Activision explains TPM 2.0 and Secure Boot requirements for Call of Duty PC players
Activision’s new explainer turns TPM 2.0 and Secure Boot into a real PC gate, with BIOS updates now part of the anti-cheat fight.
What Activision is actually telling PC players now
If your Call of Duty PC keeps throwing security prompts, this is no longer background noise you can ignore. Activision’s refreshed support guidance, updated on April 30, 2026, says TPM 2.0 and Secure Boot are recommended for the best and most secure Call of Duty experience, and that players who have not checked those settings may start running into warnings, launcher prompts, or reduced access if their hardware misses the current standard.
The practical read is simple: these are not just nice-to-have hardening steps anymore. Activision has moved them into the center of the PC security conversation, and the company is treating them as part of the normal setup for fair play rather than an advanced tweak for tech-savvy users.
Why TPM 2.0 and Secure Boot matter in Call of Duty
Activision’s explanation is straightforward. TPM 2.0 is a hardware-based security feature on Windows PCs that helps verify system integrity. Secure Boot helps make sure only trusted software loads when the PC starts up. In plain language, that means the game has a better shot at trusting the machine underneath it before anti-cheat even starts looking around.
That matters because RICOCHET Anti-Cheat is not just looking for obvious wallhacks or a sketchy overlay. Activision says these protections help counter low-level cheats, including tampered systems that try to hide what they are doing from the game. The company’s position is that TPM 2.0 and Secure Boot create a stronger foundation for fair play, especially when cheats try to bury themselves beneath the surface of Windows.
Who is likely fine, and who may get stopped
Windows 11 players are in the easiest spot. Activision says Windows 11 PCs likely already have TPM 2.0 and Secure Boot enabled because the operating system requires them. If you are running Windows 11 on a reasonably current machine, there is a good chance you are already covered without touching a thing.
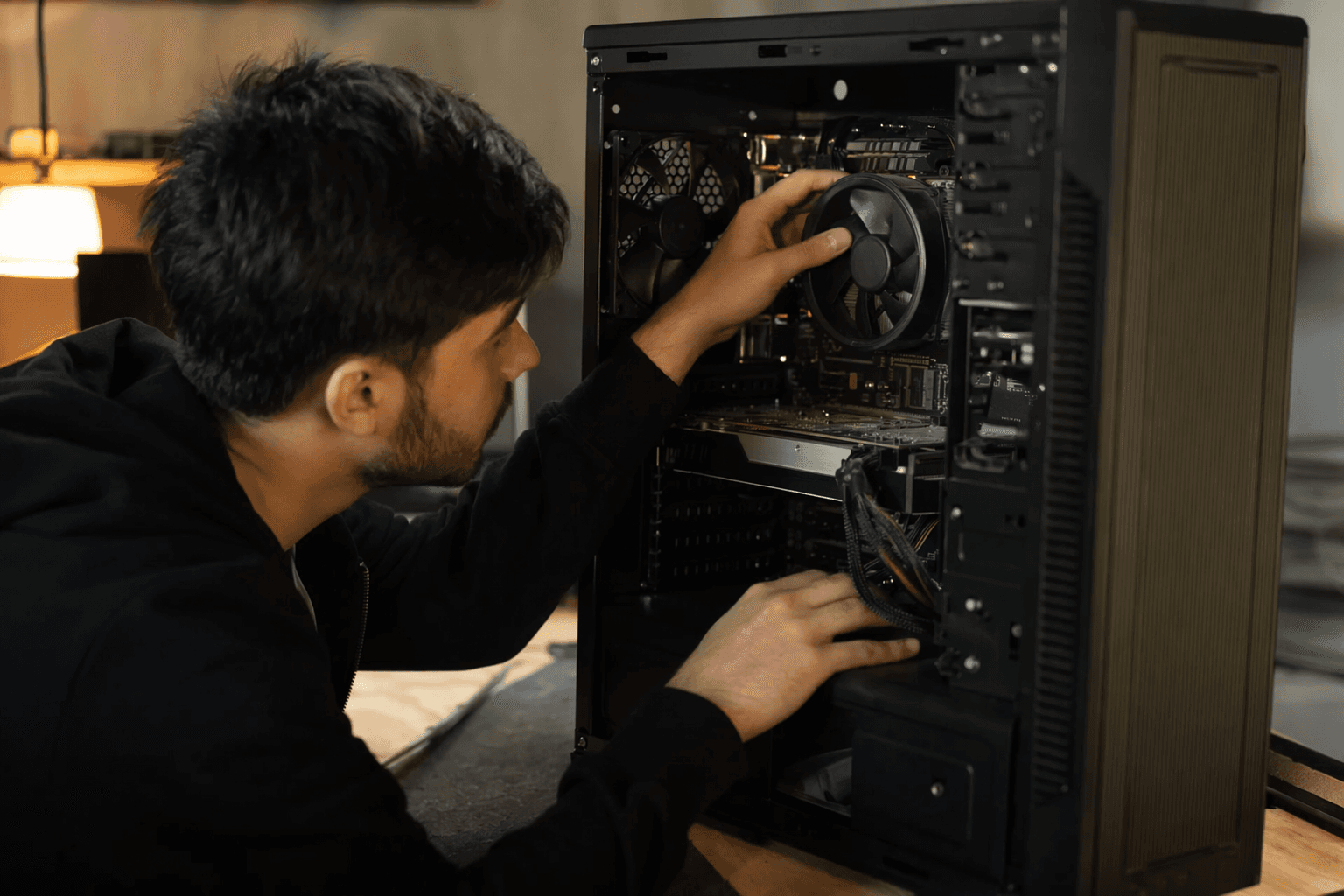
Windows 10 is where the friction lives. Activision says those players may need updates if TPM is disabled or if an older TPM version is active. And even if TPM is technically on, the support page says players who enabled TPM 2.0 but still get prompted may need a BIOS firmware update. That is the part that will catch plenty of people off guard, because the fix is not always a Windows toggle. Sometimes it is a motherboard firmware job, and that means going into BIOS settings and dealing with a motherboard maker’s update process.
