Vishing Attacks, Data Breaches, and Remote Access Compromises Highlight Latest Cyber Threats
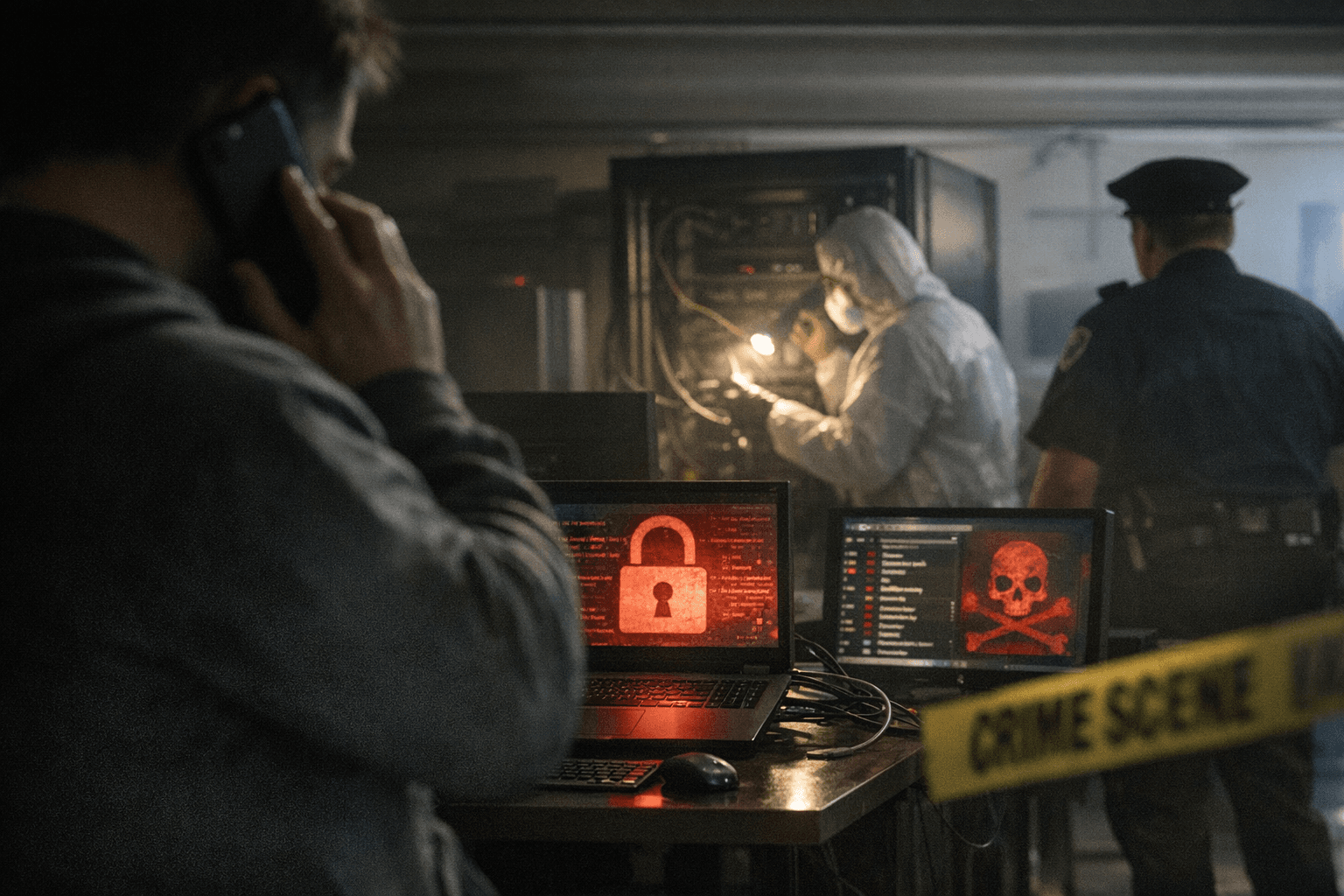
Foster City, California declared a state of emergency after ransomware paralyzed city networks for six days, while a Microsoft Teams vishing campaign tricked employees into handing over remote access using a Windows tool already on their computers.

