Leaked Persona source maps reveal surveillance-style watchlists, researchers say
Security researchers say Persona exposed internal source maps and infrastructure on Feb. 19, 2026, potentially allowing cross-platform user flagging and raising immediate privacy and regulatory risks.
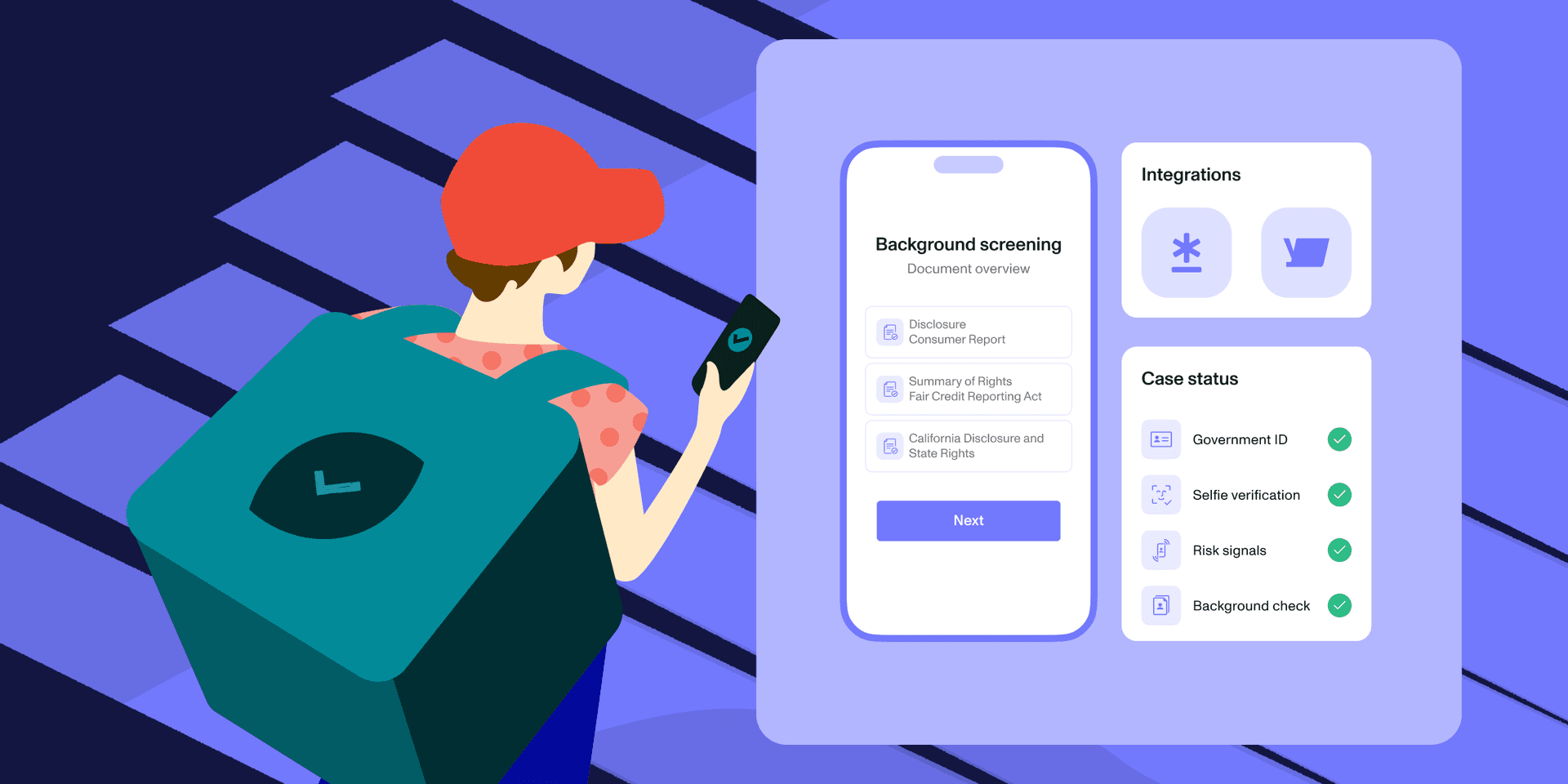
Multiple security researchers published findings on Feb. 19, 2026, alleging that Persona, a widely used identity verification service that powers age checks and KYC flows for major platforms, had exposed internal source maps and infrastructure that revealed a government‑grade, surveillance-style watchlist and the systems that support it. The disclosures have immediate implications for user privacy, vendor oversight, and regulatory enforcement across jurisdictions.
