Russia-linked hackers breached 170 Ukraine prosecutors and investigators email accounts
Hackers tied to Russia penetrated more than 170 prosecutor and investigator accounts in Ukraine, exposing email traffic on corruption and collaborator cases.
Russia-linked hackers broke into more than 170 email accounts used by Ukrainian prosecutors and investigators, opening a digital window onto some of the country’s most sensitive corruption and collaborator probes.
The breach matters far beyond ordinary espionage. The compromised inboxes belonged to officials who handle witness statements, draft indictments, evidence summaries and internal strategy, meaning the hackers may have been able to watch how cases were built, who was being pursued and where investigators were under pressure. Keir Giles of Chatham House said the attackers likely wanted to stay ahead of investigators working to expose Moscow’s spies or gather potentially compromising information on senior officials in Kyiv.
Logs and stolen emails that were inadvertently exposed online showed a wider campaign than the Ukrainian cases alone. Data reviewed from the hackers’ server indicated at least 284 inboxes were compromised between September 2024 and March 2026, with most victims in Ukraine and others in neighboring NATO countries and the Balkans. The exposed material included logs of successful intrusions and thousands of stolen emails, pointing to a sustained operation rather than a one-off incident.
Among the Ukrainian institutions hit were the Specialized Anti-Corruption Prosecutor’s Office, the Specialized Prosecutor’s Office in the Field of Defense, the Asset Recovery and Management Agency, and the Prosecutors’ Training Center in Kyiv. At the training center, 44 employee mailboxes were breached, including one belonging to Deputy Director Oleg Duka. Another victim was Yaroslava Maksymenko, who was acting head of ARMA at the time.
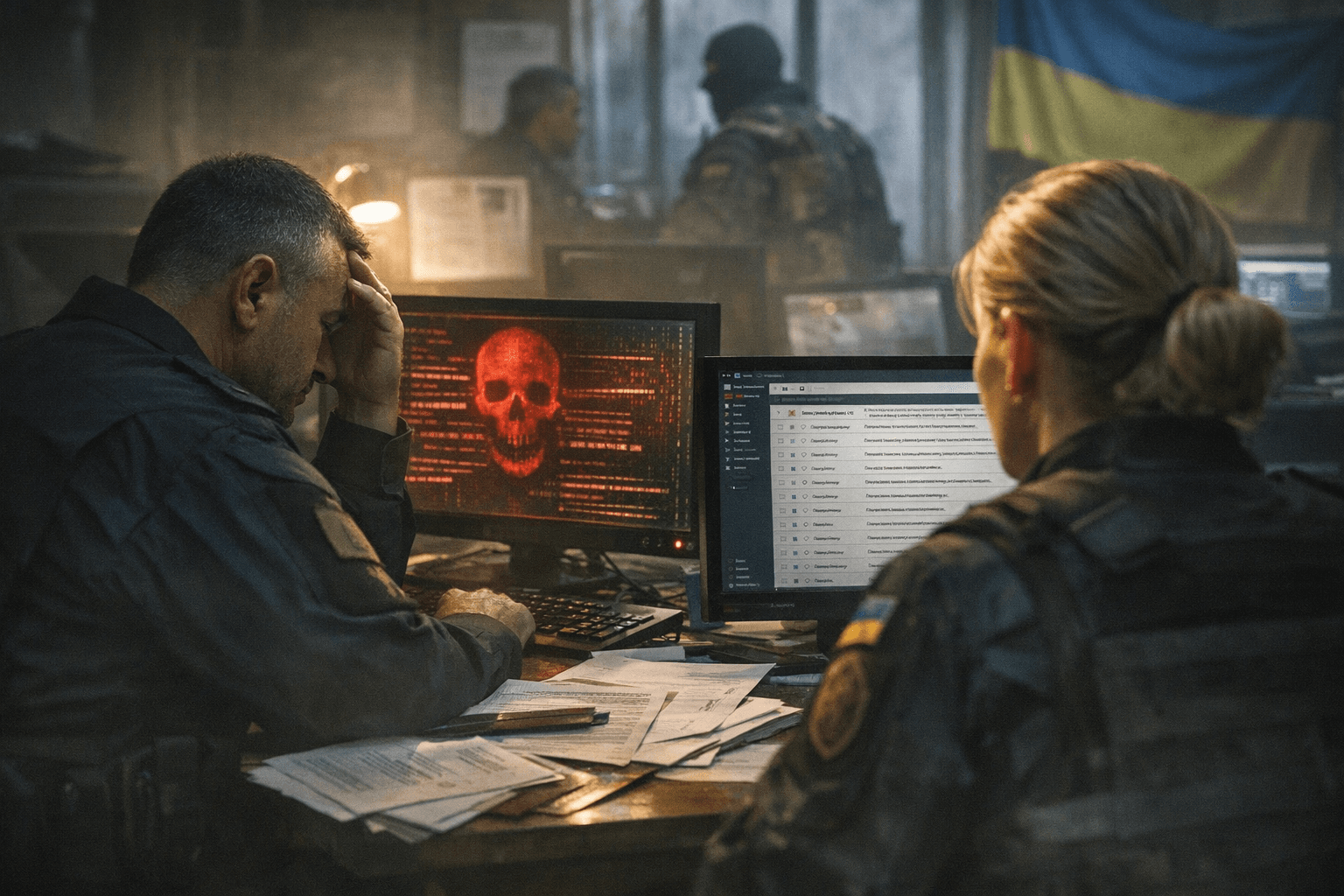
The intelligence value of the breach could be especially high because one senior SAPO official’s inbox contained material tied to several major corruption cases, including one that led to the resignation of presidential chief of staff Andriy Yermak in November 2025. That makes the campaign not just a hunt for passwords, but a direct threat to how Ukraine investigates power inside its own government.
The operation also reached beyond Ukraine’s borders. At least 67 email accounts linked to the Romanian Air Force were compromised, including some connected to NATO air bases. In wartime, that kind of reach underscores a broader Russian effort to map alliances, monitor official communications and probe the institutions that keep both Ukraine’s justice system and its battlefield resilience functioning.
Know something we missed? Have a correction or additional information?
Submit a Tip