Foster City's city council approved a state of emergency during a special meeting Monday night, with no Zoom or online access because the network was still shut down. That single detail captures the week's dominant theme in cybersecurity: attackers are not just stealing data anymore. They are switching the lights off.
The Foster City cyberattack was detected in the early hours of March 19, when IT teams identified suspicious activity later confirmed to be ransomware embedded deep within critical systems. The Bay Area city, home to about 34,000 people, forced its city manager to declare a state of emergency to unlock supplementary financial support from outside agencies. The city's 33,000 residents were left to wonder if they were affected at all, with councilmembers advised not to speak publicly about the attack. City Manager Stefan Chatwin urged the public to take precautions to protect personal information, warning that it was possible the hackers had obtained public data.
The municipal ransomware attack arrived alongside a surge in corporate threat activity. Microsoft's Detection and Response Team, known as DART, documented a recent identity-first intrusion that relied less on exploiting software vulnerabilities and more on deception and legitimate tools. After a customer reached out for assistance in November 2025, DART uncovered a campaign built on persistent Microsoft Teams voice phishing, where a threat actor impersonated IT support and targeted multiple employees. Following two failed attempts, the threat actor ultimately convinced a third user to grant remote access through Quick Assist, enabling the initial compromise of a corporate device.
Evidence gathered from browser history and Quick Assist artifacts showed the user was prompted to enter corporate credentials into a spoofed web form, initiating the download of multiple malicious payloads. One of the earliest artifacts, a disguised Microsoft Installer package, used trusted Windows mechanisms to sideload a malicious dynamic link library and establish outbound command-and-control. Forensic analysis ultimately revealed that the attacker's dwell time was limited, no persistence mechanisms were successfully established, and there was no evidence of broader compromise at the directory level.
The week also brought a large-scale data breach affecting millions of people with no connection to corporate IT. Navia Benefit Solutions, a Washington-based employee benefits administration provider, revealed a data breach that may have exposed information of nearly 2.7 million current and former participants. The intrusion was identified around January 15, and an investigation found that attackers had access to its network for about three weeks between December 2025 and January 2026. According to a breach notice filed with the Maine attorney general, 2,697,540 individuals were affected, with compromised data including names, email addresses, phone numbers, and Social Security numbers.
Healthcare records proved equally vulnerable. Trinity Health and the University of Pittsburgh Medical Center notified patients about potential unauthorized access to patient data via a Health Information Exchange. Trinity Health, a not-for-profit Michigan-based Catholic health system operating more than 92 hospitals in 22 states, informed state attorneys general that some of its patients may have had their protected health information accessed without authorization. A proposed class-action lawsuit alleges the breach may have affected about 300,000 individuals and exposed sensitive information. In response, Trinity Health began notifying affected individuals and is providing 24 months of credit monitoring and identity theft protection services delivered by Cyberscout, a TransUnion company.
Compounding the week's disclosures was a critical vulnerability in widely deployed network security software. The flaw, tracked as CVE-2026-20131, is a remotely exploitable deserialization vulnerability in Cisco Secure Firewall Management Center software and carries a maximum CVSS score of 10. While Cisco released a patch on March 4, the Interlock cybercrime group had been exploiting it as a zero-day since at least January 26, pointing to a critical patching gap. Cisco updated its advisory on March 18 to inform customers about the in-the-wild exploitation.
Taken together, the incidents illustrate a threat landscape that increasingly exploits the infrastructure organizations rely on most: their collaboration platforms, their benefits administrators, their hospital networks, and their municipal governments. Trust has become the weak point, with threat actors increasingly exploiting not just software flaws but human trust inside the collaboration platforms people use every day.
Know something we missed? Have a correction or additional information?
Submit a Tip

