RustSec flags two malicious crates with build scripts stealing data
Two new crates were yanked after their build scripts tried to steal data from the build machine. RustSec’s fast advisories show the threat now starts at compile time, not just runtime.
RustSec moved quickly against two malicious crates, mysten-metrics and sui-execution-cut, after both packages were found to include build scripts that attempted to exfiltrate data from the build machine. Both crates were removed from crates.io, and each one had just a single published version, first uploaded on April 20.
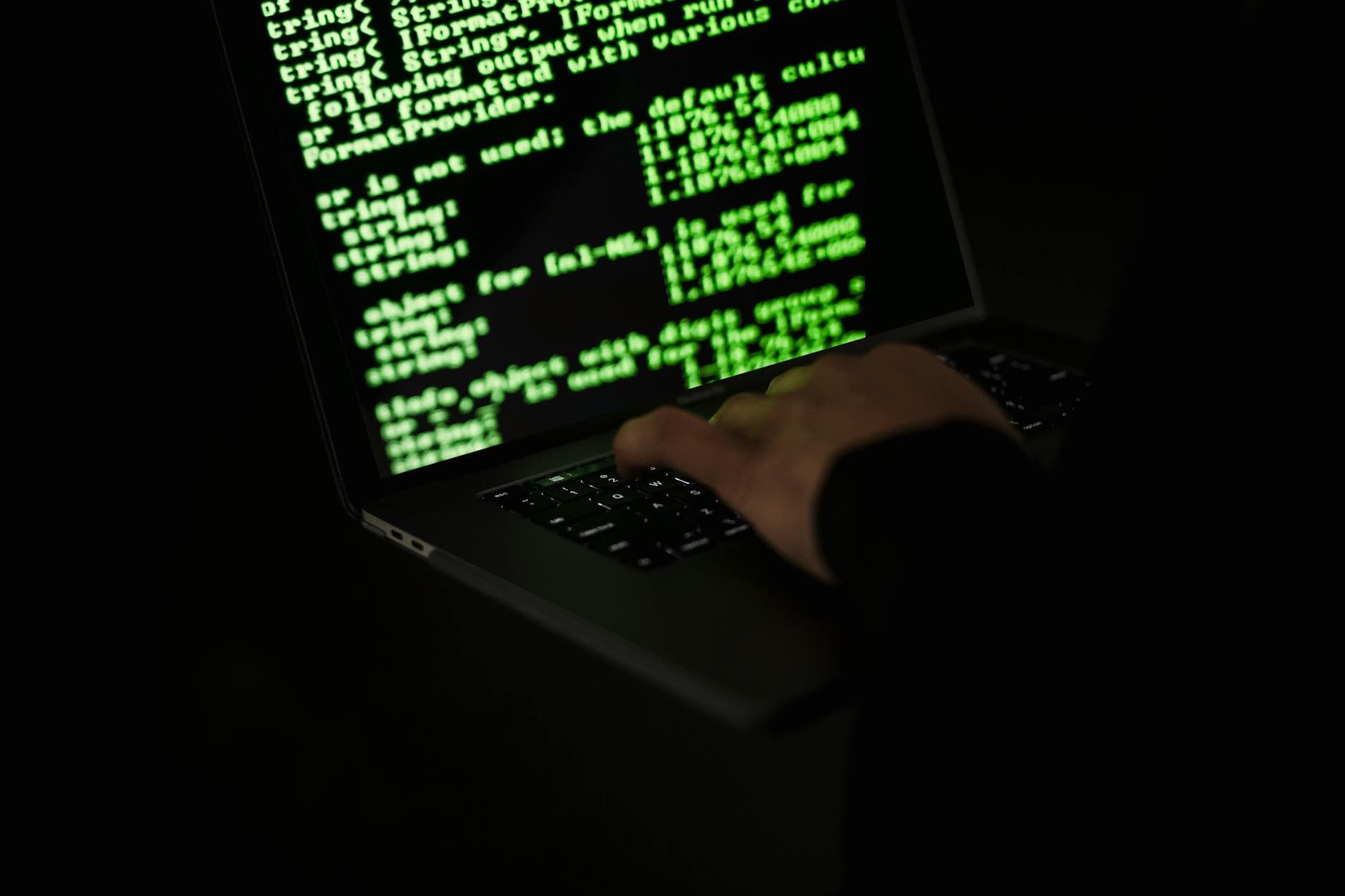
The danger here was not a buggy function or a suspicious API call buried behind feature flags. It was the build step itself. In Rust, build scripts run during compilation, and Cargo also allows code execution through procedural macros, which makes hostile package setup files a serious supply-chain risk. If a crate can run before the rest of the code even lands in your build, the attack surface starts much earlier than many dependency reviews assume.
RustSec’s timeline shows how fast the response moved. The mysten-metrics advisory was reported on April 22 and issued on April 24. The sui-execution-cut advisory was reported on April 23 and issued the same day RustSec published it. Neither crate showed evidence of actual usage, and neither had any dependencies on crates.io. That combination, one version, no downstream footprint, and a malicious build script, is exactly the kind of thing that can slip past casual scanning until a security group catches it.
There were also no patched versions. Once the bad packages were identified, the answer was removal, not remediation. That makes the advisories themselves the durable warning signal, especially after the Rust project changed its public notification policy on February 13, when crates.io said it would stop publishing a blog post for every malicious crate but would still issue a RustSec advisory whenever a crate is removed for containing malware.
The pattern is not new. Rust blog posts in late 2025 documented earlier malicious crates such as faster_log, async_println, evm-units, and uniswap-utils, with some packages deleted shortly after discovery and abusive accounts disabled. The broader lesson has only gotten sharper in 2026: treat fresh crates as untrusted until they have been reviewed, pin them with lockfiles, mirror what you depend on, and keep RustSec monitoring turned on. Dependency graphs can look clean while a build script is already reaching out for data, and that is the kind of attack that memory safety does not stop.
Know something we missed? Have a correction or additional information?
Submit a Tip