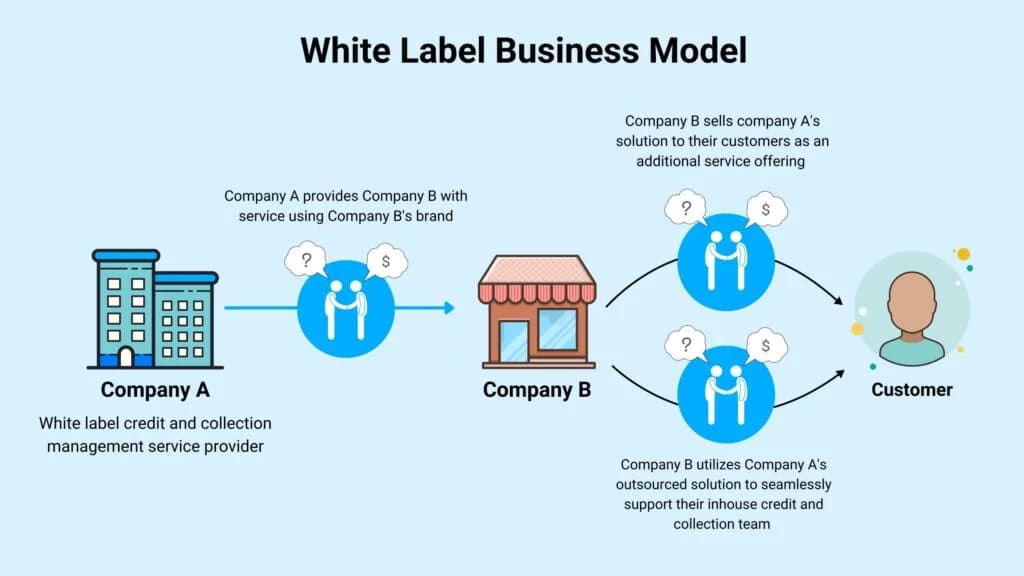
White-Label Vendor Compliance: Key Legal Areas Every Agency Must Address
Signing a white-label contract without a compliance audit is how agencies inherit fines they didn't earn. Here's what to lock down before the next vendor goes sideways.
Most agencies discover vendor compliance gaps the hard way: a client gets a breach notification letter, a PPC campaign runs afoul of financial advertising rules, or a link-building report reveals placements on private blog networks. By that point, you're already in damage-control mode. The smarter play is to treat vendor compliance as a pre-contract checklist, not a post-incident scramble. What follows is a risk-first walkthrough of the five failure modes that hurt agencies most, the contract language that protects you, and the operational habits that keep the whole system honest.
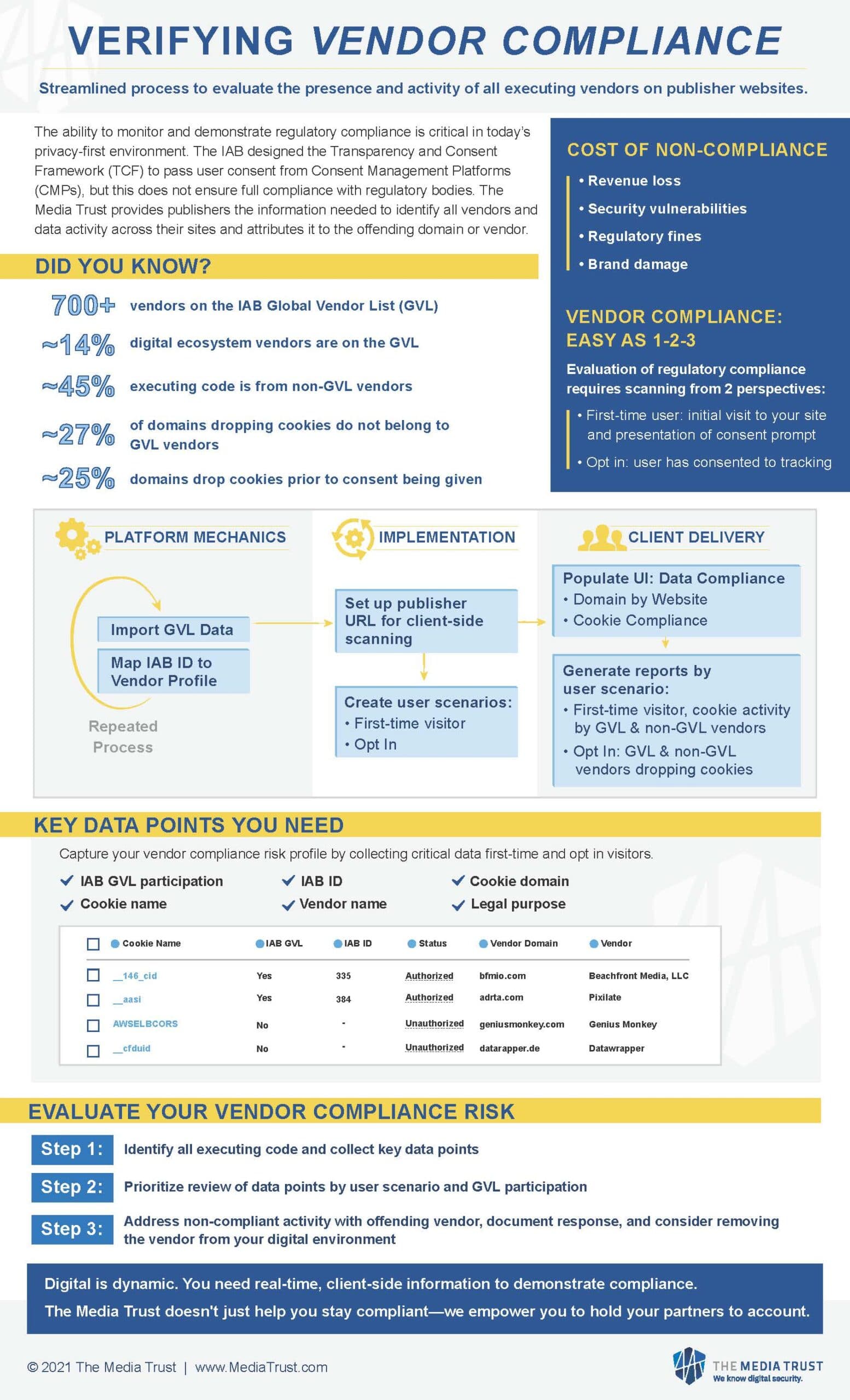
Data Privacy and Cross-Border Data Flows
This is the failure mode that carries the biggest regulatory price tag. The moment a white-label vendor touches personally identifiable information, whether that's a list of email addresses for a PPC remarketing campaign or analytics data tied to individual users, you are jointly accountable under GDPR, CCPA/CPRA, and a growing stack of local privacy statutes. The contract must include a Data Processing Agreement that explicitly names the vendor as a subprocessor and spells out what data they can touch, for how long, and for what purpose.
