Critical Cisco Firewall Zero-Day Exploited by Interlock Ransomware Before Patch Release
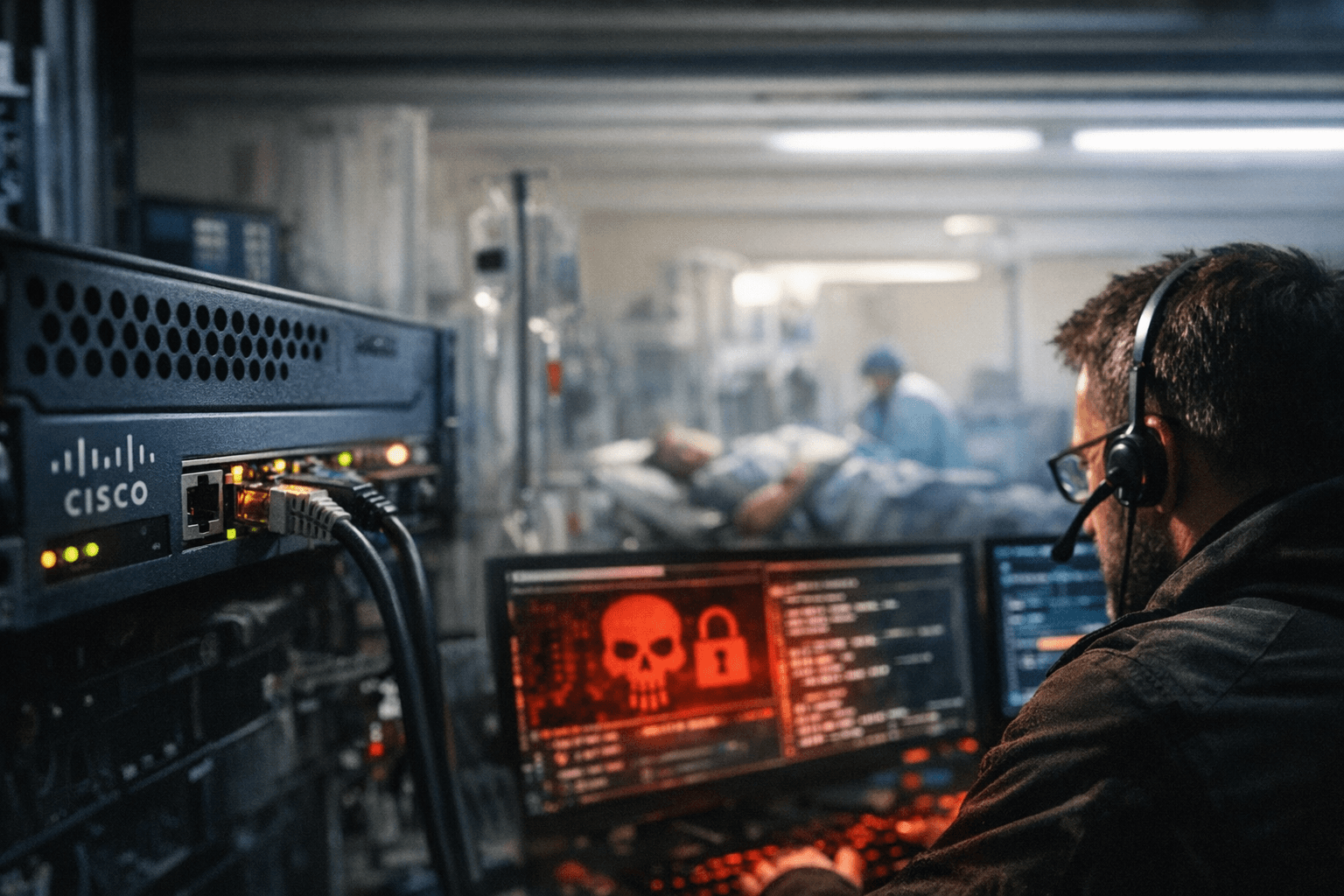
Interlock ransomware exploited a perfect-10 Cisco firewall zero-day for 36 days before a patch existed, hitting hospitals and a U.S. city before defenders knew to look.

Amazon Threat Intelligence identified an active Interlock ransomware campaign exploiting CVE-2026-20131, a critical vulnerability in Cisco Secure Firewall Management Center software that could allow an unauthenticated, remote attacker to execute arbitrary Java code as root on an affected device, which was disclosed by Cisco on March 4, 2026. The twist: Interlock was exploiting this vulnerability 36 days before its public disclosure, beginning January 26, 2026.
