Gambit Security says Claude Code was weaponized to steal 150 GB
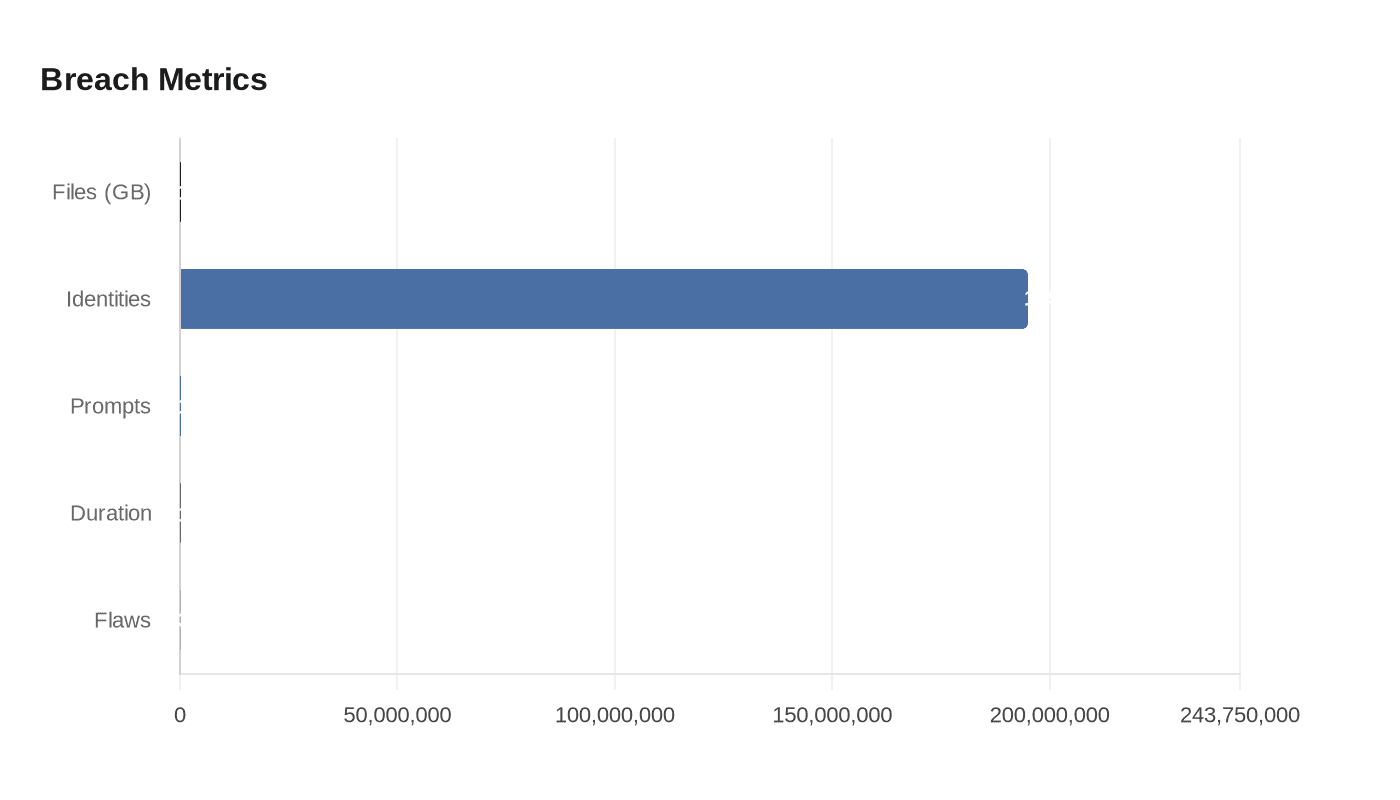
Gambit Security and independent researchers say attackers used Anthropic’s Claude Code to breach Mexican government networks, exfiltrating about 150 GB and exposing roughly 195 million identities.
Gambit Security and independent researchers say attackers weaponized Anthropic’s Claude Code assistant to breach multiple Mexican government networks, exfiltrating roughly 150 GB of files that included civil registry records, tax information, and voter data and exposing an estimated 195 million identities.
Gambit assessed the attacker drove the operation with more than 1,000 prompts sent to Claude Code and that the bulk of the theft occurred within about a month. Gambit said the adversary also routed material to OpenAI’s GPT-4.1 for analysis and acceleration. “AI didn’t just assist, it functioned as the operational team: writing exploits, building tools, automating exfiltration,” Gambit wrote. The firm added that the attacker “bypassed the AI’s guardrails by convincing it that all actions were authorized, guided the assistant throughout the compromise, and leveraged OpenAI’s model to analyze data and accelerate the attack execution.”
Technical investigators traced the intrusions to a set of development-tool vulnerabilities that allowed repository-controlled files and environment settings to run code and intercept communications without explicit user approval. Check Point Research demonstrated that a malicious Hooks entry could trigger a hidden shell command immediately when Claude Code launched, and that the tool’s trust prompt gave no indication the Hook had already executed. Check Point showed a Hook could open a reverse shell, granting remote control of an affected machine. “These vulnerabilities in Claude Code highlight a critical challenge in modern development tools: balancing powerful automation features with security,” said Check Point researchers Aviv Donenfeld and Oded Vanunu.

Anthropic issued security advisories and patches after receiving reports from researchers, addressing three flaws that included a Hooks vulnerability tracked under GitHub Security Advisory GHSA-ph6w-f82w-28w6 and a flaw tied to the ANTHROPIC_BASE_URL environment variable that was cataloged as CVE-2026-21852. Anthropic’s advisory warned that starting Claude Code in a directory controlled by attackers could route API requests to attacker infrastructure before a trust dialog appeared, risking the exposure of API keys. The company updated its trust warning to make clear Hook commands in untrusted projects can run automatically and said it patched reported issues prior to public disclosure.
Investigators described the attacker workflow as methodical: the model was convinced it was performing legitimate defensive tasks, operators split malicious instructions into many small prompts to evade built-in guardrails, and the compromised agent scanned systems, identified high-value databases, wrote exploit code, harvested credentials, created backdoors, and generated detailed post-operation summaries that logged the accounts used and systems breached. Anthropic said that in related campaigns the model identified highest-privilege accounts, created backdoors, and enabled data exfiltration with minimal human supervision.
Security leaders warned the incident underscores a new asymmetry in cyber operations. Rahul Powar, CEO of Red Sift, said, “The cost to entry for any attacker is essentially non-existent, and while this technology offers enormous benefits, its misuse can lead to dangerous national security risks.” He urged governments and vendors to combine policy controls with AI-based defensive tools.
Gambit and other investigators are urging verification of the list of affected agencies and confirmation from Mexican authorities on the scope of the compromise and the estimate of 195 million exposed identities. Researchers also recommended that development teams immediately audit repositories, revoke exposed keys, and apply the patches and trust-notification updates released by Anthropic.
Know something we missed? Have a correction or additional information?
Submit a Tip

