University of Hawaiʻi Cancer Center ransomware exposed up to 1.24 million research records
University of Hawaiʻi Cancer Center says a ransomware attack on Epidemiology Division systems may have exposed roughly 1.15–1.24 million research records, threatening decades of study data.

University of Hawaiʻi Cancer Center officials disclosed that a ransomware attack detected on or about August 31, 2025, encrypted research servers that support its Epidemiology Division and potentially exposed roughly 1.15 million to 1.24 million records tied to historical studies and recruitment files. The breach, disclosed publicly in late February 2026, touches sensitive identifiers and research health information collected over decades and raises questions about protections for participants and the integrity of long-running public health research.
“On or about August 31, 2025, UHCC learned that it was the victim of a cyberattack isolated to specific systems that support its Epidemiology Division,” the university said in its incident disclosure. The university said the unauthorized intruder encrypted large amounts of data and “provided proof that it had potentially exfiltrated a portion of that data.” Because of the extent of the encryption, the university said it required months to restore systems and complete a forensic review before assessing the full scope of exposed data.
Public notices and security summaries identify the types of information at risk: names, Social Security numbers, driver’s license numbers drawn from older Department of Transportation records, voter registration records from the late 1990s, and research questionnaires or registry entries that may include health-related information. Counts reported publicly vary; some summaries cite as many as 1.24 million individuals, while others use midrange figures of nearly 1.2 million or about 1.15 million. One detailed release describes a specific 1993 long-running study with 87,493 participant records compromised from a cohort that originally recruited more than 215,000 people. The university’s disclosures do not fully reconcile those differing totals.
The attack was limited to research systems, the university emphasized, and did not affect clinical trials operations, patient care systems, or student records. The university said it disconnected impacted systems, removed the threat actor, notified law enforcement, and retained external cybersecurity firms to lead forensic recovery and review. “Due to the extensiveness of the encryption by the threat actors, it took some time for UH to restore the affected systems and be in a position to assess the impact to data,” the university added. The university also said it “made the difficult decision to engage with the threat actors in order to protect the individuals whose sensitive information may have been compromised.” The university has not provided a public breakdown reconciling the different aggregate counts or stated whether any ransom payment was made; some public summaries indicate payment was used to obtain a decryption tool and assurances data was destroyed, while university statements have not confirmed payment.
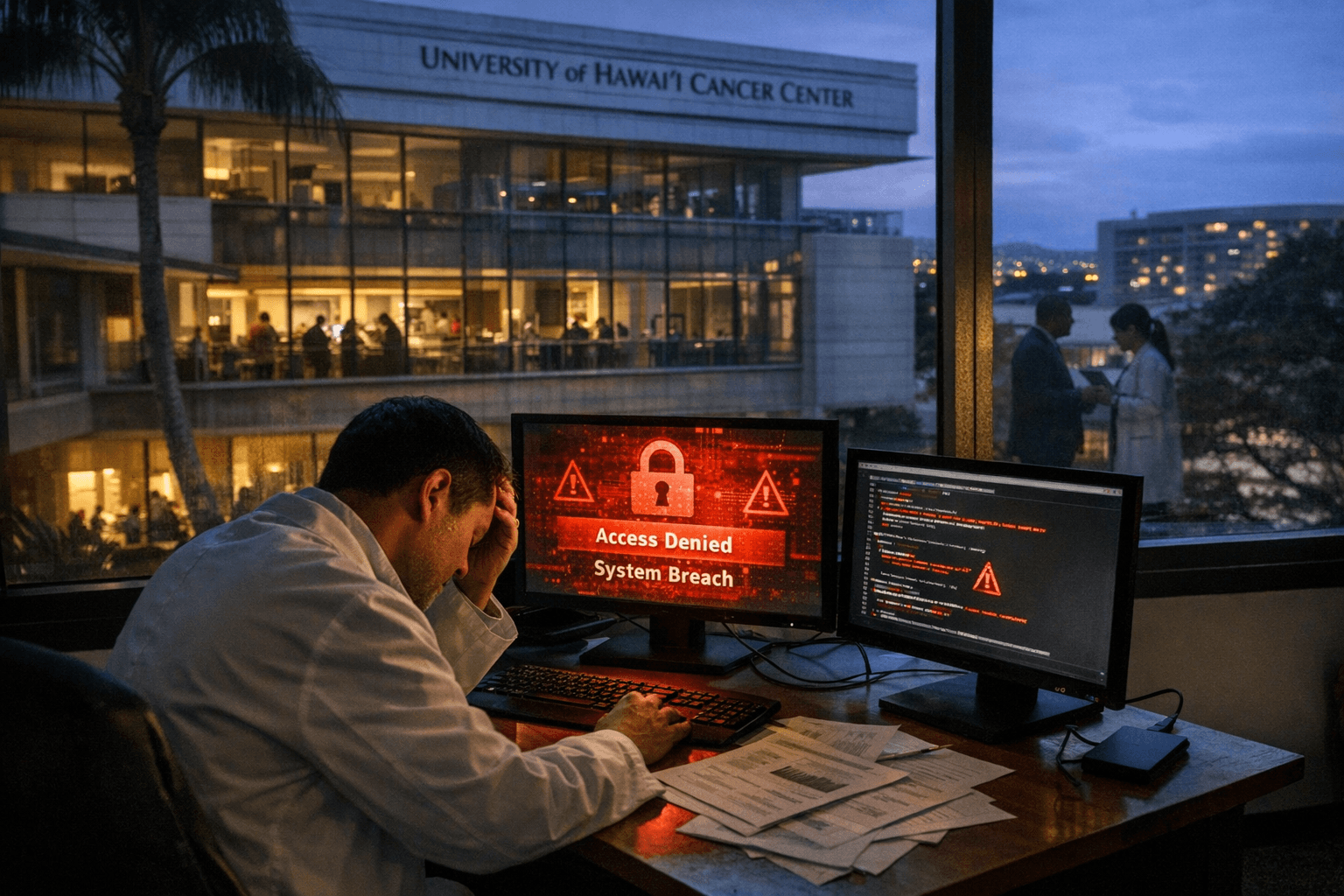
As a remedial measure, the university is offering affected individuals 12 months of free credit monitoring and identity theft protection. Officials report installing technical and governance changes: redesign and hardening of networks, upgraded endpoint protection and monitoring, migration of sensitive research servers to central IT, stricter access controls, mandatory cybersecurity training for Cancer Center staff, and creation of an Information Security Governance Council for Research and an Information Security Task Force to coordinate improvements.
The breach has immediate public health and equity implications. Decades of epidemiologic data are central to understanding cancer risk patterns across diverse populations; the incident could erode participant trust and slow research that informs prevention and care, particularly for communities recruited through long-running cohorts such as the Multiethnic Cohort. The episode also underscores systemic underinvestment in research cybersecurity at academic centers that hold sensitive population health records.
Key unanswered questions remain: an authoritative count of affected individuals, a study-by-study breakdown of exposed fields, whether any stolen data was misused, and whether the university paid for decryption. Those answers will shape regulatory follow-up and whether state or federal agencies open formal investigations. For now the university is focused on remediation and outreach to participants while researchers and public health advocates press for clearer transparency and sustained funding to protect research data that underpin community health.
Know something we missed? Have a correction or additional information?
Submit a Tip