Poland Detains Russian National in Major Cybersecurity Probe
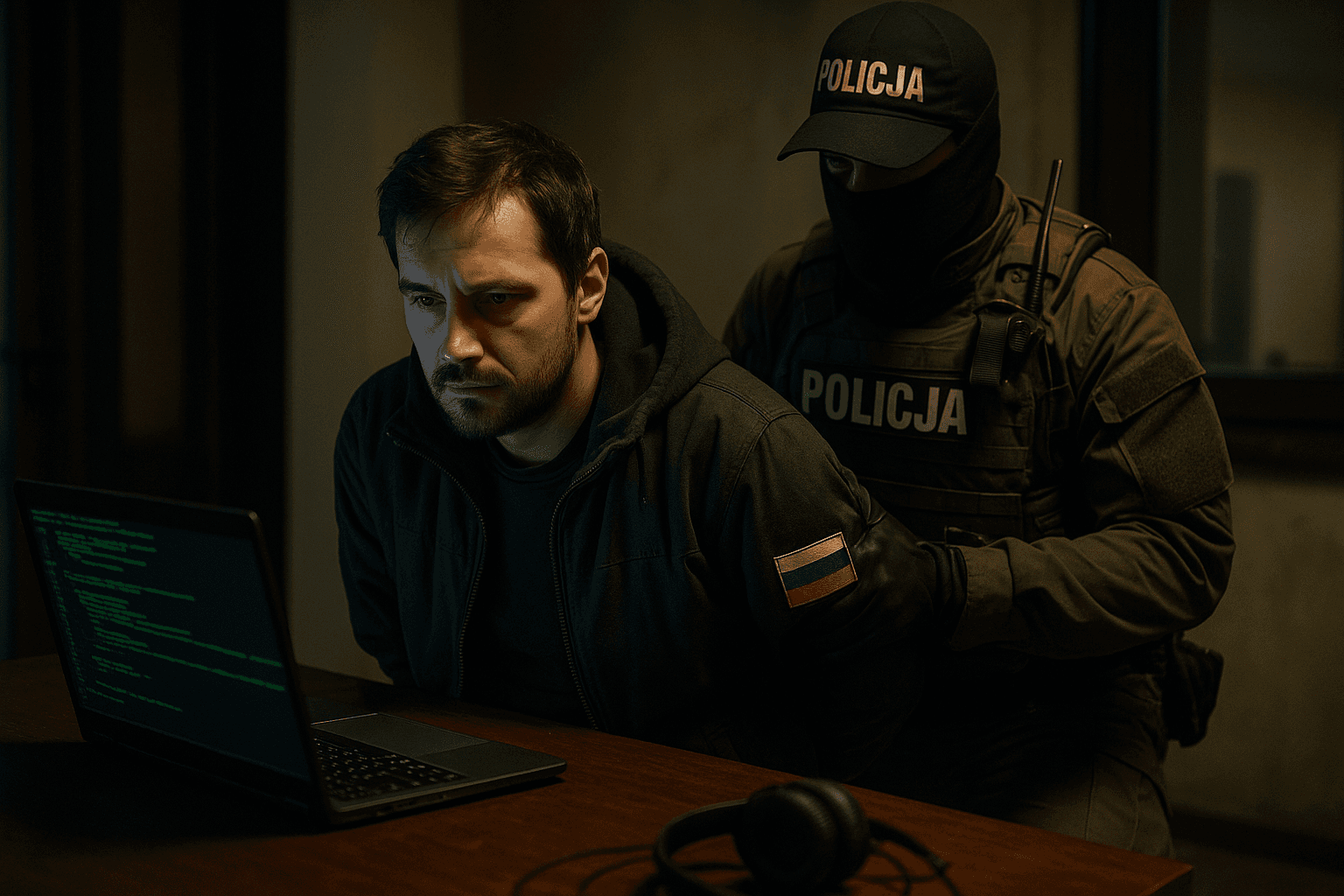
Polish authorities in Krakow detained a Russian citizen on Nov. 27 on suspicion of unlawfully accessing Polish company information systems and breaching databases, Interior Minister Marcin Kierwiński said on social media. The arrest highlights growing European alarm over hostile cyber activity linked to Russia, and it comes as Poland tightens counter cyber measures after a series of sabotage, arson and digital intrusions.

Polish police in Krakow detained a Russian citizen on Nov. 27 on suspicion of unlawfully accessing the information systems of Polish companies and breaching their databases, Interior Minister Marcin Kierwiński said on social media. Authorities declined to identify the companies involved or to specify the precise nature of the data that may have been accessed, citing an ongoing investigation.
The arrest is the latest in a pattern of heightened vigilance across Europe for hostile cyber activity tied to Russian actors since the start of the war in Ukraine. In recent months Poland has increased monitoring of critical networks and expanded counter cyber operations, citing a string of sabotage incidents, arson attacks and computer intrusions that have raised concern among officials and private sector security teams.
Polish authorities are treating the case as a criminal matter with potential national security implications. Prosecutors and cyber forensics teams are reported to be examining logs, server traffic and the pathways used to gain access, while investigators coordinate with domestic intelligence services. Officials have not disclosed whether the suspect acted on behalf of a state actor, a criminal group, or as an independent operator, and attribution in cyber cases remains technically and legally complex.
The decision to withhold company names reflects both investigative prudence and a recognition of reputational and regulatory risks for firms targeted by intrusions. Polish businesses have faced increasing pressure to disclose breaches to customers and regulators, and the absence of public detail on the current case complicates assessments of potential exposure for individuals and commercial partners. Security executives say prompt forensic work can limit further damage and preserve legal remedies, but public authorities often delay disclosure to protect technical leads and prevent copycat activity.
Internationally the arrest is likely to attract attention from European Union and NATO partners who have sharpened cyber cooperation since the conflict in Ukraine. Attribution of cyber incidents often requires multinational intelligence sharing, and legal measures such as mutual legal assistance and extradition can become entangled if suspects are nationals of states with strained relations. Poland’s broader increase in counter cyber measures reflects a regional security calculation that digital aggression is an extension of geopolitical competition.
Legal experts caution that criminal prosecutions for cyber intrusions must balance swift action with due process, including careful handling of digital evidence and the rights of the accused. For Polish domestic politics the episode feeds into broader debates over resilience, deterrence and the role of private sector defensive obligations.
For companies across Central Europe the arrest serves as a reminder that cyber risk is now a central component of commercial and national security. Firms will be watching how investigators proceed, and whether the case yields technical indicators that can be shared across industry to prevent similar breaches. As Poland seeks to harden its digital defenses, the immediate question for observers is whether this detention represents a single criminal episode or a sign of more persistent and sophisticated operations targeting the region.
Sources:
Know something we missed? Have a correction or additional information?
Submit a Tip