Juniper Networks Patches Dozens of Flaws, Including Critical Default Password Bug
Juniper Networks patched nearly three dozen vulnerabilities, including a critical default password bug in its vLWC product that could grant attackers full, unauthenticated remote access.
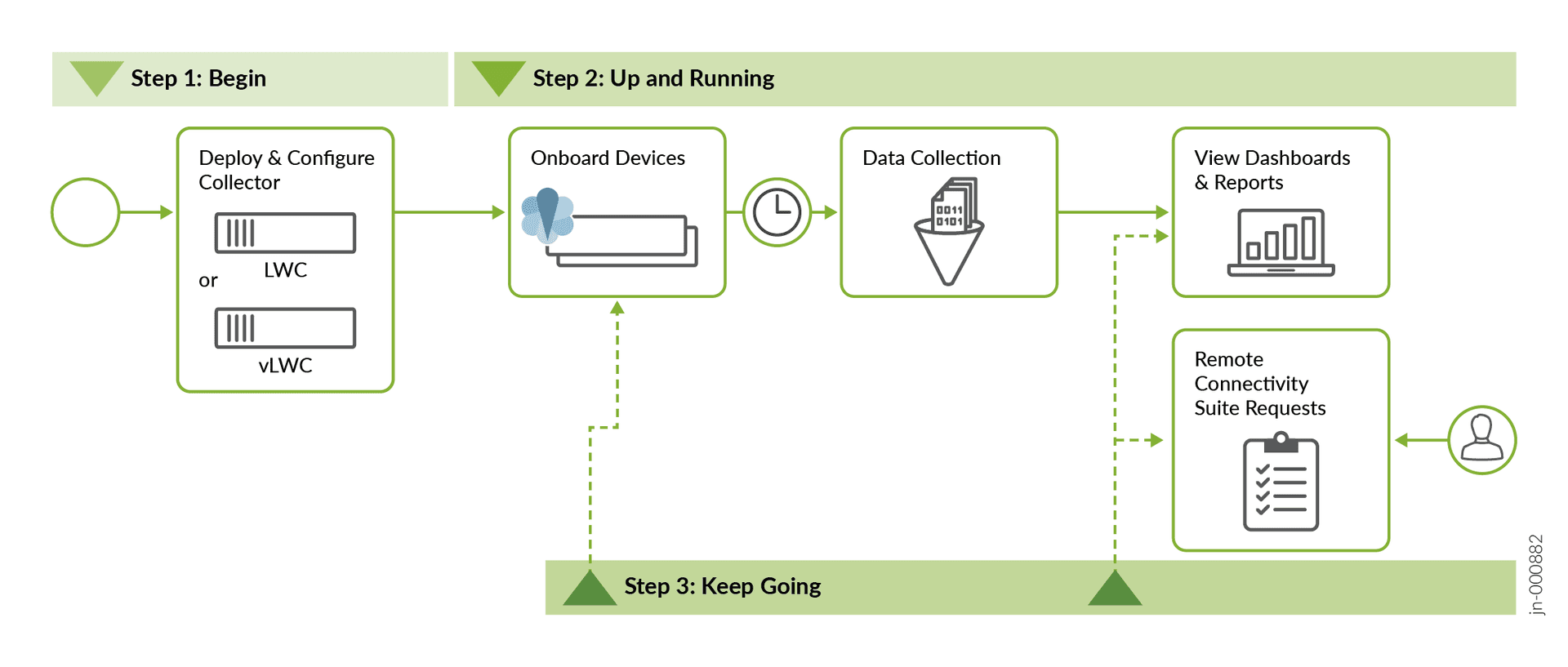
A critical vulnerability in Juniper Networks' Support Insights Virtual Lightweight Collector allowed attackers to gain full, unauthenticated remote access to high-privileged accounts because the software shipped with a default password it never required administrators to change. The flaw, tracked as CVE-2026-33784, was among the most severe in a coordinated batch of nearly three dozen patches Juniper released across its product portfolio between April 8 and 10.
Juniper described the exposure directly in its advisory: "vLWC software images ship with an initial password for a high-privileged account. A change of this password is not enforced during the provisioning of the software, which can make full access to the system by unauthorized actors possible." CVE-2026-33784 carried a very high CVSS rating, placing it among the most urgent fixes in this cycle.
The patch round also addressed a weak password persistence bug in CTP OS, tracked as CVE-2026-33771, and SSH host-key validation weaknesses in Apstra, Juniper's intent-based networking automation platform, that could enable machine-in-the-middle attacks and credential capture. Beyond those headline flaws, the advisories covered privilege escalation bugs, denial-of-service vectors triggered by crafted packets, sensitive information disclosure, firewall bypasses, and remote command execution paths, spanning Junos OS, Junos OS Evolved, and additional Juniper products.
The scope of affected deployments is wide. Junos OS and Junos OS Evolved power service provider and enterprise routing and switching platforms across the MX, PTX, and EX hardware families, as well as newer Evolved branches. Both on-box and virtualized components are impacted across multiple release trains, meaning the vulnerable surface extends to core routing infrastructure at some of the world's largest networks.
National cyber agencies including the Canadian Centre for Cyber Security, HKCERT, and CERT-FR issued guidance calling for immediate asset discovery, prioritized patching of externally reachable and critical devices, and temporary mitigations for systems where live upgrades are not immediately feasible.
The timing adds pressure. Critical infrastructure networks face persistent targeting from both opportunistic actors and nation-state groups, and a flaw allowing unauthenticated full access to a high-privileged monitoring component represents exactly the kind of foothold that advanced adversaries use for lateral movement and sustained presence. Successful exploitation across the broader vulnerability set could produce full device takeover at the network edge or core, traffic manipulation, or prolonged outages.
Juniper's coordinated disclosure across multiple product lines attempts to consolidate the response, but defenders face the practical challenge of triaging patches across divergent platforms and release schedules simultaneously. Configuration hardening, including enforced password rotation at provisioning, and active monitoring of device telemetry remain the most immediate risk-reduction steps available while patch cycles are completed.
Sources:
Know something we missed? Have a correction or additional information?
Submit a Tip

