Canvas Maker Says It Struck Deal With Hackers After Data Breach
Instructure said it negotiated with hackers to delete stolen Canvas data, after a breach that disrupted schools during finals and raised the stakes for millions of users.
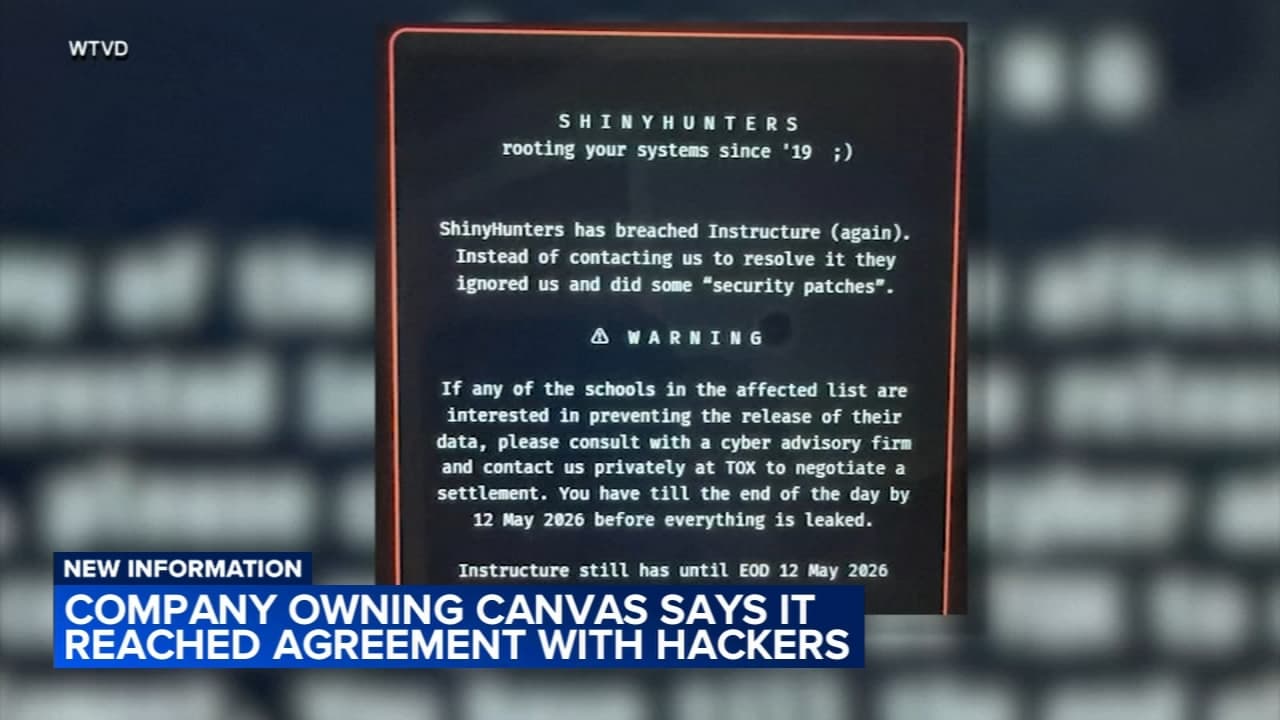
Instructure said it struck a deal with hackers to delete data stolen from Canvas, a rare move that puts schools, students and families inside a fast-moving extortion economy where criminals can hold everyday academic life hostage. The breach hit Canvas, the learning platform used to manage grades, course notes, assignments, lecture videos and school messages, and it landed at the worst possible moment for students in the middle of finals.
Canvas serves thousands of schools and has 30 million active users, making it one of the most deeply embedded systems in American education. When Instructure put Canvas, Canvas Beta and Canvas Test into maintenance mode on May 7, the disruption reached far beyond a routine outage. By May 11, the company said Canvas was available for most users again, and its final status update said it was not seeing ongoing unauthorized activity.
The company’s response now becomes part of the precedent. Rather than waiting for stolen information to surface elsewhere, Instructure negotiated with the hackers in hopes of forcing deletion. That may limit one immediate release, but it does not erase the practical risk for districts that already had to notify students and parents, rebuild confidence and check whether data had been copied, shared or resold before any deletion promise was made.
ShinyHunters publicly claimed responsibility for the breach and set extortion deadlines that included May 12, signaling that the pressure campaign was still active as schools scrambled to respond. Reporting tied to the incident said the hackers claimed nearly 9,000 schools worldwide were affected, and one security analysis said the group claimed to have stolen 275 million records from roughly 9,000 education institutions worldwide. Those figures remain the hackers’ claims, but they show the scale of leverage criminals believe they can extract from school technology.
Instructure has urged customers to enforce multifactor authentication on privileged accounts, review admin access and rotate API tokens or keys where applicable. It also said it would communicate directly with impacted customers with organization-specific information and support.
The company had already disclosed a separate security issue in September 2025 involving a social-engineering attack on a third-party Salesforce instance, which it said did not expose Instructure products or product data. That history underscores the vulnerability of education vendors that sit between schools and the records they now depend on every day. Even if hackers delete what they stole, the trust damage can linger long after the data itself is gone.
Know something we missed? Have a correction or additional information?
Submit a Tip