Vendor concentration turned 2025 breaches into global cascading failures
Black Kite finds 136 third-party incidents in 2025 affected 719 named firms and an estimated 26,000 more in a "shadow layer," warning boardrooms to act.

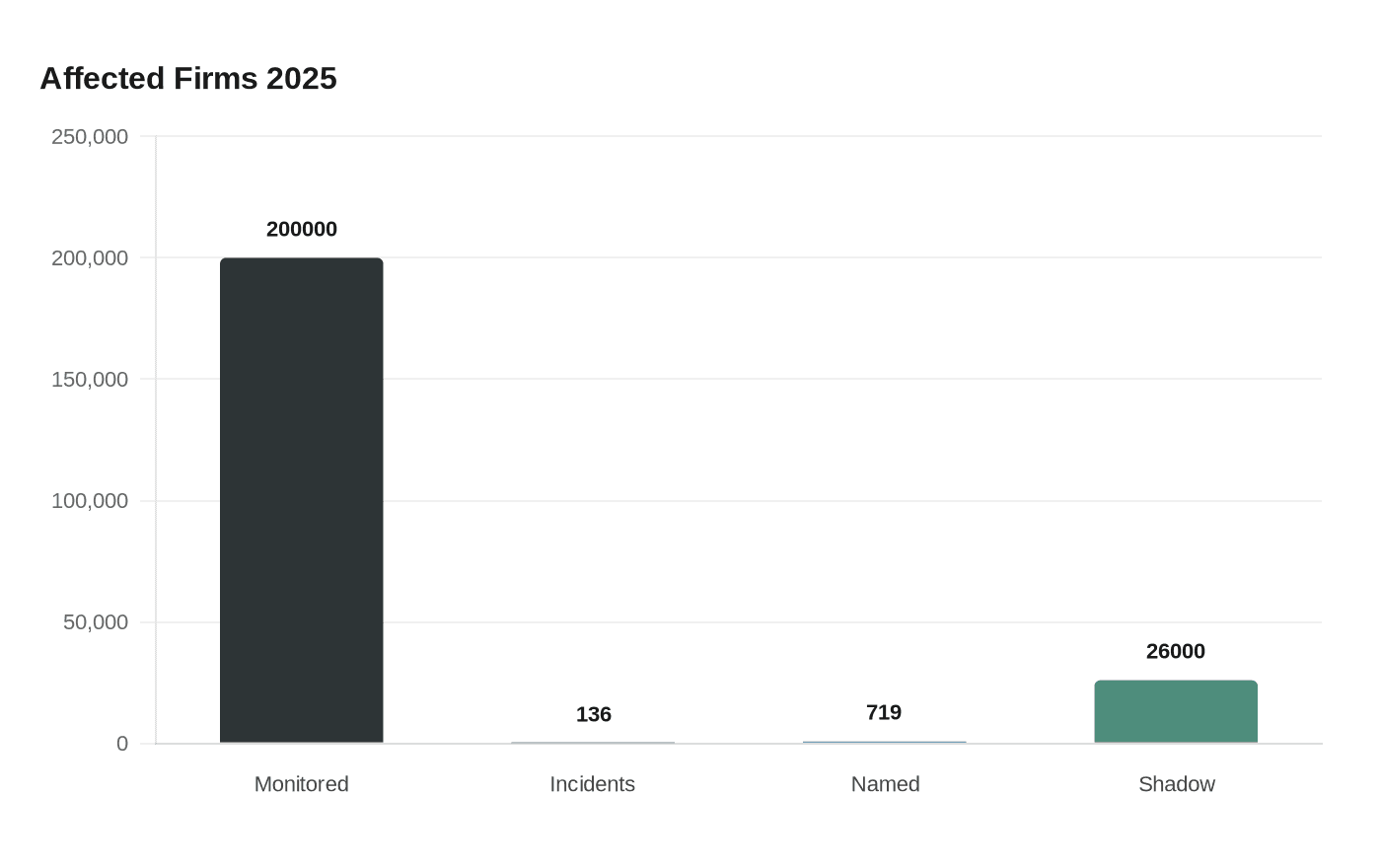
Black Kite’s seventh annual Third-Party Breach Report finds that 136 unique major incidents in 2025 directly affected 719 named companies and created an estimated "shadow layer" of roughly 26,000 additional firms hit between detection and public disclosure. The Boston-based risk firm concludes that concentration among widely relied-upon vendors turned what had been isolated intrusions into system-wide cascades across corporate supply chains.
The report evaluated the cyber posture of about 200,000 companies monitored on Black Kite’s platform and specifically examined concentration risk among the top 50 most relied-upon third parties within the Forbes Global 2000 ecosystem. Black Kite summarizes its central finding bluntly: "Third-party breaches scaled because impact cascaded faster than disclosure, baseline control gaps stayed repeatable, and the most relied-upon vendors remained structurally exposed."
Timing gaps amplified harm. For the subset of incidents where timelines could be reconstructed, the median time to detect an intrusion was 10 days (based on 79 events with timeline data), while the median lag to public disclosure stretched to 73 days and averaged 117 days. The company frames that gap as a transfer of risk: during the interval between discovery and disclosure many downstream organizations were affected but never officially named, forming the report’s "shadow layer."

Black Kite cites a string of vendor-related incidents in 2025 as examples of the mechanism at work, naming F5, Salesloft/Drift, Jaguar Land Rover and Asahi as illustrative cases in which single vendor failures triggered broader operational and reputational damage. The report argues that repeating baseline control failures across vendors turned vulnerabilities into vectors for mass disruption rather than one-off breaches.
The analysis warns that existing third-party risk programs are outpaced by the problem. "Traditional third-party risk management is not keeping pace with the reality of today’s threats. Over the past year, these risks have transformed from a series of isolated accidents into a systematic crisis," the report states. Dikbiyik, speaking from Black Kite’s research group, framed the vulnerability differently: "We can forget about the 'weakest link.' Supply chains are actually most fragile at their highest points of connection." Dikbiyik urged teams to "shift toward active intelligence and systematic awareness" to map where risk concentrates and how it propagates.
Black Kite offers prescriptive steps: map concentration risk across supply chains to identify frequently shared vendors, prioritize mitigation where dependencies cluster, and move from reactive incident response to proactive preparation that speeds disclosure and limits downstream impact. Jeffrey Wheatman, SVP Cyber Risk Strategist at Black Kite, projects the governance consequences: "We predict that supply-chain and third-party cybersecurity risk will move firmly into the boardroom agenda in 2026." Wheatman also flagged a specific corporate threat in the firm’s predictions: "One major manufacturer will suffer an eight-figure financial loss from a supply-chain cyber incident."
The report arrives as security teams and corporate leaders wrestle with how to measure and manage non‑intrusive open-source intelligence ratings, continuous monitoring, and new product-level analyses such as software composition and SaaS subdomain assessments. Black Kite positions these tools as essential to reducing the disclosure gap and breaking the concentration choke points that transformed 2025 into a year of cascading failures.
Know something we missed? Have a correction or additional information?
Submit a Tip

