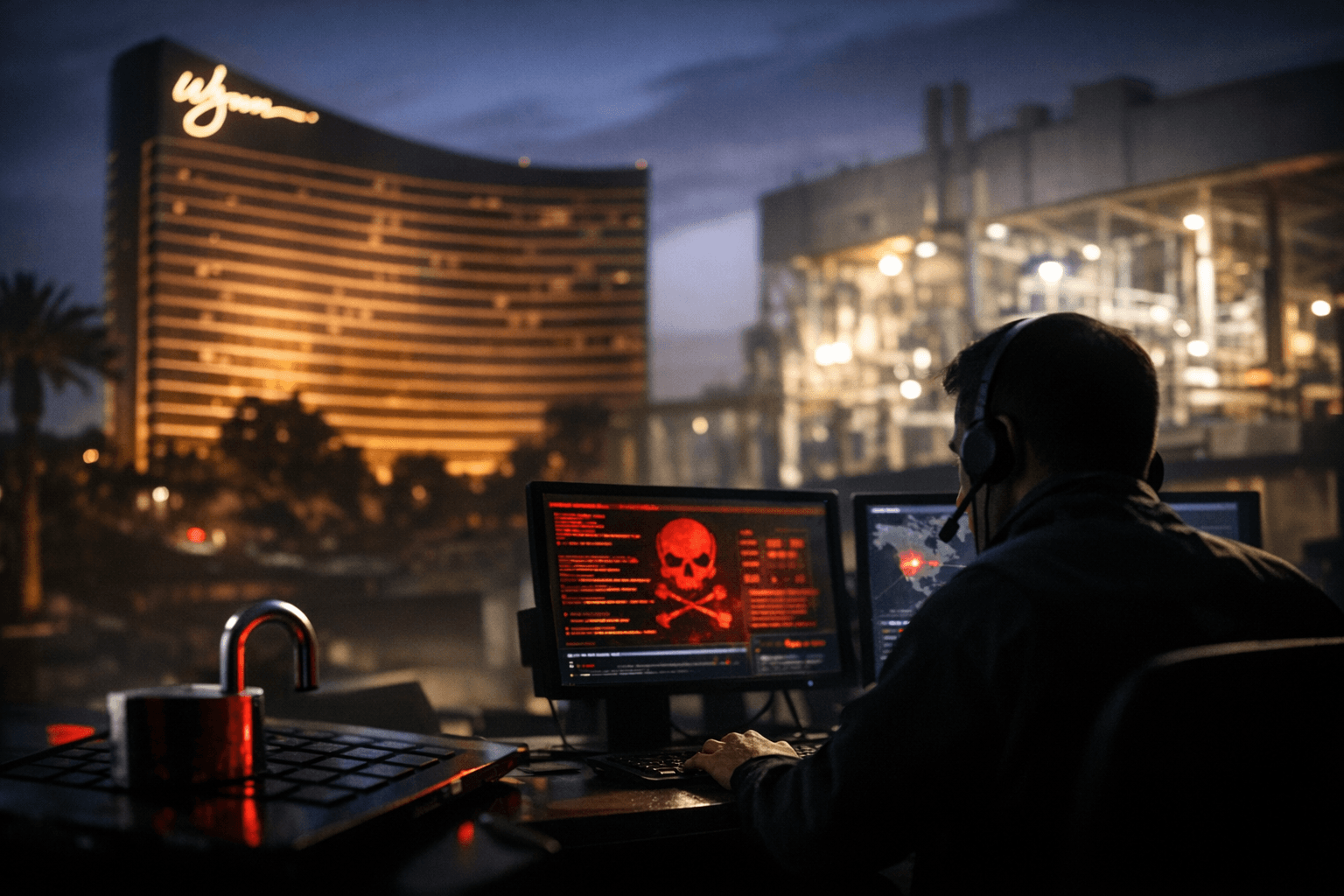
Check Point flags Wynn, UFP Technologies breaches and critical SD-WAN bug
Check Point warns of extortion at Wynn and UFP Technologies and active high‑severity exploits, urging urgent patching and deeper disclosure on several incidents.

Check Point Research’s March 2 threat intelligence roundup consolidated multiple active extortion and data‑exfiltration incidents and flagged high‑severity software flaws that enterprises must address immediately. The bulletin calls out extortion and data theft at Wynn Resorts and UFP Tech while also highlighting ongoing exploit activity in widely used development and management tools.
The company reiterated findings first published in a February 9 Threat Intelligence Report that a ransomware attack claimed by the Qilin group disrupted Romania’s national oil pipeline operator Conpet, taking its website offline while leaving operational technology intact. Check Point quoted Conpet as saying operational technology, including pipeline control and telecommunications systems, remained fully functional and oil transport continued without interruption. Check Point mapped detections for Qilin under signatures such as Ransomware.Wins.Qilin.ta.\ and Ransomware.Wins.Qilin, and recommended use of Check Point Harmony Endpoint and Threat Emulation to help block the threat.
Among the most urgent software flaws cited were two Ivanti Endpoint Manager Mobile vulnerabilities, CVE‑2026‑1281 and CVE‑2026‑1340, rated CVSS 9.8 and described as enabling unauthenticated code injection and remote code execution in in‑house app distribution and Android file‑transfer features. Ivanti issued emergency fixes on January 29 for on‑premises EPMM deployments, and Check Point said its IPS provides protection under the detection name Ivanti Endpoint Manager Mobile Command Injection (CVE‑2026‑1281, CVE‑2026‑1340).
Check Point’s earlier bulletin also warned of active exploitation of a React Native Community CLI and Metro development server vulnerability, CVE‑2025‑11953, an OS command injection flaw that can give unauthenticated attackers remote code execution and “full shell access on Windows.” The research note urged teams to inventory build and development servers and apply patches or mitigations immediately.
The roundup underscored larger trends observed through 2025: DDoS attacks surged 105%, data breaches and leaks rose 73%, and ransomware incidents totaled 451 cases, with groups such as Qilin, Akira, and Cl0p scaling operations through shared tooling and third‑party access. Check Point’s December 2025 telemetry shows organizations averaged 2,027 attacks per organization per week. “This represents a 1% month-over-month increase and a 9% year-over-year increase,” the company said. Regional averages were higher in Latin America (3,065) and APAC (3,017) while Africa averaged 2,752; the education sector was the most targeted in December, averaging 4,349 attacks per organization per week.
Check Point and partners also highlighted identity and access fraud risks. Citing Mandiant, the bulletin described a fresh wave of voice‑phishing attacks targeting single sign‑on tools that have enabled data theft and extortion by enrolling attacker‑controlled devices into victims’ MFA. Silent Push was quoted as saying SSO providers are being targeted by a “massive identity‑theft campaign across more than 100 high‑value enterprises.” In its ThreatsDay commentary Check Point summarized the trend: "Many of the stories point to the same trend: familiar tools being used in unexpected ways. Security controls are being worked on. Trusted platforms turning into weak spots. What looks routine on the surface often isn’t."
Check Point’s published excerpts identified signatures for several ransomware families, including Ransomware.Wins.Akira.ta.\ and Ransomware.Wins.Clop, and urged defenders to prioritize patching Ivanti EPMM, hardening development servers that host React Native tooling, and auditing SSO and MFA enrollments for suspicious activity. The March 2 roundup named Wynn Resorts and UFP Tech in relation to extortion and data exfiltration but did not provide technical details or timelines for those incidents in the excerpts released; Check Point’s full March 2 bulletin and vendor or victim statements will be needed to clarify scope, attribution, and remediation for those cases.
Know something we missed? Have a correction or additional information?
Submit a Tip

