StegaBin attack hid npm command-and-control in Pastebin to steal developer credentials
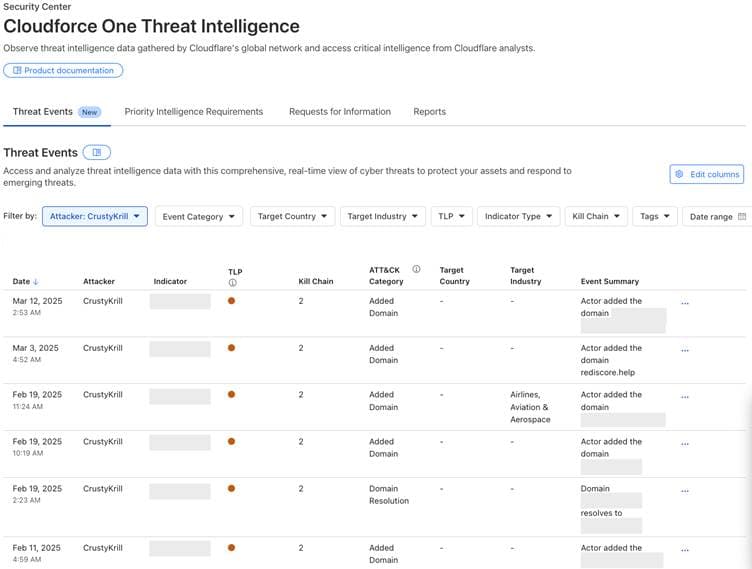
Socket.dev found 26 malicious npm packages published in two days that used Pastebin steganography and Vercel routing to deliver a nine-module infostealer and RAT.

Socket.dev researchers Philipp Burckhardt and Peter van der Zee say their AI-powered systems identified 26 malicious npm packages published over a two-day window that quietly installed a multi-stage credential‑stealing toolkit and a cross‑platform remote access trojan. The campaign, labeled "StegaBin" for its use of steganography, targeted developer environments and flagged Hardhat in its infection chain, underscoring risk to cryptocurrency and Web3 projects.
The attack chain began with typosquatted, look‑alike packages that appear to be developer tools and, in some cases, listed the legitimate library they mimic as a dependency so projects would run normally while a hidden lifecycle script executed. That install script contacted Pastebin and decoded attacker instructions embedded inside seemingly innocuous computer‑science essays. "The loader extracts C2 URLs steganographically encoded within three Pastebin pastes, innocuous computer science essays in which characters at evenly‑spaced positions have been replaced to spell out hidden infrastructure addresses," Burckhardt and van der Zee wrote.
Once decoded, the loader routed to attacker‑controlled infrastructure hosted on Vercel. Socket.dev’s analysis indicates the campaign used multi‑stage Vercel routing; the researchers describe the architecture as a deliberate effort to evade detection and add resilience. Platform‑specific payloads for Windows, Linux and macOS were then fetched, installing a nine‑module infostealer and an interactive RAT. The toolkit includes an FTP exfiltration capability, weaponized TruffleHog scanning to hunt repository secrets, and modules specifically designed to harvest SSH keys, Git credentials and browser secrets.
Socket.dev was able to simulate an infected client because the command‑and‑control infrastructure was live at discovery, allowing them to retrieve the adversary’s post‑exploitation toolkit intact. "Because the campaign's command‑and‑control infrastructure was still live at the time of discovery, we were able to safely simulate a compromised client and retrieve the adversary’s entire post‑exploitation toolkit," the researchers reported.
Persistence and stealth were notable. Several packages write a malicious Visual Studio Code tasks.json file that hides the executable command behind 186 leading spaces so it sits off‑screen; the task is configured to run when a folder opens and will re‑trigger each time a developer opens the infected project directory. At least one previously observed package fetched a next‑stage payload from Google Drive, showing the campaign adapts multiple hosting vectors.
Attribution in multiple research threads ties this activity to a new iteration of the Contagious Interview campaign and to North Korea‑aligned clusters, including FAMOUS CHOLLIMA, though Socket.dev frames the activity primarily as a refinement of tradecraft and evasion techniques rather than a change in motive.
Socket.dev and independent researcher Kieran Miyamoto (kmsec.uk) published overlapping discoveries; Miyamoto disclosed 17 related packages while Socket.dev’s systems flagged 26. Researchers urge urgent defensive steps: treat dependency hygiene as a security control, pin dependencies with lockfiles, verify maintainers before adding look‑alike packages, review new packages for unexpected install scripts and heavy obfuscation, and consider disabling lifecycle scripts in CI and on developer machines when not needed.
Full package names, hashes and takedown status were not included in the initial public notes; Socket.dev and Miyamoto remain primary contacts for indicators of compromise and technical follow‑ups.
Know something we missed? Have a correction or additional information?
Submit a Tip