Breach notification timelines are non-negotiable specifics, not boilerplate. GDPR requires supervisory authority notification within 72 hours of discovering a breach; your vendor contract needs to require the vendor to notify you well inside that window, because you can't report what you don't know about. If the vendor hosts or processes data outside your client's jurisdiction, verify that transfer mechanisms are in place: Standard Contractual Clauses for EU data exports are the baseline, and you need documentary proof, not a verbal assurance.
Questions to ask every data-handling vendor: What subprocessors do you use, and are they listed in the DPA? Where is data physically stored and processed? What is your breach detection and notification SLA?
Intellectual Property Ownership
Content, code, creative assets, campaign structures built by a white-label vendor are only yours if the contract says so explicitly. A clause that grants the agency a "license to use" deliverables is not the same as an assignment of ownership, and that distinction matters when a client asks for their full asset library at contract end or when a vendor starts recycling your client's content for other clients.
Every new vendor contract should include a full IP assignment clause: all creative outputs, deliverables, and derivative works produced under the engagement are assigned to the agency in full upon delivery. For vendors who push back on full assignment, the fallback is an exclusive, perpetual, irrevocable license. What you cannot accept is any clause that allows the vendor to reuse, resell, or repurpose client assets without prior written consent. This comes up most often in content and link-building engagements where vendors maintain libraries of "repurposable" material.
