Anonymous School and Crime Tip Platform Leak Exposes Millions of Submissions
A hacker group stole 8.3 million anonymous crime and school tips from P3 Global Intel, exposing tipster identities, Social Security numbers, and cartel intelligence dating to 1987.

Straight Arrow News and DDoSecrets obtained more than 8.3 million highly sensitive records from P3 Global Intel, stolen by a hacker group calling itself "THE INTERNET YIFF MACHINE." The data spans from February 1987 to November 2025. The platform, built to guarantee anonymity to anyone reporting a crime or a school safety threat, turns out to have been anything but.
The Texas-based company enables the public to share crime tips, anonymously it says, with thousands of clients, including Crime Stoppers programs, local and federal law enforcement agencies, public schools, and the U.S. military. The leak contains extensive personal data on people accused by tipsters: names, email addresses, dates of birth, phone numbers, home addresses, license plate numbers, Social Security numbers, and criminal histories. Tipsters' own personal information also appears throughout the leak.
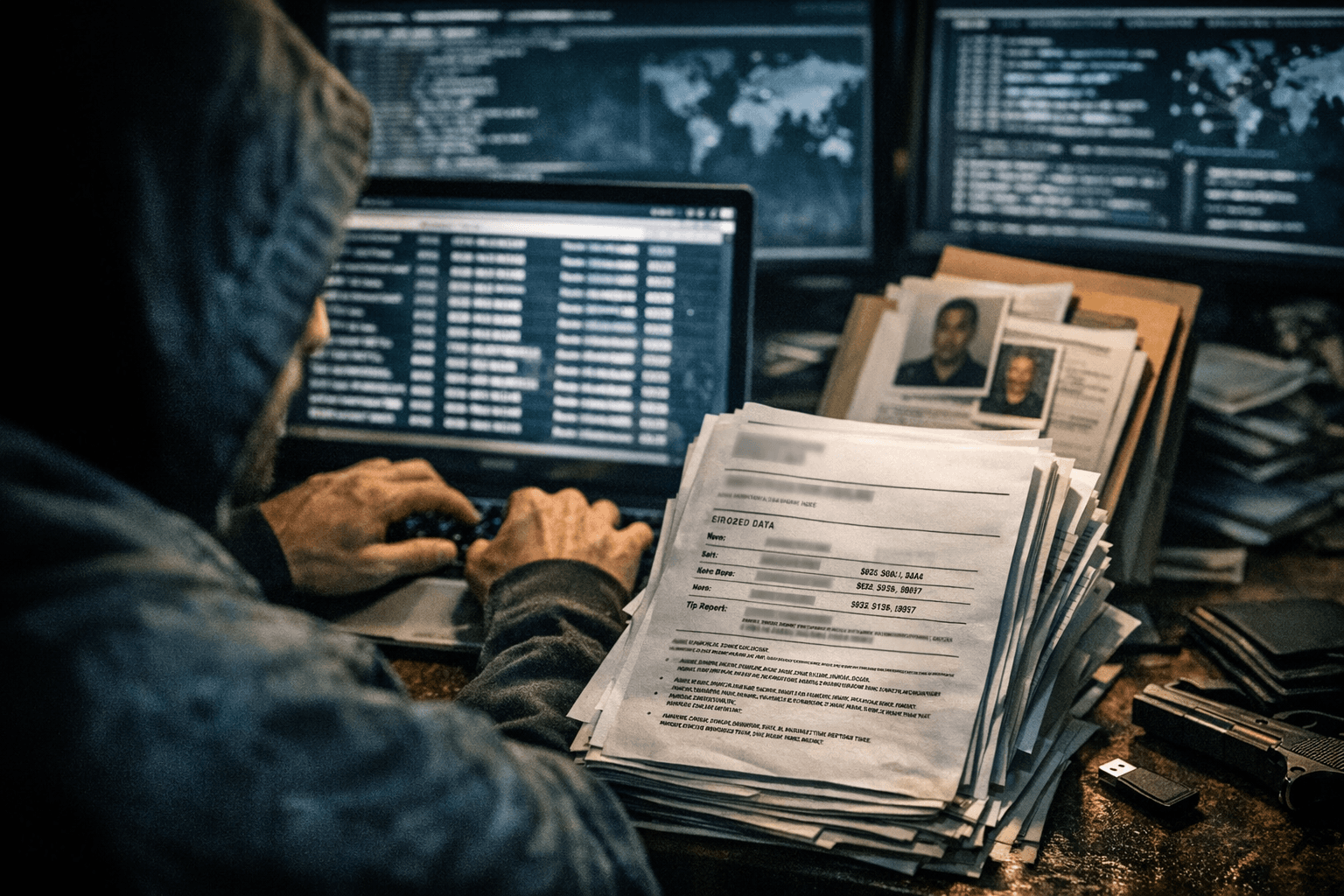
The hacker, using the name Internet Yiff Machine, said in a statement that they hacked and shared the data to expose that the confidential tips people submit through Navigate360's P3 Global Intel platform are neither secure nor anonymous. In a statement posted online, the hacker said they obtained about 93 gigabytes of data after taking over a customer account through social engineering and exploiting a system vulnerability.
