U.S. officials weigh three-day patch deadline as AI speeds cyberattacks
Officials are weighing a three-day patch clock for actively exploited flaws as AI shrinks the gap between discovery and attack. The question is whether agencies can move faster than their own procurement cycles.

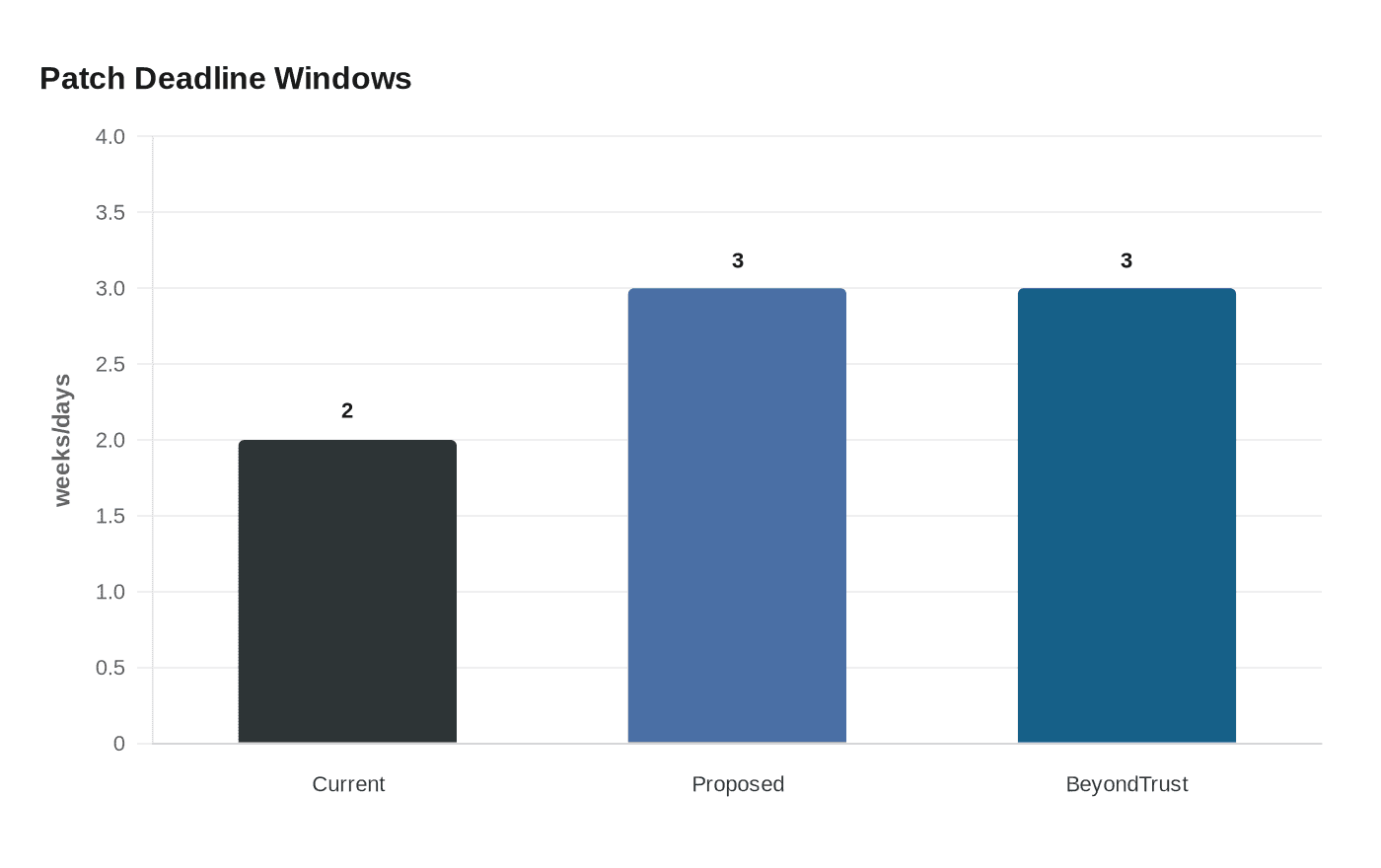
Federal cybersecurity officials are weighing a sharp shortening of the deadline for fixing actively exploited software flaws in civilian government systems, from two weeks to three days, as AI tools compress the time between disclosure and attack. The move would put even more pressure on agencies already expected to move quickly when a vulnerability lands in the Cybersecurity and Infrastructure Security Agency’s Known Exploited Vulnerabilities catalog, the government’s authoritative list of flaws exploited in the wild.
The discussion is being driven by Nick Andersen, CISA’s acting head, and Sean Cairncross, who was confirmed by the Senate as national cyber director on August 2, 2025. The White House says the Office of the National Cyber Director is the president’s principal cybersecurity policy shop. If the three-day standard is adopted, it would likely accelerate testing, procurement, and remediation workflows across federal civilian agencies, while also signaling that Washington views AI-enabled exploitation as an immediate operational threat rather than a future one.
CISA already uses aggressive deadlines when it sees active abuse. Its Binding Operational Directive 22-01, issued on November 3, 2021, requires federal civilian executive branch agencies to remediate KEV-listed vulnerabilities within prescribed timeframes. On April 20, 2026, CISA added eight known exploited vulnerabilities to the catalog and set remediation dates of April 23 and May 4, 2026 for different entries. In February 2026, the agency ordered federal agencies to patch an actively exploited BeyondTrust flaw within three days, showing that the compressed window is already in use for some critical cases.

The policy debate comes as Anthropic and other AI developers have raised new alarms about offensive cyber uses of large models. Anthropic’s April 2026 research on Claude Mythos Preview focused on cybersecurity capabilities, and the company also said it disrupted an AI-orchestrated cyber espionage campaign that used Claude Code in part to execute attacks at scale. Stephen Boyer, founder of Bitsight, said, “We don’t have as much of a window as we used to have,” capturing the core problem for defenders: the attacker’s clock is getting faster, and government patching systems may not be keeping pace.
Sources:
Know something we missed? Have a correction or additional information?
Submit a Tip