Advertising, Consumer Protection, and Regulated-Industry Marketing
White-label content and PPC services create real exposure when the underlying work involves endorsements, affiliate relationships, or reviews that don't carry required disclosures. In the U.S., FTC rules require clear and conspicuous disclosure of material connections; in the UK, the ASA enforces equivalent standards. If your vendor is producing sponsored content, influencer briefs, or review-based landing pages, your contract needs to require that their production process includes disclosure compliance checks, not just a style guide.
The stakes climb significantly for agencies serving financial services or healthcare clients. Pre-publication legal review is not optional in these sectors: a vendor-produced piece of health content making an unsubstantiated efficacy claim, or a financial ad that omits required risk disclosures, can result in regulatory action against your agency even if the content originated with the vendor. Build a formal sign-off step into your content workflow for any regulated-sector client, and document it.
Questions to ask content and PPC vendors: Do your writers and campaign managers receive training on FTC/ASA disclosure requirements? What is your review process for content in regulated industries?
Anti-Spam and Consent Management
For agencies using white-label email or outreach services, the compliance surface extends to how the vendor sourced the lists and how they handle opt-outs. CAN-SPAM in the U.S. and CASL in Canada set the floor; many jurisdictions layer additional requirements on top. Sending to a list that wasn't built on affirmative consent, or using a platform that doesn't honor unsubscribe requests within the legally required window, creates direct regulatory exposure for the agency whose brand name is on the campaign.
Before onboarding any email or communications vendor, require written documentation of their list-sourcing methodology and a demonstration of their unsubscribe and suppression list mechanics. Consent records need to be exportable, not just internally accessible, so you can produce them if a regulator asks.
Anti-Fraud and Security Controls
Vendor access to client accounts, ad platforms, analytics dashboards, and CRM systems is a meaningful attack surface. SOC 2 Type II certification is the practical standard to require for any vendor with access to sensitive data or client systems; if a vendor can't produce it, require a compensating controls plan in writing. Contractual cyber insurance is a separate requirement: the vendor's policy should cover incidents originating from their systems, and you should be named as an additional insured or entitled to indemnification for costs you incur as a result of their breach.
Access management is where a lot of agencies get sloppy. Shared credentials, over-permissioned service accounts, and vendor access that isn't revoked after a project ends are all common. Your security annex should specify minimum access controls: least privilege, MFA, and a documented offboarding process.
Questions to ask all vendors: Can you provide your most recent SOC 2 Type II report or equivalent attestation? What cyber insurance coverage do you carry, and does it cover third-party claims?
Contractual Protections: The Non-Negotiable Clauses
Beyond the DPA, a compliant vendor agreement needs five specific elements:
- A security annex defining minimum controls and granting you audit rights, including the right to request spot audits and review third-party attestations annually.
- Vendor warranties that they comply with all applicable laws and that their deliverables do not infringe third-party intellectual property.
- Indemnification provisions requiring the vendor to defend and hold the agency harmless from third-party claims arising from the vendor's negligence, including regulatory fines where local law permits.
- A breach protocol section that sets specific notification windows, assigns remediation responsibilities, and allocates costs for incident response.
- Data retention and deletion rules: how long the vendor stores client data, and a binding deletion obligation upon contract termination with a certificate of destruction.