The content of what was exposed goes well beyond routine crime reports. Sinaloa cartel trafficking intelligence from a California resident demanding strict anonymity sits alongside military sexual assault reports and school suicide risk assessments. Many of the messages in the leaked data involve students in crisis: self-harm, suicide threats, bullying, and potential violence. In one report from 2022, a parent told Pennsylvania's Safe2SayPA program about a seventh-grader who classmates were calling "the school shooter." The student had been fixated on firearms and grenades, the parent wrote. A wellness check later sent the child to a hospital for a mental evaluation.
The scope of the platform's reach amplifies the damage. According to its website, 30,000 schools use its P3 Global Intel confidential tip app. Clients of P3 include the US Air Force, Army Criminal Investigation Division, Homeland Security Investigations, the Secret Service, and the IRS Criminal Investigation Division. Federal spending records show four departments, Defense, Homeland Security, Justice, and Interior, paid P3's parent company nearly $1.3 million between 2020 and 2025.
The breach also revealed a quiet contradiction at the core of P3's marketing. The hackers exposed an internal page for P3's customers, marked confidential, that reveals how the company's clients can track tipsters without their knowledge. The page details an opt-in feature titled "Session Information Disclosure" that allows P3 customers to request their tipsters' IP addresses. By default, the feature is disabled on all accounts, but when tracking is enabled, the values are stored for a period of up to 90 days and can be made available to clients upon formal request in the event of serious misuse or abuse.
Those messages do not appear to have been stored in an encrypted format, which would protect them in the event of a data breach; IDs and passwords were located in plain text.
DDoSecrets stated that the dataset challenges some of the statements made by P3: while P3 says that communications on the system are encrypted, the data was allegedly retrieved in plaintext, and P3 also claims that the tip collection and messaging process is anonymous, but the data indicates that administrators are secretly given the ability to de-anonymize users.
Mailyn Fidler, a cybersecurity professor at UNH Law, put the stakes bluntly. "Those risks include severe harm and even death to police informants... risks to national security," Fidler warned. David Riedman, founder of the K-12 School Shooting Database and a professor of security and risk management at Idaho State University, focused on the student side. "The kind of data collected through anonymous tips is highly sensitive and if exposed could harm both the reporters and the subjects of the tips," Riedman said.
DDoSecrets released 91.53GB of data for researchers and journalists, describing the archive as containing "millions of submissions and tips about alleged crimes and terrorist acts made over several decades." The leak was named "BlueLeaks 2.0," after the landmark BlueLeaks hack from 2020, which exposed 269GB of internal US law enforcement data from over 200 agencies.
Navigate360 CEO JP Guilbault told Cybernews that the company is "currently working to determine whether we have experienced an incident involving our computer network" and has hired an independent third party to conduct a full forensic investigation. "To this point, we have not confirmed that any sensitive information has been accessed or misused," Guilbault said.
Cybersecurity experts recommend that schools should take steps now to protect student data as they wait for confirmation of a potential hack of Navigate360's P3 Global Intel platform. For the students, informants, and military personnel whose tips were filed in confidence over nearly four decades, confirmation may come too late to matter.
Know something we missed? Have a correction or additional information?
Submit a Tip