The real-world fallout: prompts, warnings, and possible access limits
This is the piece that matters most for everyday players. If your PC does not meet the current standard, Activision says you could see in-game security warnings, launcher prompts, or reduced access. That is not a theoretical future problem either. The company already said in Season 03 that it was rolling out updated in-game notifications for players who did not meet TPM 2.0 and Secure Boot requirements.
That is the clearest sign that this has shifted from a quiet recommendation to an enforced checkpoint. If you are the kind of player who just clicks through launchers and never touches BIOS, this is the moment where that habit starts costing you time. And if you are sitting on an older board, a Windows 10 install, or a custom build that has not been checked in years, you are the exact person most likely to get tripped up first.
How this fits into Team RICOCHET’s larger anti-cheat push
Activision is not presenting TPM 2.0 and Secure Boot as standalone security theater. Team RICOCHET has been tying them into a much broader anti-cheat system that also includes kernel-level monitoring, remote attestation, machine-learning detections, and account enforcement. That matters because the company is clearly trying to catch cheats from more than one angle instead of relying on a single detection method.
Activision has also said it uses Microsoft Azure Attestation to verify TPM and Secure Boot settings through external servers. The company’s argument is that this is harder for cheaters to spoof than local verification, because the check is happening through Microsoft Azure rather than trusting the PC to honestly report its own state. In other words, if someone is trying to feed the game false information about the machine, Activision says the server-side attestation approach is built to make that much harder.
What changed from the earlier RICOCHET messaging
The key difference now is clarity and enforcement. Activision first added these protections with the launch of Season 05 in August 2025, but the current support language is much more direct about what players should expect. Instead of treating TPM 2.0 and Secure Boot like a future-proofing note, the company is now spelling out that players may need BIOS changes, firmware updates, and in some cases newer platform support just to stay aligned with the game’s security baseline.
That shift lines up with the anti-cheat updates that followed. In the Season 05 anti-cheat post, Activision said TPM 2.0 and Secure Boot would be required for Call of Duty: Black Ops 7 on PC when that game launched later in 2025. Later, Activision said the Black Ops 7 PC beta required both features, which confirmed that the requirements were no longer hypothetical. They were being enforced in public, on a real build, before launch.
The motherboard wrinkle: MSI, ASRock, and BIOS trouble
If you are running into TPM prompts even after you think everything is enabled, the motherboard side of the problem may be the real culprit. In Season 05 Reloaded, Activision said it was still troubleshooting TPM 2.0 prompts and noted that MSI and ASRock had released related BIOS or firmware updates. That detail matters because it shows the issue is not always a Windows checkbox problem. Sometimes the fix lives in the motherboard firmware, and sometimes the board vendor has already pushed the patch you need.
That is the part many players will miss. Secure Boot and TPM can be enabled in theory, but an outdated BIOS can still leave the machine in a state where Call of Duty does not like what it sees. If you are on MSI or ASRock hardware, checking the vendor’s BIOS support page is no longer optional busywork. It is part of staying eligible to play without being nagged by the anti-cheat system.
Why Activision is drawing such a hard line
The scale of the crackdown helps explain the pressure. In its anti-cheat progress reports, Activision said it had shut down more than 50 cheat providers and disrupted nearly 300 reseller operations over the prior year. In an earlier update, it said more than 150 cheat resellers had been disrupted or rendered ineffective.
Those numbers tell you why the company is leaning so hard on machine-level protections. Activision is not just trying to catch cheaters after the fact. It is trying to make the PC environment harder to manipulate before cheats even get a foothold. For Call of Duty players, that means the cost of ignoring TPM 2.0 and Secure Boot has gone up fast. If your setup is current, you probably glide through. If it is not, the game is increasingly willing to make you fix it before you get in.
Know something we missed? Have a correction or additional information?
Submit a Tip