Microsoft and Europol seize 330 domains to dismantle Tycoon 2FA phishing service
A coalition led by Microsoft and Europol took 330 domains offline on March 4, 2026, disrupting Tycoon 2FA and curbing a service that delivered tens of millions of phishing messages.

Microsoft and Europol announced a coordinated takedown on March 4, 2026, that dismantled the infrastructure of Tycoon 2FA by seizing 330 domains, striking a phishing‑as‑a‑service platform that enabled real‑time multi‑factor authentication bypasses. The action combined technical disruption by Microsoft with law‑enforcement seizures coordinated by Europol and carried out across six national jurisdictions.
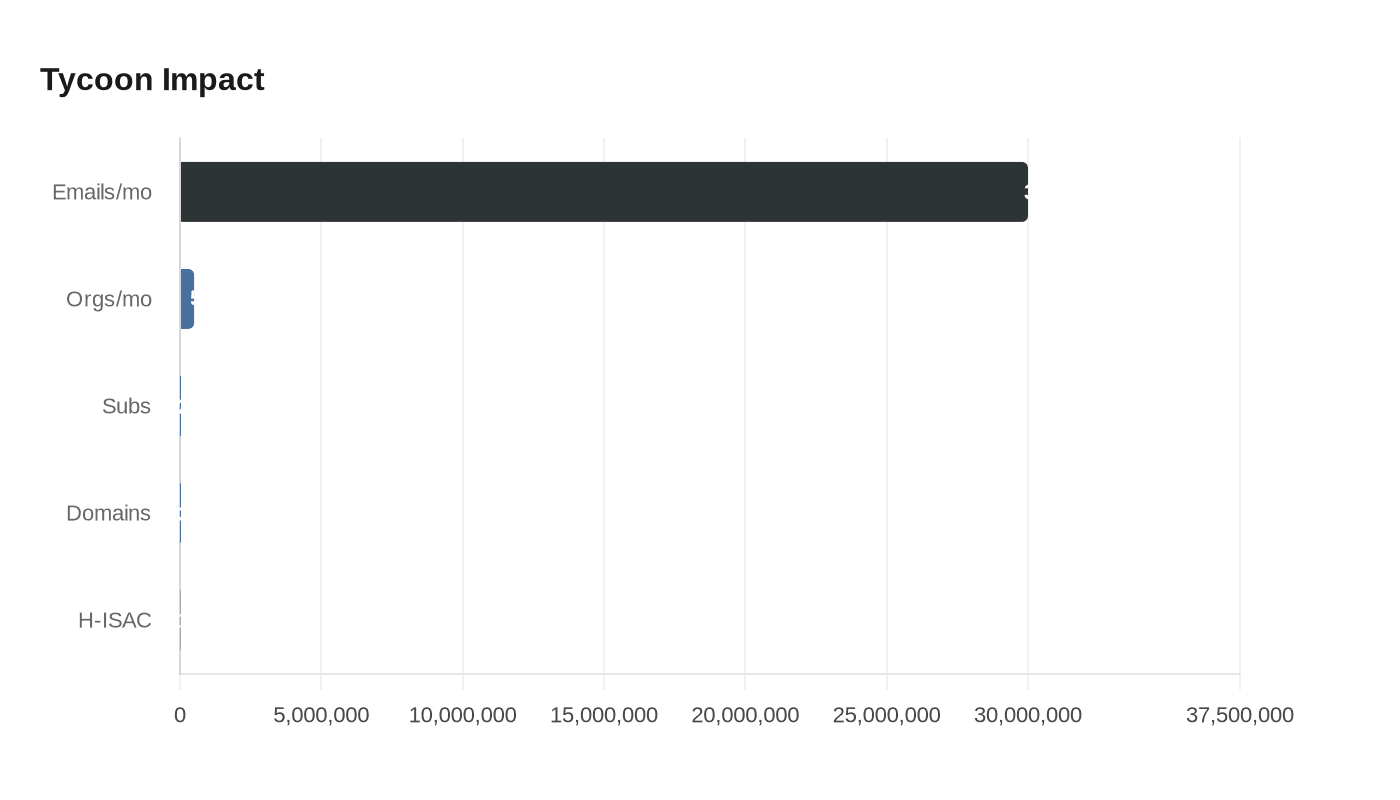
Tycoon 2FA, active since at least August 2023, used adversary‑in‑the‑middle techniques to intercept live authentication sessions and capture credentials, one‑time passcodes and session cookies, allowing attackers to take over accounts while evading standard MFA protections. Microsoft Threat Intelligence and allied firms traced the service to tens of millions of phishing messages that reached more than 500,000 organizations each month, and to a user base of roughly 2,000 service subscribers used by thousands of cybercriminals.
“By mid‑2025, Tycoon 2FA accounted for approximately 62% of all phishing attempts Microsoft blocked, including more than 30 million emails in a single month. That placed Tycoon 2FA among the largest phishing operations globally,” said Steven Masada, assistant general counsel at Microsoft’s Digital Crimes Unit, in commentary supplied by Microsoft.
Investigators said the probe began after intelligence from Trend Micro was shared through Europol’s EC3 advisory groups. BleepingComputer summarized the operational split: “The technical disruption was led by Microsoft with the support of a coalition of private partners, while seizure of infrastructure and other operational measures were carried out by law enforcement in Latvia, Lithuania, Portugal, Poland, Spain, and the United Kingdom – all of this coordinated by Europol.”

The domains seized included control panels and fraudulent login pages that powered Tycoon 2FA’s service. Legal measures preceded the technical action: Microsoft and Health‑ISAC filed a civil complaint naming alleged creator Saad Fridi and four unnamed associates and seeking a $10 million injunction; a court order authorized Microsoft to dismantle and take ownership of the platform’s infrastructure.
Health‑ISAC, the health sector threat‑sharing organization and co‑plaintiff in the complaint, said the platform had tangible consequences for patient care and institutional operations. “More than 100 members of Health‑ISAC … were successfully phished,” the group said, adding that “in New York alone, at least two hospitals, six municipal schools, and three universities faced attempted or successful compromise through Tycoon 2FA.” Health‑ISAC described disruptions including delayed paychecks, rerouted invoices, stolen data, locked networks and interrupted patient care.
Private sector partners provided intelligence, victim notification support and technical assistance. Microsoft and Europol said the action was supported by Cloudflare, Coinbase, Crowell & Moring, eSentire, Health‑ISAC, Intel471, Proofpoint, Resecurity, Shadowserver / The ShadowServer Foundation, SpyCloud, and Trend Micro (also referenced in some outlets as TrendAI).
SpyCloud, which supplied victim telemetry used to prioritize notifications, framed the operation as a strategic shift in defensive tactics. “The coordinated disruption led by Europol, Microsoft, and private sector partners represents a meaningful blow to that ecosystem. Seizing infrastructure, degrading service availability, and enabling victim notification efforts directly reduces harm and raises the operational cost for threat actors. Targeting not just individual operators, but the enabling platform itself, signals a maturing approach to ecosystem‑level disruption,” the company said.
Sources vary slightly on some metrics, some outlets used the phrasing “over 300” domains rather than the specific 330 figure, and other reports rounded Microsoft’s share of blocked phishing to about 60 percent, but the coordinated action removed a widely used enabling service and aims to improve victim remediation and raise barriers for criminals. Security firms recommended rapid moves to phishing‑resistant authentication, strict conditional access, real‑time URL inspection and continuous identity risk monitoring to limit similar threats going forward.
Know something we missed? Have a correction or additional information?
Submit a Tip

