Pentagon Inspector General Says Defense Secretary Shared Strike Details On Signal
A Pentagon inspector general review found Defense Secretary Pete Hegseth used the encrypted messaging app Signal on his personal device to share sensitive information about imminent strikes in Yemen, a practice the report said could have imperiled U.S. forces if intercepted. The finding highlights tensions between classification authority at the top of the Pentagon and departmental rules intended to protect operational security, and it has prompted fierce criticism from lawmakers and calls for tighter communications safeguards.
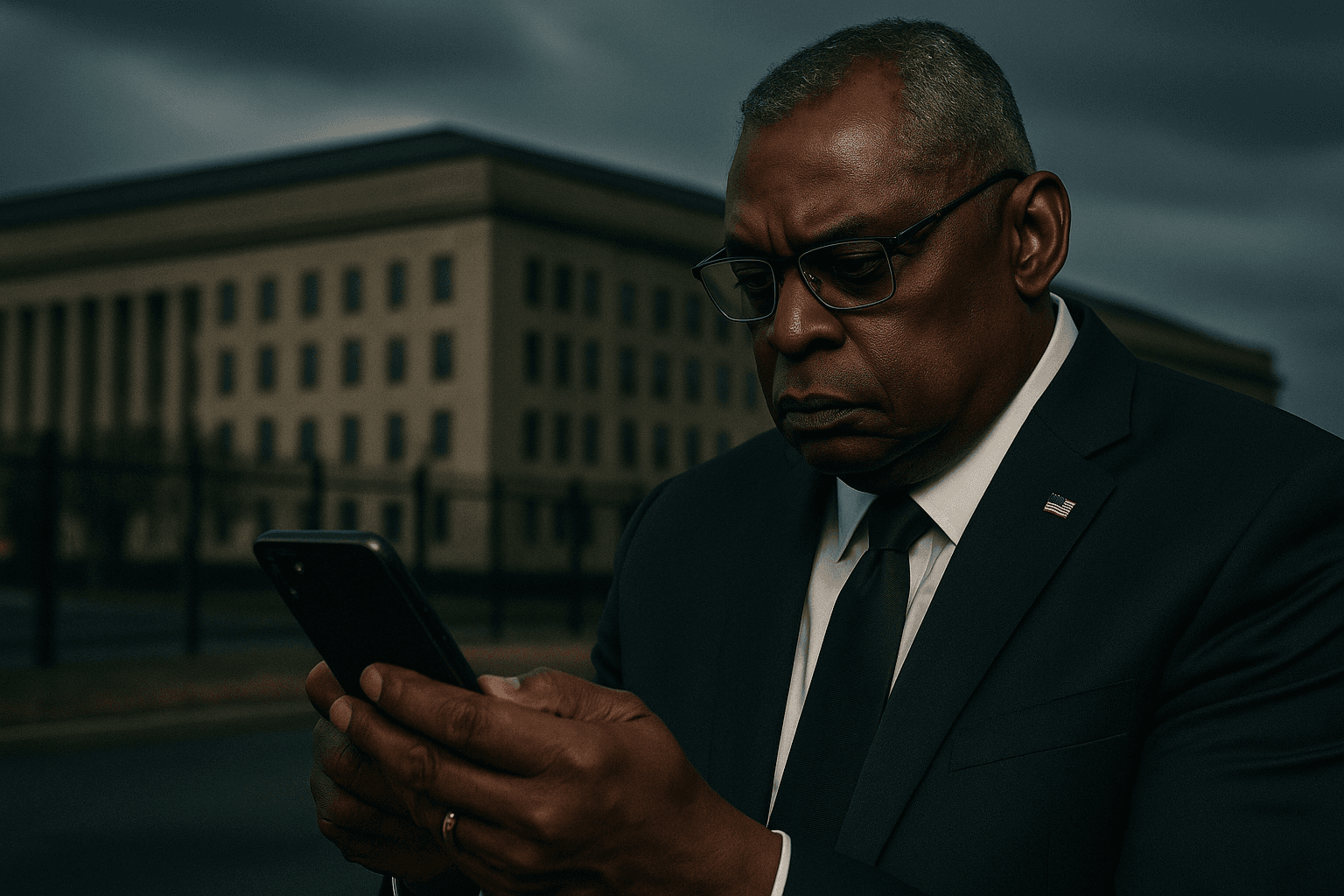
The Pentagon’s Office of the Inspector General concluded in a review released December 3, 2025 that Defense Secretary Pete Hegseth used the encrypted messaging app Signal on his personal device to convey operational timing and mission details about imminent strikes in Yemen. The IG said that the mode of communication and the nature of the material could have jeopardized U.S. troops if intercepted, and that Hegseth’s conduct violated department policy barring official operational coordination on personal devices and unauthorized messaging platforms.
The report stopped short of declaring the information classified at the moment it was shared, noting that the secretary of defense holds original classification authority and may declassify information under certain circumstances. That legal and policy nuance complicated the investigators’ assessment, the review found, even as it stressed the operational risk posed by the communications method. The IG recommended improved training across the department and stricter adherence to secure communications protocols to prevent similar lapses.
Hegseth denied leaking classified material and declined an in person interview with investigators, providing written responses instead. Pentagon spokespeople and the White House emphasized that the IG did not determine that classified information had been improperly disclosed, a point they said undercut suggestions of criminality. Nevertheless the matter drew sharp criticism from some members of Congress who argued that lower ranking personnel would face severe career consequences for comparable conduct.
The episode exposes a difficult tension at the heart of wartime information management. Senior officials possess unique authorities to classify and declassify material, a feature intended to enable rapid decision making. At the same time, departmental rules and long established practices restrict the use of unapproved devices and consumer messaging applications precisely to limit the risk of operational details reaching adversaries or being exploited in real time.
Yemen remains a theater of concern for U.S. military planners and regional partners, where strikes have targeted a range of militant actors in recent years. Operational security in such environments is paramount, officials say, because the disclosure of timing and mission parameters can enable opposing forces to adapt, increase threats to personnel on the ground, and complicate cooperation with allies who share sensitive intelligence.
Beyond immediate force protection questions, the IG review raises broader implications for trust in civilian leadership of the military and for congressional oversight. Lawmakers pressed the department for clarity about what safeguards will follow the recommendations. Analysts said the case could prompt renewed scrutiny of how senior officials use personal devices and apps, and whether existing norms and enforcement mechanisms are adequate to deter risky behavior.
The IG’s recommendations call for reinforced training and more rigorous enforcement of secure communications rules across the Pentagon. As the department weighs its response, the episode is likely to fuel debate about the balance between flexibility for senior decision makers and the strictures needed to preserve operational security and the safety of U.S. forces abroad.
Sources:
Know something we missed? Have a correction or additional information?
Submit a Tip

