Ransomware gangs now threaten executives with physical harm, research finds
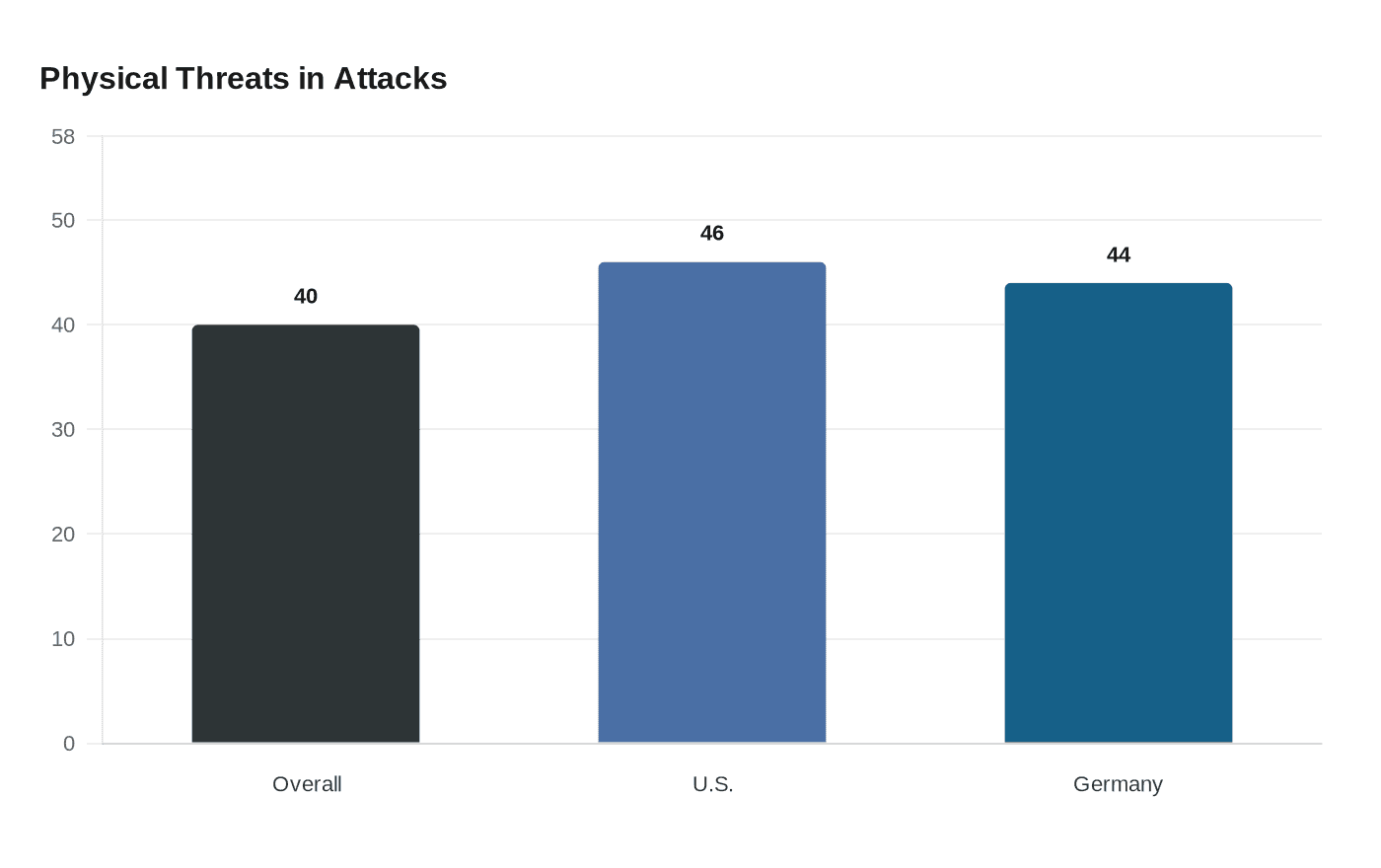
Ransomware crews are escalating from data theft to personal threats, with Semperis finding physical harm warnings in 40% of attacks and 46% against U.S. firms.
The ransomware economy has moved beyond locked files and stolen data. New research cited by Semperis found that 40% of attacks now included threats to physically harm executives when organizations refused to pay, a shift that turns a cybersecurity crisis into a direct worker-safety problem.
The pattern was especially stark for U.S.-based companies, which reported physical threats 46% of the time. German firms were close behind at 44%. The numbers show how extortion crews are using intimidation to increase pressure on decision-makers, raising the stakes for hospitals, schools, utilities and local governments that may have plans for data recovery but not for threats of violence aimed at staff.

That shift is already reshaping official guidance. The Cybersecurity and Infrastructure Security Agency has built tabletop exercise packages that do not stop at ransomware. They also cover civil disturbances, vehicle ramming, insider threats, active assailants, natural disasters, pandemics, industrial control systems, election security and unmanned aerial systems. CISA’s conflict-prevention resources are designed to help critical-infrastructure partners prevent, protect against and respond to potential acts of violence, while two conflict-prevention webinars are offered each month for partners and community members.
Federal law enforcement has been making the same point from a different angle. The FBI says ransomware is a growing threat to the health and safety of the American people, and to national and economic security. Its cyber pages warn that the expanding digital landscape has created a larger-than-ever attack surface for hostile actors, underscoring that the target set is no longer just servers and laptops, but the people responsible for keeping essential services running.
The trend fits a broader criminal escalation described by Europol in its 2026 Internet Organised Crime Threat Assessment. Europol said cybercrime is becoming more sophisticated and that international cooperation is increasingly necessary, a reminder that ransomware crews continue to adapt faster than many defenses.
For organizations that operate power grids, medical networks, school systems and municipal services, the practical lesson is clear. Incident response can no longer be confined to backups, password resets and forensics. It now has to include executive protection, staff safety, crisis communications and coordination with law enforcement before a ransomware demand becomes a physical threat.
Know something we missed? Have a correction or additional information?
Submit a Tip