Weill Cornell Medicine employee accessed 516 patient records without authorization
A former Weill Cornell employee secretly browsed hundreds of patient records, exposing contact details and visit reasons in a breach now under federal review.

Weill Cornell Medicine filed a breach report with the Department of Health and Human Services disclosing that a former employee accessed the electronic medical records of 516 patients without authorization, according to the HHS submission received February 23.
The institution, a major academic medical center affiliated with NewYork-Presbyterian Hospital, categorized the incident as an "Unauthorized Access/Disclosure" of data held in its electronic medical records system. A spokesperson confirmed the breach in a statement, saying the employee "briefly accessed patient records for reasons unrelated to their job duties and without authorization" and is "no longer with the organization."
The scope of the accessed data appears limited. "The information obtained was limited to contact information and the reason for their visit," the spokesperson said. "No other clinical information and no financial information was accessed."
Weill Cornell said it has notified affected patients and "appropriate authorities," though it did not specify whether those notifications included state regulators, law enforcement, or both. Under New York State's Information Security Breach and Notification Act and federal HIPAA rules, institutions are required to notify affected individuals and regulators within specific timeframes following discovery of a breach involving protected health information.
The institution's own incident response policy, last updated July 24, 2024, lists compliance with HHS's Office for Civil Rights and the New York State notification law among its regulatory obligations. Whether the institution met those obligations within required windows has not been publicly confirmed.
While the data exposed is less sensitive than diagnoses, treatment records, or financial information, the "reason for visit" field in a medical record can carry meaningful privacy implications. Patients seeking care for mental health conditions, reproductive health, substance use, or other sensitive issues may have had that context exposed, even if their formal clinical records were not accessed.
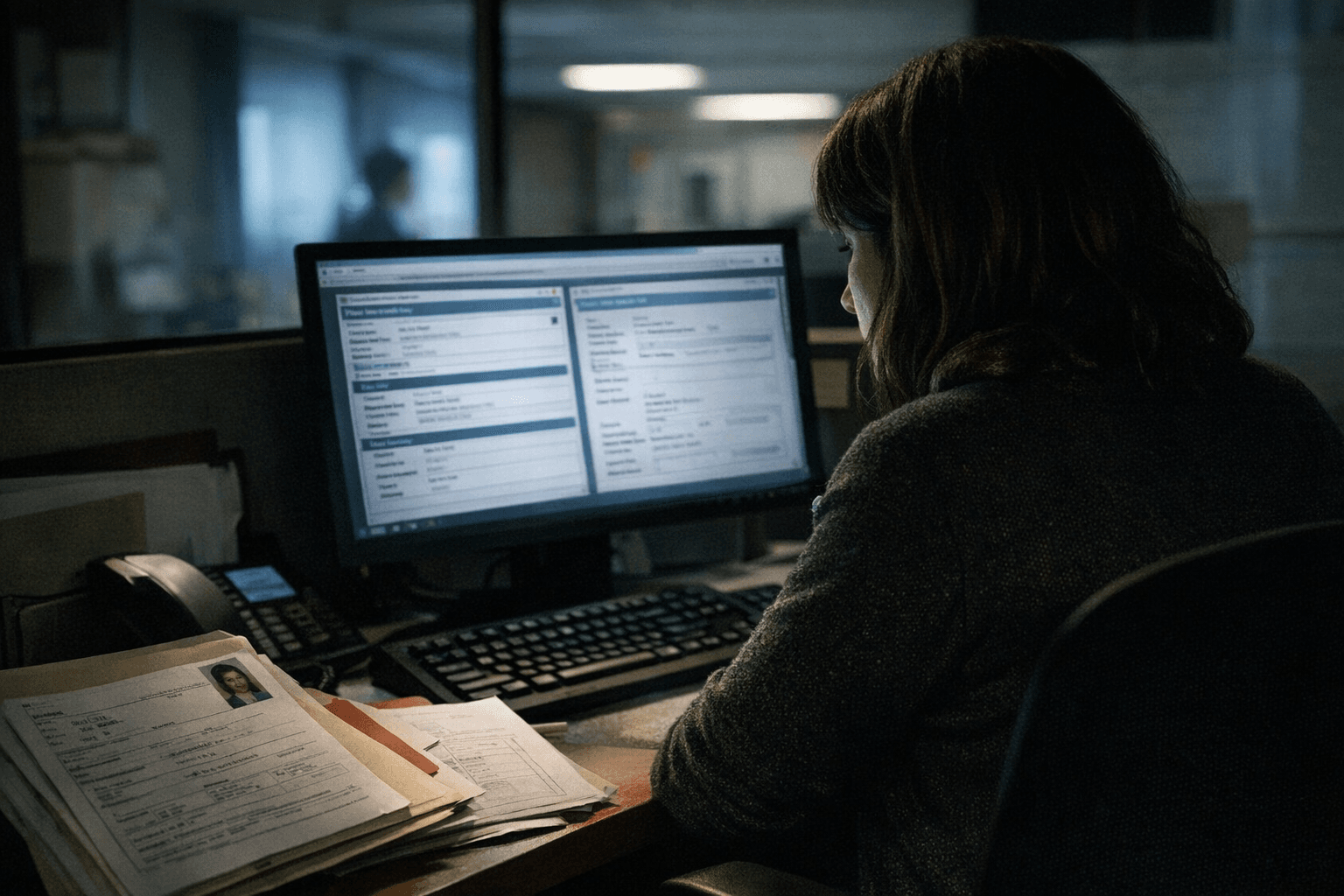
The motive behind the access remains unclear. The spokesperson's statement did not address why the employee accessed the records or whether any data was copied, exported, or otherwise removed from Weill Cornell's systems. The institution said only that it has "established additional measures to help prevent this issue from happening again," without specifying what those measures entail.
Privacy analysts tracking the incident noted that HHS may use this submission as a trigger for a broader compliance review. The more consequential risk to the institution could be a federal audit of its pre-incident risk assessment and internal safeguards rather than the breach itself, which, given the data elements involved, may not have caused direct harm to patients.
This is not the first data security incident Weill Cornell has disclosed. In 2021, the institution reported that a small number of employee email accounts were compromised between September 9 and September 23 of that year, potentially exposing patient names, dates of birth, health insurance information, and in limited cases, Social Security numbers. That incident was attributed to a phishing attempt and did not involve the electronic medical records system.
The 516-patient EMR incident adds to a growing pattern of insider access cases at major health systems nationally, where authorized users exploit system privileges to view records outside their clinical responsibilities. Federal regulators have increasingly treated such incidents as indicators of systemic access control failures rather than isolated employee misconduct.
Know something we missed? Have a correction or additional information?
Submit a Tip

