Iranian-Linked Hackers Target U.S. Supply Chains, Threatening Critical Infrastructure
Iranian-linked hackers breached Stryker Corp.'s systems in March, disrupting medical device orders in a supply-chain attack with critical infrastructure implications.
The hacking persona known as Handala breached Stryker Corp.'s Microsoft-based internal systems in March, disrupting order processing and manufacturing workflows at one of the world's largest medical device companies. The intrusion has become a defining case study in how Iranian-linked cyber actors are converting regional military tensions into sustained attacks against U.S. supply chains.
Security analysts examining the campaign described the Stryker compromise as emblematic of a broader strategic shift. Rather than assaulting headline infrastructure like power grids or ports directly, Handala and similar groups focus on suppliers, managed service providers and parts distributors that sit one or two links upstream of hospitals, transit systems and manufacturing lines. Disruption at that level cascades downstream, with consequences proportional to the dependencies the targeted company serves.
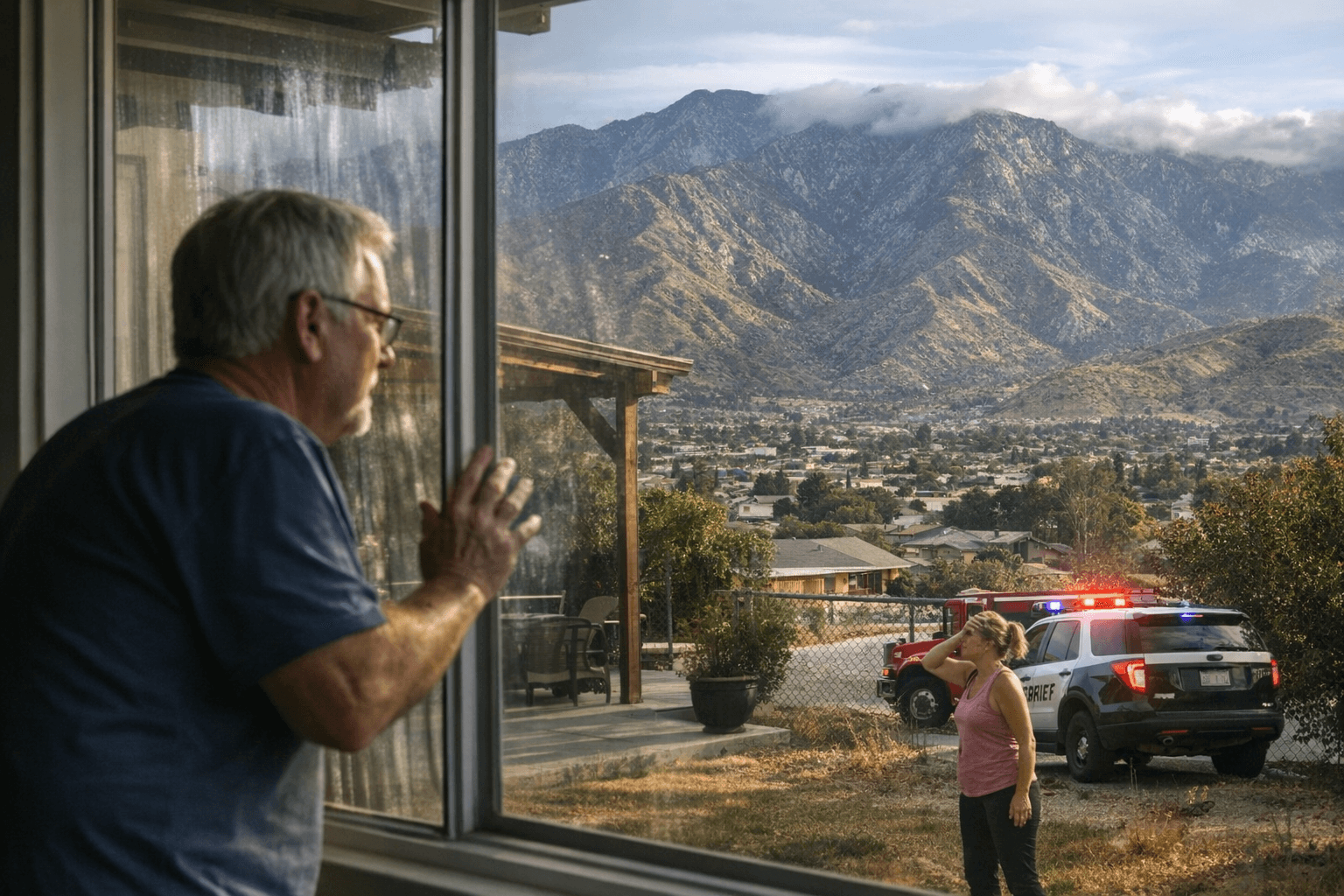
The Stryker attack caused order and shipping delays that rippled through healthcare delivery and device availability. Medical devices reaching hospitals late represents not just a commercial setback but a patient-safety concern, underscoring why analysts consider supply-chain compromise a vector with outsized public-health implications.
The Cybersecurity and Infrastructure Security Agency's "Shields Up" guidance urges organizations across sectors to harden defenses and assume they may be targeted during periods of geopolitical escalation. But security experts warn that government measures alone cannot neutralize the threat. Domain seizures, reward offers and indictments have disrupted specific operations without eliminating the underlying capacity or intent of state-linked actors.
The strategic logic driving these operations lies less in immediate destruction than in persistent access. Gaining a foothold inside networks that service critical supply chains functions like holding a set of keys: operators can steal information, map dependencies and preserve the option to strike later with calibrated precision. Geopolitical shocks, including kinetic strikes or new sanctions packages, elevate the incentive for retaliatory cyber operations that are deniable, asymmetric and capable of disrupting services at distances conventional military action cannot reach.
For corporate risk managers, analysts recommended assuming elevated threat conditions, accelerating incident response rehearsals and treating third-party supplier security as an immediate priority rather than a future audit item.
The broader call is structural: greater private-sector transparency around supply-chain risk, tighter interagency coordination and stronger international cooperation on offensive and defensive cyber norms. Healthcare, logistics and supply-chain operators face the starkest warning. As long as regional conflict persists, those sectors should expect elevated targeting, and the Stryker breach has made clear that the consequences of under-preparation reach well beyond any single company's balance sheet.
Sources:
Know something we missed? Have a correction or additional information?
Submit a Tip