Gunra Ransomware Group Claims Data Leak After Trio-Tech International Attack
Stolen data from Trio-Tech International's Singapore subsidiary is already online after the Gunra ransomware group published sample files, just two weeks after the March 11 attack was initially dismissed as non-material.
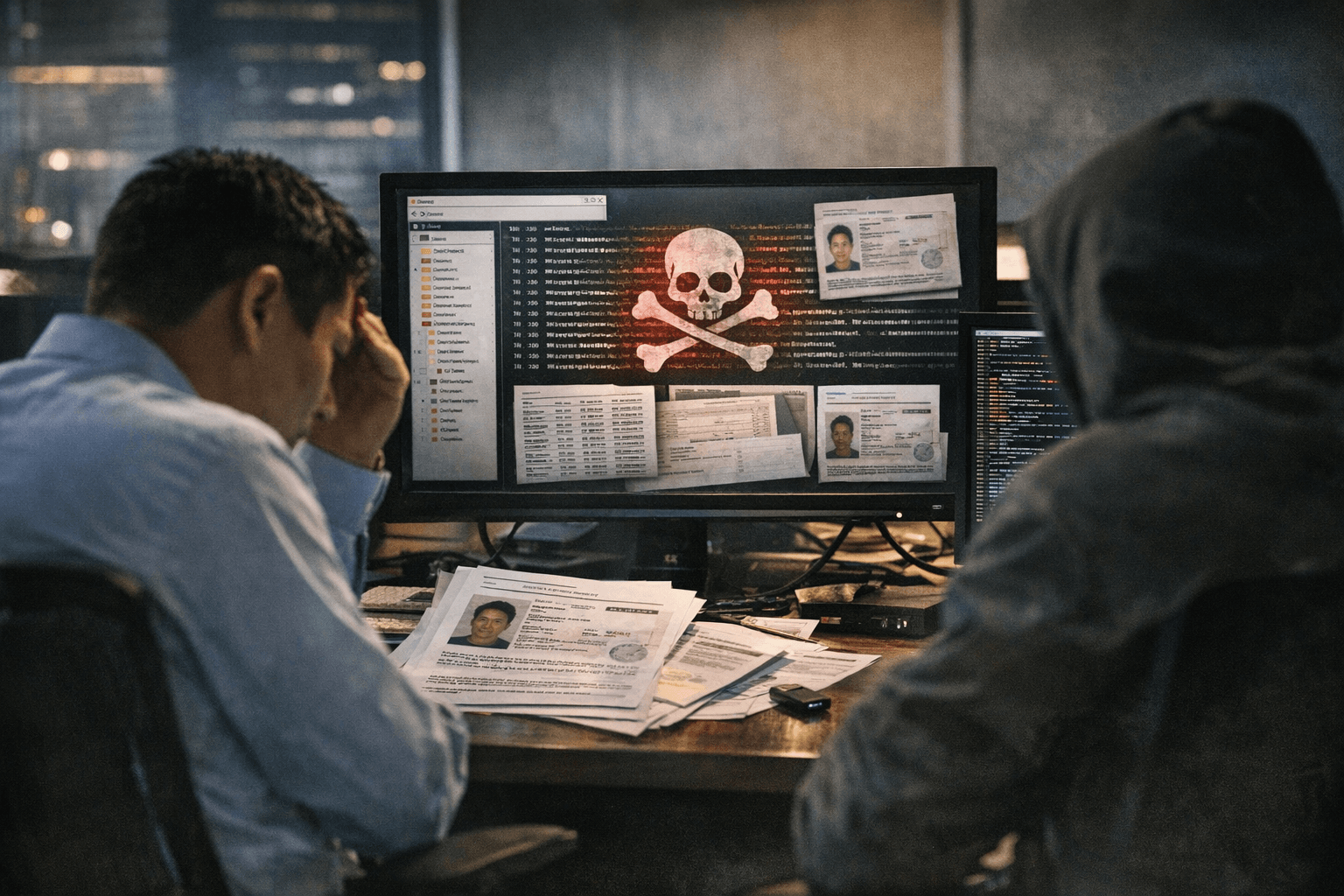
Stolen data from Trio-Tech International's Singapore operations was already circulating on the dark web by the time the California-based semiconductor testing firm acknowledged the full severity of its ransomware attack, a sequence that forced a rapid reversal of the company's own materiality assessment.
The incident occurred on March 11 and resulted in the encryption of certain files within the subsidiary's Singapore network. At the time, management determined the incident was not material. That assessment held for a week. On March 18, the incident escalated and resulted in the unauthorized disclosure of certain company data, prompting management to conclude that the incident may constitute a material cybersecurity event.
Trio-Tech did not share details on the threat actor responsible in its SEC filing, but the Gunra ransomware group added Trio-Tech to its Tor-based leak site. According to cybersecurity researchers, Gunra claimed responsibility by listing Trio-Tech on that dark-web site, the equivalent of a trophy wall. The group follows a double extortion playbook, encrypting files first and then threatening to publish stolen data if the ransom is not paid, and the fact that data has already appeared online suggests either negotiations broke down or never happened at all.
Gunra is a financially motivated threat actor that emerged in April 2025 and deploys double-extortion tactics to encrypt victims' data while threatening leaks of exfiltrated information, primarily targeting Windows and Linux systems across healthcare, manufacturing, and other sectors worldwide. Victims are typically given a five-day deadline, with negotiations conducted via Tor-based portals styled similarly to messaging apps like WhatsApp, complete with assigned roles such as "Manager." The group's malware is believed to be based on the Conti ransomware source code.
Upon discovery, Trio-Tech's Singapore subsidiary immediately activated its response protocols, implemented containment measures including proactively taking its network offline, launched an investigation with the assistance of third-party cybersecurity professionals, and notified law enforcement in Singapore. The company also disclosed the incident to U.S. regulators, filing an 8-K with the Securities and Exchange Commission. Trio-Tech has not said what data may have been taken, whether a ransom was demanded, or if any payment was made.
"The subsidiary is also working closely with its cyber insurance provider to support the investigation, remediation, and potential claims process," Trio-Tech said in its SEC filing.
Trio-Tech does not expect the incident to have a material impact on financial results for the three months ended March 31, 2026, though that forward-looking assessment carries an asterisk. The full scope of the ransomware attack is still unknown and it may have an impact on the company's finances.
Trio-Tech provides semiconductor back-end solutions including manufacturing, testing, and distribution services, as well as industrial electronic equipment, with offices in the U.S., China, Malaysia, Singapore, and Thailand. The company reported more than $36 million in revenue last year, with 94% of its customers located in Asia, and has about 600 employees, most of whom are located across Asia. That customer concentration deepens the stakes: a breach touching chip testing and verification data could ripple across automotive, industrial, and computing supply chains that Trio-Tech serves across the region.
The incident comes roughly a month after another semiconductor test equipment supplier, Advantest, reported a ransomware attack to Japanese authorities. Ransomware gangs have repeatedly targeted the semiconductor industry over the last five years, with Microchip Technology struck by the Play ransomware gang in 2024, Applied Materials hit in 2023, and Chinese-owned Nexperia and Taiwan's Foxsemicon both experiencing attacks.
Trio-Tech says its investigation is ongoing and it has not yet determined the full scope of compromised data. The number of affected individuals has not been disclosed, and the company has not publicly named the third-party cybersecurity firm leading its forensic response. The Gunra leak site posting remains active, and whether additional data surfaces will likely depend on whether the two sides were ever in contact at all.
Know something we missed? Have a correction or additional information?
Submit a Tip

