AkzoNobel confirms contained cyberattack after Anubis posts sample files
AkzoNobel says a breach at a single U.S. site was contained after the Anubis gang posted samples claiming about 170GB of stolen files; company vows limited impact and notifications.
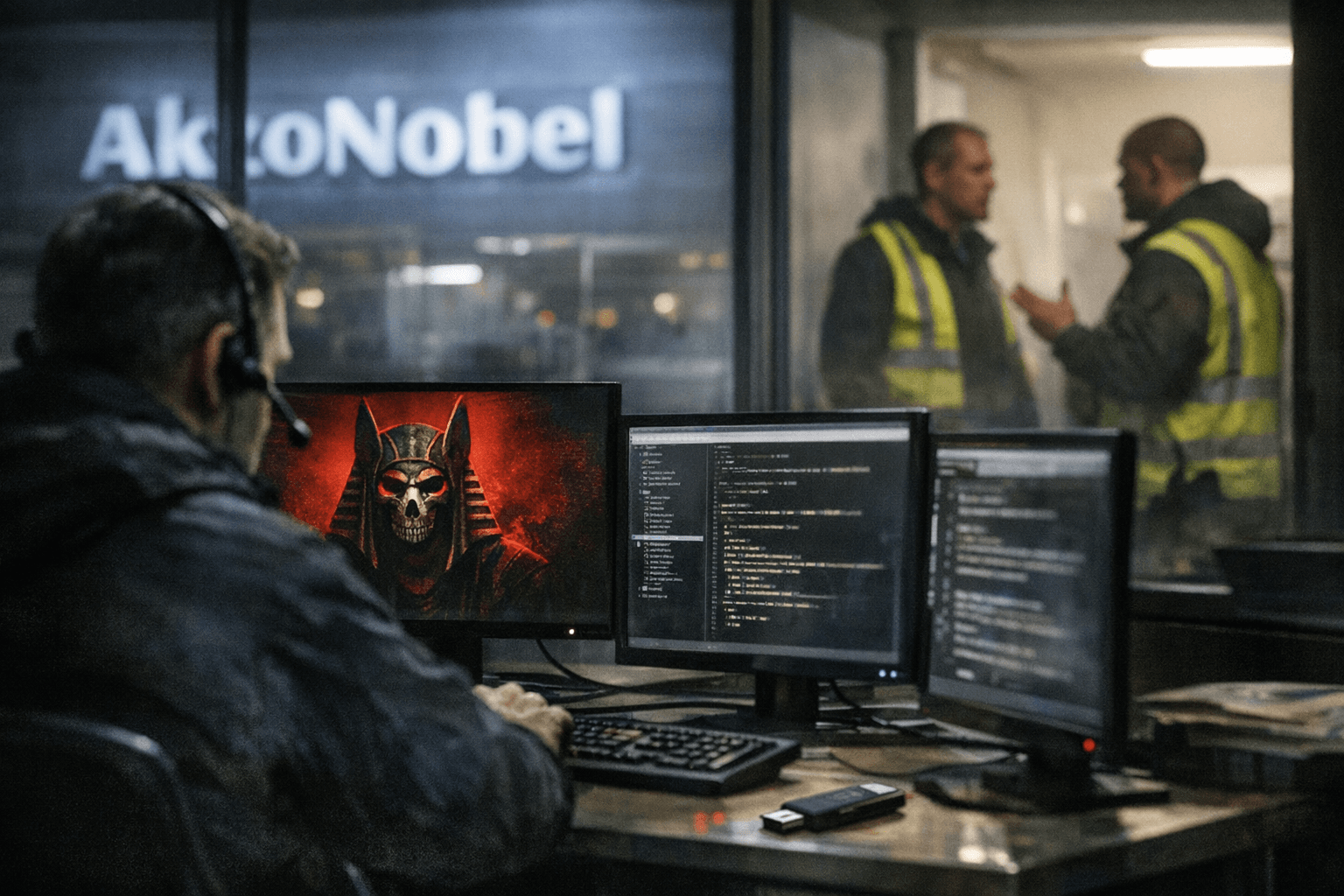
AkzoNobel confirmed a security incident at one of its U.S. facilities after the Anubis ransomware operation listed the company on its leak site and published sample files claiming roughly 170 gigabytes of exfiltrated data. An AkzoNobel spokesperson said, “AkzoNobel has identified a security incident at one of our sites in the United States. The incident was limited to the respective site and was already contained.”
The criminal group’s listing asserts the haul included nearly 170,000 files. Sample items visible on the leak site include screenshots and a file tree and, according to the materials published, confidential agreements with clients, private email correspondence, contact details, passport scans, material testing documents, and internal technical specification sheets.
AkzoNobel sought to reassure customers and markets that the breach was local and controlled. “The impact is limited, and we are taking the appropriate steps to notify and support impacted parties, and will work closely with relevant authorities,” the company said. The multinational paint and coatings maker employs about 35,000 people, reports annual revenue above $12 billion, and operates in more than 150 countries under brands including Dulux and Sikkens.
Key details remain unresolved. AkzoNobel has not publicly identified the precise U.S. site affected, the number or identities of individuals whose data may have been exposed, or whether it engaged with the attackers or paid a ransom. The portion of material the attackers published appears to be only part of what they claim to have taken; whether additional stolen files remain undisclosed on the attacker’s side has not been confirmed.
Security analysts note the Anubis operation has rapidly evolved since it first surfaced in late 2024. The group runs a ransomware-as-a-service model and has promoted an affiliate program that offers large revenue shares to partners. In mid-2025 Anubis added a destructive data-wiper capability that can make recovery more difficult and raise pressure on victims during extortion attempts. Those developments have been linked by experts to a rise in high-impact incidents against large corporate targets.
AkzoNobel said it is working with external security specialists and law enforcement to investigate the incident and to support affected parties. Independent verification of the leaked samples will be important to determine their provenance and scope, and affected clients or employees should expect direct notification if their personal or contractual data is implicated.
The attack underscores persistent risks for global manufacturers: even a breach confined to a single facility can expose sensitive technical information, contractual material and personal identity documents that carry reputational, regulatory and operational consequences. Companies in AkzoNobel’s supply chain and customers named in the leaked samples will likely seek clarity on whether contracts or operations were disrupted and what steps are being taken to protect exposed data.
AkzoNobel’s statement and the Anubis postings leave a narrow window between containment and disclosure. Regulators, customers and affected individuals will be watching for a fuller accounting of the scope, timelines for the intrusion and the company’s remedial actions as the investigation continues.
Know something we missed? Have a correction or additional information?
Submit a Tip