CVE-2026-20131 carries a CVSS score of 10.0 and stems from insecure deserialization of a user-supplied Java byte stream, which could allow an unauthenticated, remote attacker to bypass authentication and execute arbitrary Java code as root on an affected device. The Cisco Secure Firewall Management Center is a centralized administration system for critical Cisco network security appliances, including firewalls, application control, intrusion prevention, URL filtering, and malware protection.
Amazon discovered the pre-patch exploitation only after Cisco's advisory prompted a retrospective search. Amazon said it started searching for exploitation of CVE-2026-20131 after Cisco's advisory, using the company's MadPot global network, a honeypot system comprising thousands of sensors deployed throughout its AWS platform, which quickly uncovered attacks dated weeks prior to the vulnerability being made public. CJ Moses, CISO for Amazon Integrated Security, said: "Observed activity involved HTTP requests to a specific path in the affected software." Request bodies contained Java code execution attempts and two embedded URLs: one used to deliver configuration data supporting the exploit, and another designed to confirm successful exploitation by causing a vulnerable target to perform an HTTP PUT request and upload a generated file.
Amazon's researchers went further by simulating a compromised system. Amazon gained insight into the attacker's infrastructure by using the honeypot to mimic a vulnerable firewall system, which resulted in an attack on the honeypot that received a malicious binary from the attackers and revealed that the ransomware depended on a single server with a poorly-secured staging area. From this, researchers were able to analyze the group's full attack chain, including Trojans, reconnaissance scripts, and evasion techniques.
As Moses put it: "This wasn't just another vulnerability exploit; Interlock had a zero-day in their hands, giving them a week's head start to compromise organizations before defenders even knew to look." Moses later clarified to CSO Online that the "week's head start" referred to the gap between the date of the first exploit that Amazon's analysis had unearthed and Cisco's own discovery of the bug.
The attack chain that followed initial access was methodical. After initial access, Interlock deployed PowerShell scripts to systematically map compromised networks, collecting system, user, and browser data across multiple machines. The group then used custom remote access trojans, written in both JavaScript and Java, to maintain persistent control, execute commands, transfer files, and exfiltrate data via encrypted communications. To hide their activity, attackers set up proxy-based relay infrastructure that masked the origin of attacks and regularly wiped logs to erase evidence.
The ransom note also threatened to expose victims to regulators, using the pressure of fines and compliance violations, in addition to data encryption and leaks, to solicit payment.
Interlock ransomware has claimed several high-profile victims since its launch in late 2024, including DaVita, Kettering Health, the Texas Tech University System, and the city of Saint Paul, Minnesota. The group has infected hospitals and medical facilities, disrupting chemotherapy sessions and pre-surgery appointments at Kettering Health, and claimed to have stolen 43 GB of files from the city of Saint Paul, forcing the Minnesota capital to declare a state of national emergency.
In the past, Interlock has targeted sectors including education, engineering, architecture, construction, manufacturing, healthcare, and government, but given that the group was able to exploit a zero-day vulnerability in equipment as prevalent as Cisco firewalls for more than a month, any vulnerable organization might be at risk.
The regulatory response came swiftly. CISA added CVE-2026-20131 to its Known Exploited Vulnerabilities catalog, marking it as "known to be used in ransomware campaigns," and ordered federal agencies to patch by March 22. Cisco published its security bulletin on March 4, urging system administrators to apply security updates as soon as possible and warning that no workarounds are available. The procedure for patching CVE-2026-20131, and the other 47 CVEs included in Cisco's March 4 update, varies depending on the FMC software version installed.
The FMC incident is not isolated. CVE-2026-20131 is the third Cisco vulnerability flagged as exploited as a zero-day since the start of this year, with attackers also leveraging CVE-2026-20127 in Cisco Catalyst SD-WAN Controller and CVE-2026-20045 in the company's unified communications solutions. Moses framed the broader problem plainly: "The real story here isn't just about one vulnerability or one ransomware group; it's about the fundamental challenge zero-day exploits pose to every security model. When attackers exploit vulnerabilities before patches exist, even the most diligent patching programs can't protect you in that critical window.
Know something we missed? Have a correction or additional information?
Submit a Tip