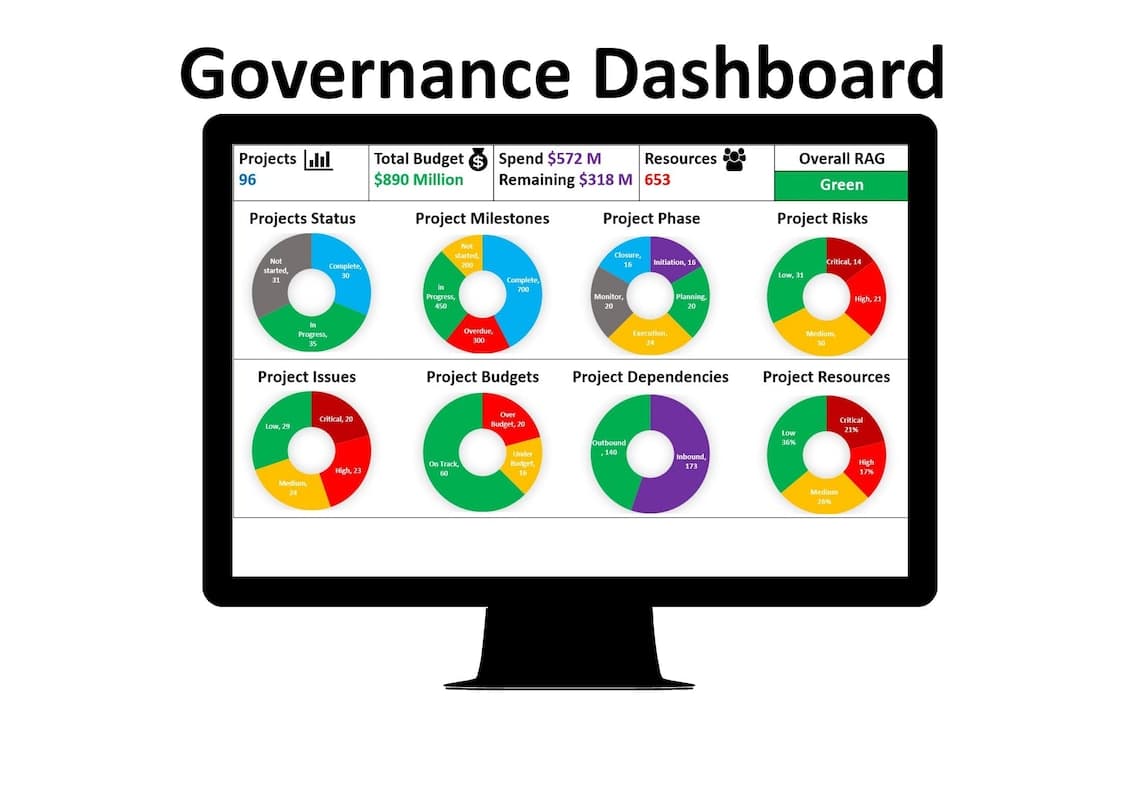
Operational Controls: Keeping Compliance Active
Contracts are only as good as the processes that enforce them. A quarterly vendor compliance review cadence, with required attestations and the option for spot audits, keeps vendors accountable and surfaces problems before they become client-facing incidents. Security questionnaires should be part of every vendor onboarding, with a periodic reassessment (annually at minimum) rather than a one-time gate.
For content in regulated industries, legal sign-off before publication needs to be a standing process item, not an ad hoc request. Build it into your project management templates so it's never accidentally skipped.
What Goes Wrong and How to Fix It
Two scenarios come up repeatedly in white-label engagements. In the first, a vendor exposes a client's contact list and then uses it for their own marketing. The correct response is immediate contract termination, an indemnity claim against the vendor, and a client remediation plan that includes breach notification and credit monitoring where applicable. In the second, a link-building vendor delivers placements through private blog networks in violation of search engine quality guidelines. The remedy is a contractual removal clause that obligates the vendor to disassociate the links, a remediation credit, and an immediate audit of every placement they've delivered across all clients.
Both scenarios share a root cause: the agency didn't have the contractual leverage to respond quickly. The clauses above exist precisely to give you that leverage before you need it.
The Business Case and the 30-Day Plan
Agencies with demonstrable vendor compliance programs consistently win larger enterprise clients and command higher retainer fees; enterprise procurement teams now routinely ask for vendor management policies as part of RFP responses. Noncompliance isn't just a regulatory risk; it's a commercial one, because a single publicized incident can undo years of client trust.
The 30-day implementation plan is straightforward:
- Execute DPAs with every vendor currently handling personal data.
- Require SOC 2 Type II certification or a compensating controls plan from any vendor with access to sensitive data or client systems.
- Add IP assignment language to all new vendor contracts; flag existing contracts for renewal-cycle remediation.
- Write an incident response playbook and run a tabletop exercise with your team before a real incident forces you to improvise.
Compliance built into vendor selection and ongoing governance isn't a legal burden; it's what separates agencies that scale enterprise accounts from those that stay stuck managing risk they didn't create.
Sources:
Know something we missed? Have a correction or additional information?
Submit a Tip