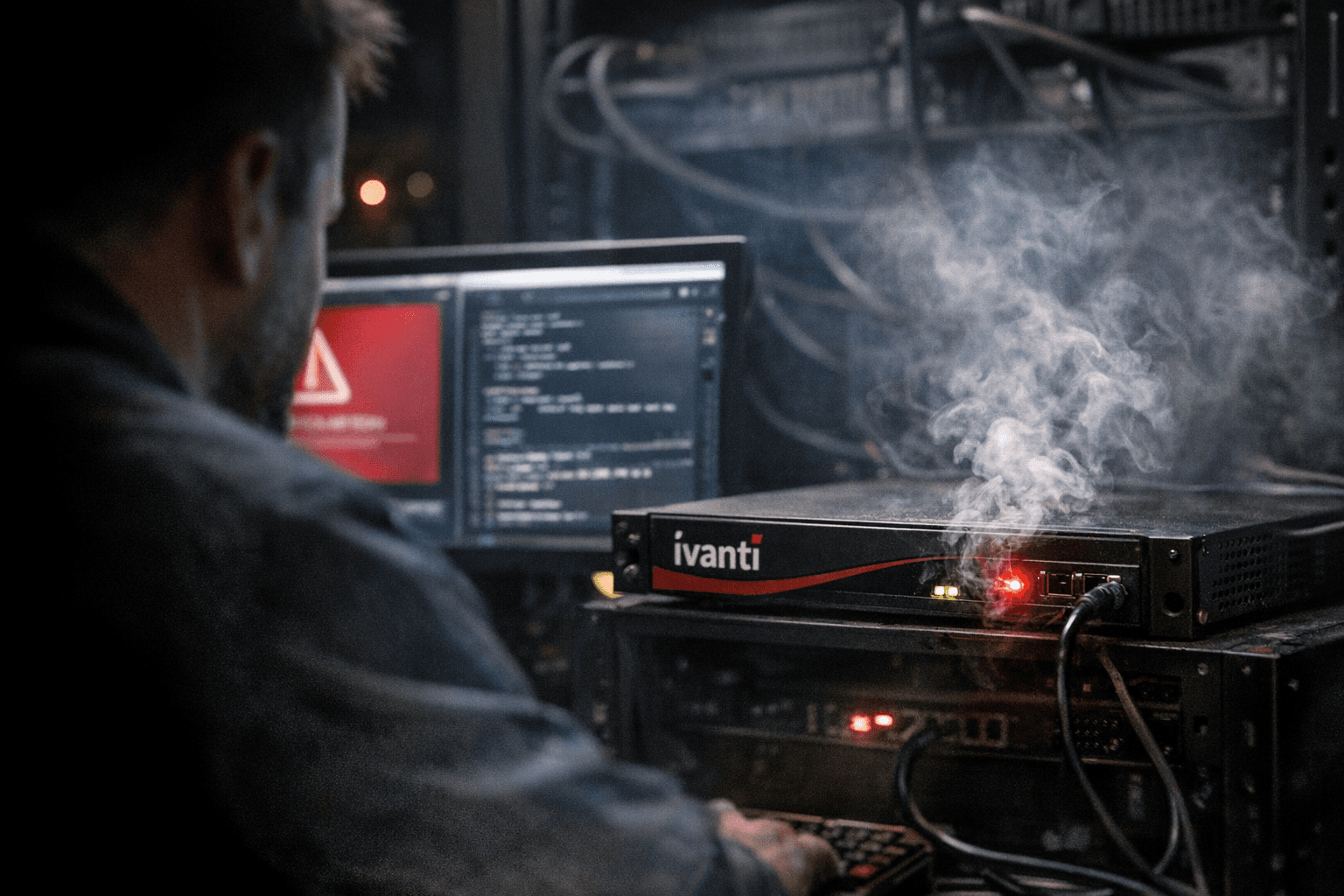
CISA warns RESURGE implant can lie dormant on Ivanti Connect Secure gateways
CISA released an updated Malware Analysis Report saying RESURGE can persist silently on Ivanti Connect Secure devices and activate only when triggered, complicating detection.

The Cybersecurity and Infrastructure Security Agency released an updated Malware Analysis Report warning that RESURGE, a sophisticated implant tied to attacks exploiting CVE-2025-0282, can persist silently on Ivanti Connect Secure appliances and remain dormant until a remote actor triggers it. The alert, amplified by media reporting Feb. 27–28, 2026, cautions that affected networks may harbor undetected implants that evade conventional monitoring.
CISA described RESURGE as a 32-bit Linux shared object that, when present, is injected into the native Ivanti web server process known as web. The implant hooks the accept() call to inspect incoming TLS traffic before the legitimate server handles it, looking for a CRC32 fingerprint in TLS ClientHello messages that identifies attacker connections. If the fingerprint does not match, traffic is forwarded to the real server, masking the implant. The agency also said the threat uses forged Ivanti TLS certificates and advanced cryptographic methods to authenticate covert connections.
The updated MAR presents multiple operational details that make the implant unusually stealthy. Rather than beaconing to an external command-and-control server, RESURGE can wait indefinitely for a specific inbound TLS connection and activate only when that tailored handshake occurs. CISA also characterized the malware as enabling covert Secure Shell based command-and-control access, giving operators remote SSH-style control without obvious outbound signals. The original MAR was published March 28, 2025; reporting and technical summaries on Feb. 27–28, 2026 noted the expanded analysis.
Beyond network-level evasion, the implant includes boot-level persistence tools. Researchers and media accounts report that RESURGE can decrypt, modify, and re-encrypt coreboot firmware images and manipulate filesystem contents to survive reboots and firmware checks. Capabilities cataloged across the reporting include rootkit and bootkit functions, backdoor and dropper behavior, proxying and tunneling, and deployment of web shells for credential theft and privilege escalation.
CISA stressed that the agency expanded the technical detail in the updated MAR to help defenders detect and respond. “By expanding on the technical details in the original Malware Analysis Report (MAR) on RESURGE, we are equipping network defenders with a deeper, more complete understanding of this malware, along with the tools they need to identify, mitigate, and respond effectively,” said Nick Andersen, CISA Executive Assistant Director for Cybersecurity. “Our updated analysis shows that RESURGE can remain dormant and undetected on Ivanti Connect Secure devices, meaning the threat is very much active.” CISA also warned that RESURGE “is engineered to persist silently on compromised systems, remaining dormant until a remote actor connects.”
The updated reporting includes explicit indicators of compromise for defenders to search for; three component hashes published in technical summaries are liblogblock.so - 3526af9189533470bc0e90d54bafb0db7bda784be82a372ce112e361f7c7b104, libdsupgrade.so - 52bbc44eb451cb5e16bf98bc5b1823d2f47a18d71f14543b460395a1c1b1aeda, and dsmain - b1221000f43734436ec8022caaa34b133f4581ca3ae8eccd8d57ea62573f301d. CISA said its MAR contains additional IOCs and detection signatures.
Some community and industry posts link exploitation of CVE-2025-0282 and RESURGE activity to a China-linked actor identified as UNC5221 and trace active abuse to mid-December 2024; the CISA excerpts provided to reporters did not include an explicit actor attribution in the quoted passages. CISA urged organizations to apply the mitigation steps in its CVE-2025-0282 mitigation instruction and to use the updated MAR IOCs and detection resources to hunt for and remove latent implants.
Network administrators running Ivanti Connect Secure appliances should treat the alert as immediate operational risk, check the published IOCs against devices, and follow CISA’s mitigation guidance while seeking Ivanti advisories and patches.
Know something we missed? Have a correction or additional information?
Submit a Tip

