Cloudflare warns AI and nation-state threats reshape cyberattacks
Cloudflare's 2026 threat report says AI, nation-state groups and record DDoS scale are changing attacks, raising risks to payroll, telecoms and cloud services.
Cloudflare published its inaugural 2026 threat report on March 3, 2026, warning that artificial intelligence, nation-state pre-positioning and DDoS attacks at unprecedented scale are tipping the balance of cyber conflict toward stealth, speed and automation. The company and allied reporters say the changes increase risks to payroll systems, telecommunications networks and cloud services that underpin everyday business operations.
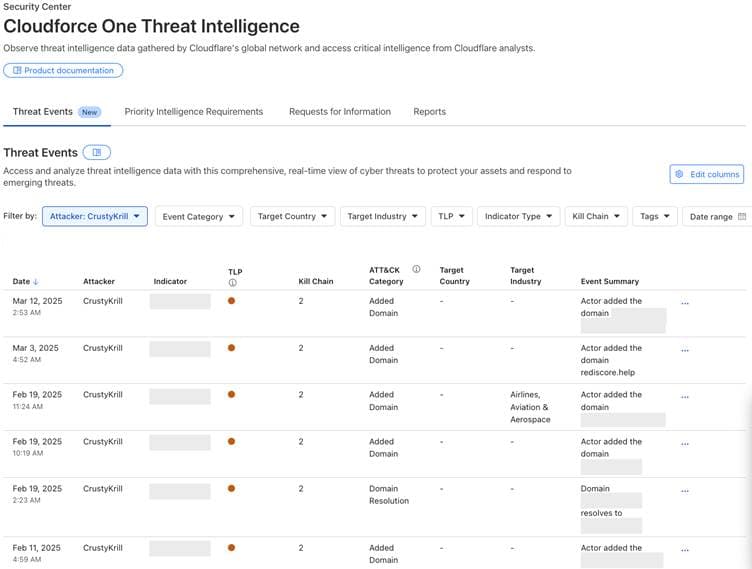
Cloudflare says its Cloudforce One research team and global telemetry informed the findings. The company’s press release and Business Wire syndication state that Cloudflare blocks roughly 230 billion threats on average each day. SiliconANGLE, reporting on the same dataset, gave a slightly higher figure, more than 234 billion threats a day, and said Cloudflare’s network processes more than 20 percent of global internet traffic. Both sets of figures are presented as drawing on Cloudflare telemetry.
A central theme of the report is that attackers are shifting from spectacle to subtlety, preferring to "log in" with abused credentials and trusted flows rather than "break in" with noisy exploits. Cloudflare’s summary warned that “threat actors are using DDoS attacks of unprecedented scale, leveraging AI systems to exploit vulnerabilities, and continuing to strike at traditional weak spots like email to find ways to ‘log in’ versus ‘break in.’” The company adds that “they are not just crashing websites; they are quietly infiltrating payroll systems and tricking software into trusting them,” highlighting direct, financially motivated harms for organizations and employees.
Multiple outlets emphasized the role of AI and large language models in lowering the technical barrier for attackers. Danny Palmer of Infosecurity Magazine summarized the report’s assessment: “Easy access to large language models (LLMs) and other AI tools has significantly lowered the barrier to entry for cybercriminals to conduct effective cyber-attacks rapidly and at scale.” Palmer added that “AI has become a ‘force multiplier’ for cybercriminals, lowering the effort required to carry out campaigns, while also making those campaigns more impactful.”

SiliconANGLE’s coverage supplied additional operational detail and attribution caveats, reporting that alleged China-linked groups such as Salt Typhoon and Linen Typhoon are prioritizing North American telecommunications, government and information technology services for long-term pre-positioning inside critical infrastructure. That outlet also reported North Korean operators running industrialized remote IT worker schemes that use deepfakes and U.S.-based laptop farms to funnel revenue back to the regime. SiliconANGLE framed the trend as cybercrime reaching “full industrial scale” by weaponizing the openness of cloud and software-as-a-service platforms.
Cloudflare and analysts argue defenders must change their posture. Blake Darché, head of threat intelligence for Cloudforce One at Cloudflare, urged organizations to move away from reactive defenses: “Threat actors are constantly changing tactics, finding new vulnerabilities to exploit and ways to overwhelm their victims. To avoid being caught off guard, organizations must shift from a reactive posture to one fueled by real-time, actionable intelligence.” He added that the report should serve as guidance: “This report is a North Star for understanding the scale of attacks, and how threat actor aggression and techniques are shifting. The message to defenders is simple: lead with intelligence or risk falling behind in a race where the stakes have never been higher.”
The report’s practical prescriptions center on identity verification, continuous monitoring and automation to detect and remediate credential abuse and cloud-based command-and-control activity. As the report frames it, defenders who do not adopt identity-centric controls and real-time intelligence risk being outpaced by attackers using AI to scale precision operations against critical services.
Know something we missed? Have a correction or additional information?
Submit a Tip

