Home Depot GitHub Token Exposed, Accessed Private Repositories for Over a Year
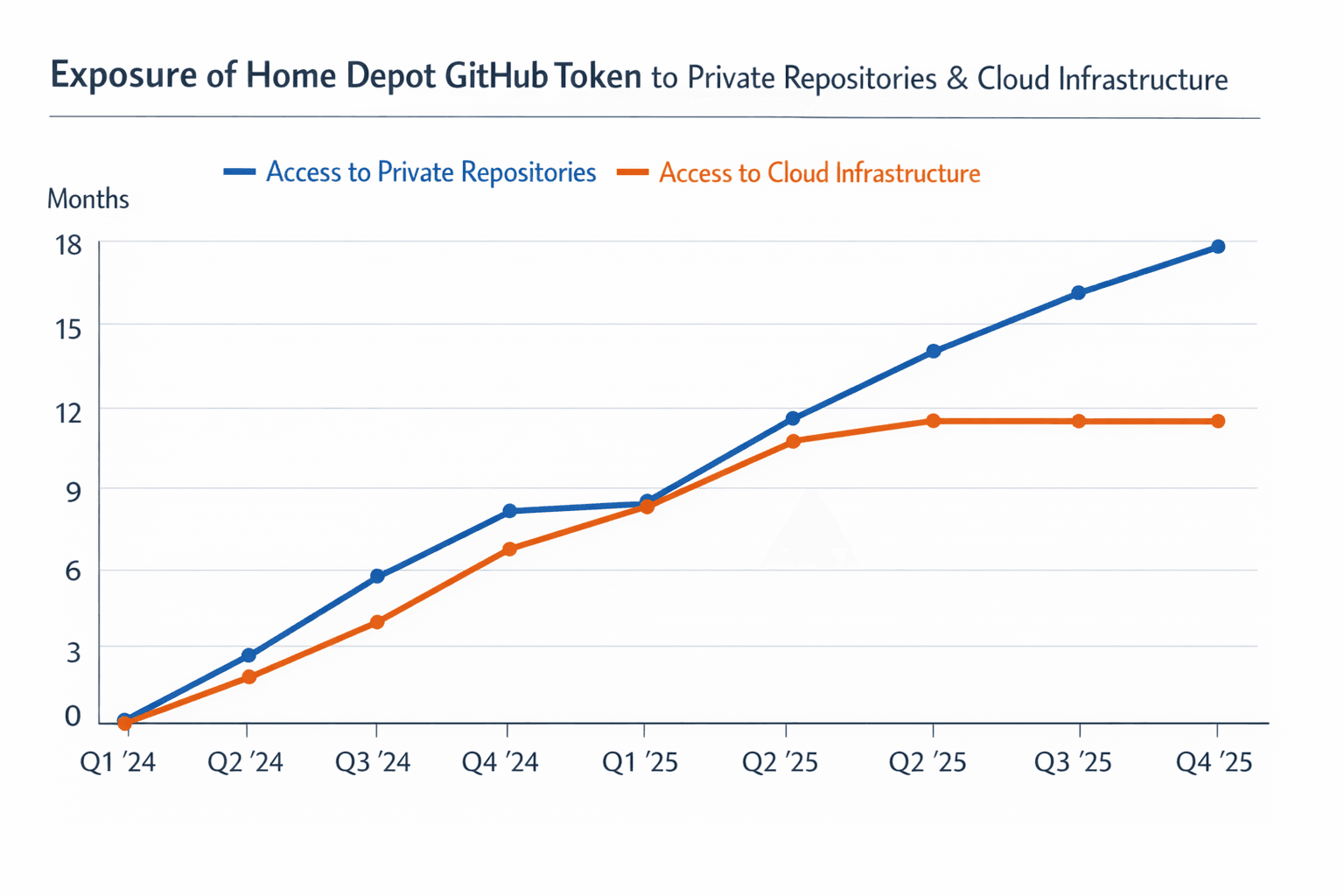
A security researcher found in early November 2025 that a private GitHub access token tied to a Home Depot employee had been publicly available, likely since early 2024, and allowed broad access to hundreds of private source code repositories and connected cloud systems. The credential was revoked only after media outreach in early December, raising questions about the company response, monitoring of leaked secrets, and potential risks to order fulfillment and inventory systems.

A private GitHub access token tied to a Home Depot employee was publicly discoverable for an extended period, a security researcher found in early November 2025. When the researcher tested the credential it granted broad access to hundreds of Home Depot private source code repositories and to cloud infrastructure components, including systems involved with order fulfillment, inventory management and development pipelines.
The exposure likely began in early 2024, and the credential remained accessible until early December 2025 when it was revoked following media contact. The researcher, Ben Zimmermann, reported making multiple attempts to notify Home Depot, including messaging the company and its chief information security officer. Those outreach attempts received no response, and the token was disabled only after public attention increased.

The scope of access reported raises practical concerns for employees and operations staff. Source code repositories include tools and workflows that support store systems, logistics and customer order processing. Access to development pipelines and cloud environments can provide a pathway to alter build processes or to access data used by operational systems. For workers, that could mean disruption to tools they rely on to manage inventory, process orders and support customers, as well as increased scrutiny from internal security reviews and audits.
The incident highlights two persistent risks in corporate technology environments. First, developers and engineers can inadvertently commit secrets into public repositories, creating long lived exposures unless automated secret scanning and access controls are in place. Second, the way organizations handle external vulnerability disclosure matters for preventing and containing incidents. A prolonged lack of response to a researcher who found a high risk credential compounded the exposure period and amplified operational risk.
Home Depot employees should expect internal follow up from security and operations teams, including credential rotation, codebase audits and tighter monitoring of repository access. For workers who operate or depend on digital systems, the event underscores the importance of good security hygiene, prompt reporting of anomalies and clear channels for researchers to communicate potential vulnerabilities.
Know something we missed? Have a correction or additional information?
Submit a Tip