebex accredited before making a purchase."
The Brinztech item and the August 2025 asset escrow admission are distinct in scope and vector in the available text: Brinztech focuses on a claimed SQL database dump with PII and transaction logs, while Cfx.re’s August statement addressed extraction of encrypted client assets. The Brinztech alert is presented as dark-web intelligence reporting a threat actor claim; the excerpt does not include independent forensic evidence or a named affected server in the public text.
Verify your control panel and web portals for unauthorized uploads and signs of SQL injection, confirm asset provenance with Tebex accreditation where applicable, and treat exposed accounts as high risk for credential stuffing given Brinztech’s "Tier 1" assessment. For further technical follow up, Brinztech listed a contact as WhatsApp/phone +971 52 603 9711 in the alert header, and platform confirmation from Cfx.re on whether the March 1, 2026 listing matches any known server compromises remains a critical next step. If validated, a dump containing emails, password hashes, Steam and Discord IDs, and donation logs will materially raise doxxing, swatting, and account-takeover risks across FiveM RP servers.
Know something we missed? Have a correction or additional information?
Submit a Tip