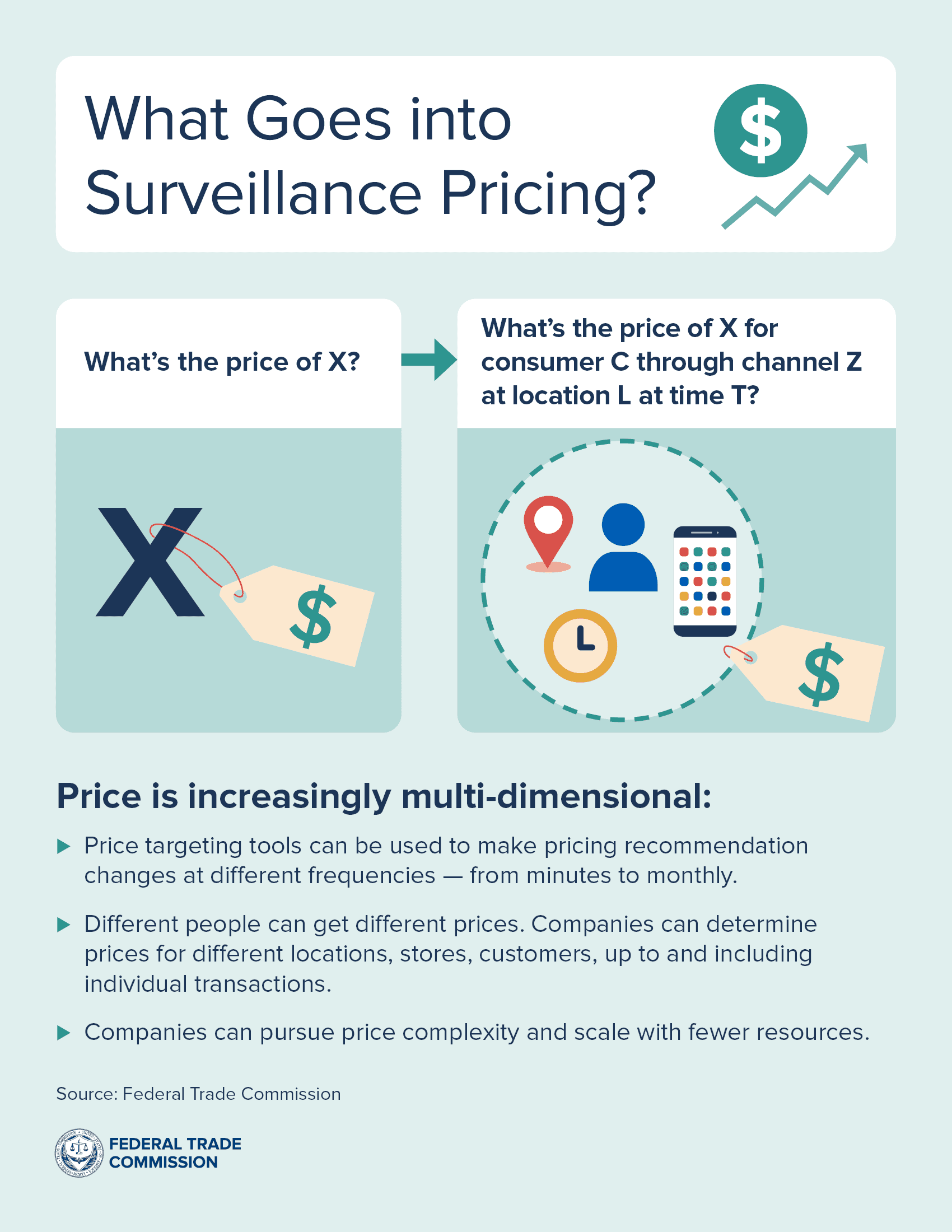
Source maps are developer artifacts that link compressed, minified application code back to readable source code. When left accessible, they can disclose internal APIs, routing logic, configuration files and other metadata that operators intentionally keep hidden from public view. According to the researchers’ analysis, the exposed artifacts in Persona’s repositories show components and naming conventions consistent with centralized watchlist matching, enrichment services and administrative tooling that could be used to flag or classify people across different customer sites.
The practical impact is twofold. First, platforms that embed Persona for routine age checks or KYC may have unknowingly exposed downstream signals to a centralized system that categorizes users. That configuration increases the risk that routine consumer interactions will be linked, aggregated and elevated into watchlist hits. Second, the availability of source maps and infrastructure diagrams lowers the bar for abuse by malicious actors who could map endpoints and behavior patterns that were intended to remain private, creating new attack vectors against user identity data and the vendors that process it.
The episode highlights a gap in oversight of critical third-party vendors. Companies that outsource identity functions often treat those suppliers as commodity services, but the research findings underscore how such vendors can become chokepoints for sensitive data flows. Regulators and contracting agencies face difficult questions about audit rights, disclosure requirements and minimum technical hygiene for vendors handling identity signals for millions of users.
Legal and regulatory consequences could follow. The exposed material will likely raise compliance issues under data protection regimes that require appropriate technical and organizational measures to safeguard personal data. The disclosures may attract scrutiny from authorities responsible for consumer protection and privacy enforcement, and could prompt corporate customers to demand expedited security audits, contract renegotiations or temporary suspension of services.

For civic life, the stakes are concrete. Age verification tools interact with minors and vulnerable populations; KYC flows affect access to online services and financial accounts. If watchlist-style categorization is confirmed, people could face de facto exclusion or increased surveillance without meaningful notice, recourse or transparency. The risk is especially acute for users who rely on anonymity or pseudonymity for safety or political expression.
The immediate remedies are technical and contractual: companies should confirm whether they transmitted any watchlist signals to Persona, conduct code and configuration reviews, rotate exposed credentials where appropriate, and require independent audits of vendor security practices. Longer term, the incident bolsters arguments for clearer regulatory standards for identity vendors, mandatory incident reporting, and stronger vendor management requirements in procurement rules.
The researchers’ disclosures have set in motion a cascade of questions about how identity verification infrastructure is governed and who is accountable when a vendor’s internal tools become a vector for surveillance-style classification. The answers will determine whether privacy protections follow users into the background systems that now power routine checks on age, identity and access.
This article was produced by Prism’s automated news system from verified source data, official records, and press releases, then run through automated quality and moderation checks before publishing. The system is built and supervised by the people who set the standards it runs under. Read our full AI policy.
Know something we missed? Have a correction or additional information?
Submit a Tip