Ransomware.live reports dozens of victims after multiple gangs post March 2 listings
Ransomware.live says dozens of new victims were named on March 2 as several extortion groups updated public leak sites, underscoring a rising, more personal extortion wave.
Ransomware.live reported that multiple ransomware extortion groups posted dozens of new victims to public leak sites on March 2, naming actors including Qilin, Rhysida, DragonForce, LockBit variants and TheGentlemen. The immediate disclosures add to a pattern of escalating leak‑site activity tracked by security firms and analysts across 2023 to 2026.
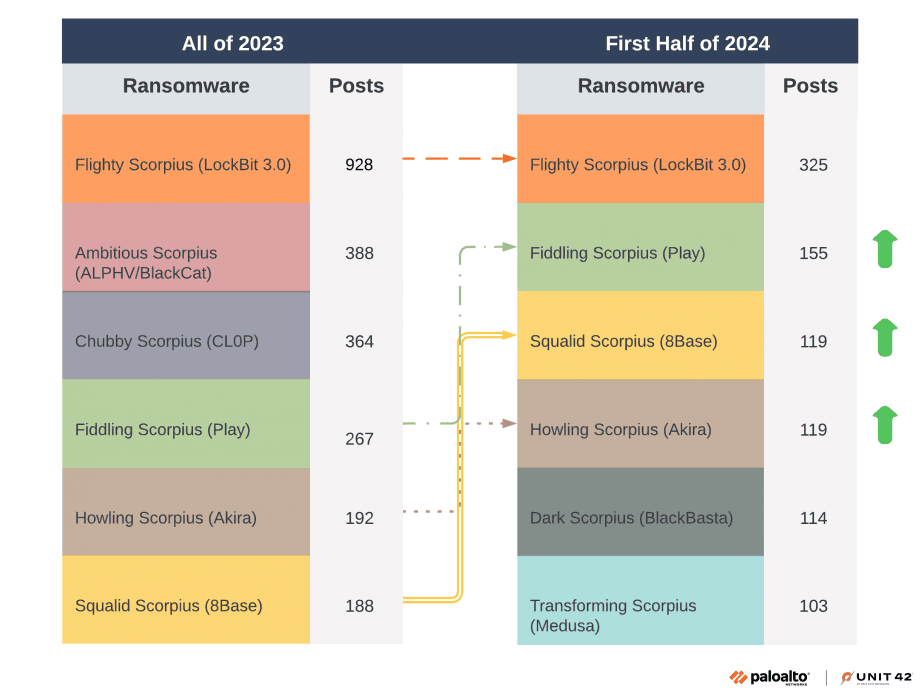
The surge follows sustained growth in leak‑site postings that Unit42 of Palo Alto Networks characterized as part of a "thriving and evolving ransomware landscape." Unit42's leak site analysis found a 49 percent increase in victims reported on leak sites in 2023, totaling 3,998 posts, and documented at least 25 new ransomware groups that year. Unit42 also warned that "Zero-day exploits for these vulnerabilities drove spikes in ransomware infections by groups like CL0P, LockBit and ALPHV (BlackCat) before defenders could update the vulnerable software," citing MOVEit and GoAnywhere managed file transfer flaws as notable drivers.
More recent telemetry reinforces the persistence of the trend. Breachsense, which compiles leak‑site claims, tracked 677 companies listed by ransomware groups in January 2026, an 11 percent rise above its 2025 monthly average. Breachsense said Qilin alone claimed 107 victims that month, representing 15.8 percent of January's alleged targets, with Akira at 71, CL0P at 68 and Sinobi at 56. Breachsense cautioned that these are "claimed victims, not confirmed breaches" and that some listings may be exaggerated or duplicated.
A separate tracker, Breached Company in partnership with Cyble, reported a slightly different January figure of 679 claimed victims and said ransomware attacks had surged more than 30 percent compared with the prior nine‑month average. Breached Company also stated that "Data exfiltration is now part of 74 percent of all ransomware incidents" and that "Triple extortion is now standard operating procedure." The firm added that the January listings included "hospitals that couldn't access patient records, manufacturers whose production lines stopped, government agencies whose services were disrupted, and thousands of employees and customers whose personal information was exposed," illustrating the immediate consequences for critical services and individuals.
ThreatLabz at Zscaler, which analyzed April 2024 to April 2025 telemetry and leak sites, identified RansomHub, Clop and Akira as among the most prolific groups in that window and framed current patterns under the headings "Now trending: extortion, GenAI, and strategic targets" and "Vulnerabilities remain the easy way in." ThreatLabz also urged defenders to adopt "Zero trust: the standard for stopping ransomware."
Analysts at Radiant flagged a worrying shift in attacker behavior. "Threat actors increasingly treat researchers as part of the battlefield, naming them directly, threatening retaliation, and using intimidation to discourage investigation and reporting," Radiant said, and noted that attackers are moving toward closed‑shop crews that control attacks end to end. Radiant described three components of personalization now common in extortion: direct pressure on individuals connected to victim organizations; targeted intimidation of security researchers; and increased insider alignment or misuse of trusted access.
Taken together, the March 2 postings and recent briefs suggest leak‑site churn is rising and extortion tactics are becoming more varied and personal. While law enforcement efforts have had some impact, Unit42 warned the landscape remains fluid. Security firms point to patched vulnerability management, zero trust architectures and heightened monitoring of leak sites as immediate priorities for organizations seeking to avoid becoming the next publicly listed victim.
Know something we missed? Have a correction or additional information?
Submit a Tip