Blender project files on marketplaces weaponized to deliver StealC infostealer
Weaponized .blend files on 3D marketplaces have delivered the StealC V2 infostealer for at least six months, with a sample SHA256 c62e094c... and a rigged NASA spacesuit used as a free decoy.

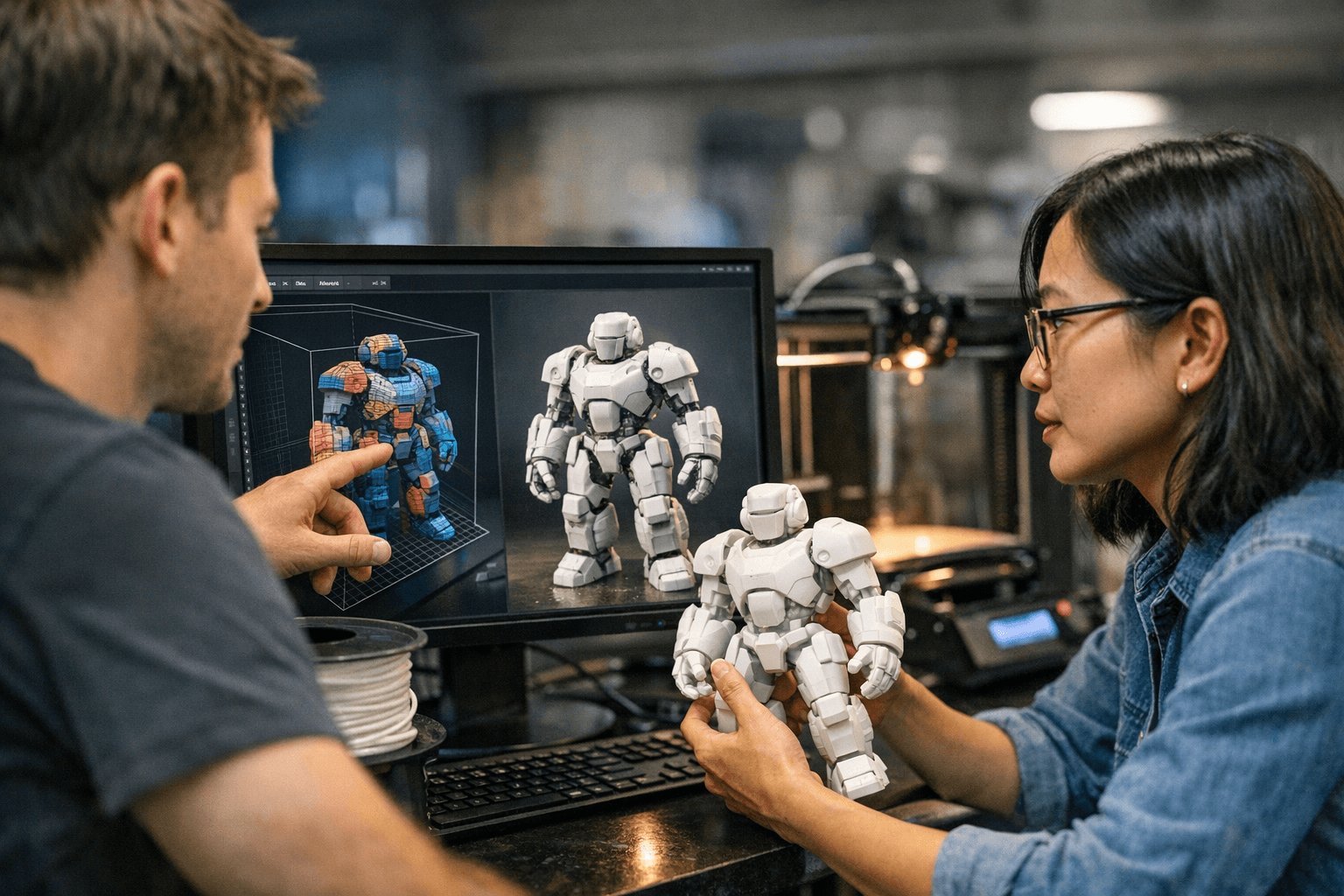
Malicious Blender project files uploaded to marketplaces such as CGTrader are delivering the StealC V2 infostealer and have been active for at least six months, researchers report; one analyzed sample carries SHA256 c62e094cf89f9a2d3b5018fdd5ce30e664d40023b2ace19acc1fd7c6b2347143 and contains a weaponized Rig_Ui.py script. The embedded Python code takes advantage of Blender’s Auto Run Python Scripts setting to execute on users’ machines when an untrusted .blend is opened, triggering a multi-stage download and execution sequence that ends with credential theft.
The attack chain is specific and repeatable: weaponized .blend files use bpy.data.texts and add-on-style scripts to auto-execute, fetch loaders from remote hosts, extract two ZIP archives, run PowerShell scripts, and install StealC V2 plus an auxiliary Python stealer before establishing Pyramid C2 infrastructure. Renderhub and Hivepro detail the multistage downloads and note that BleepingComputer observed the initial loader fetched from a Cloudflare Workers domain. Morphisec documents the Rig_Ui.py component and reports ongoing prevention activity.
Stolen data types are concrete: browser and crypto wallet credentials, Telegram and Discord credentials, VPN client credentials and mail client logins are all within StealC’s capabilities. Renderhub warns about an auxiliary Python stealer paired with StealC and notes that “The latest variant has been completely ignored by security engines on VirusTotal, which makes it particularly nasty.” Blender’s default capability to execute Python is central to the risk: “Blender can execute Python scripts for automation and many more; it's a default language for Blender add-ons, after all,” Renderhub states.
Morphisec and Hivepro link the campaign to a broader evolution of StealC. Morphisec describes the operation as “Russian-linked” and Hivepro describes “Russian-speaking threat actors,” with Morphisec adding that StealC V2 was first announced on April 28, 2025 and subsequently attracted lower-tier cybercriminals through underground marketplace edits. Morphisec also ties the techniques to prior operations that impersonated the Electronic Frontier Foundation to target Albion Online players with StealC V2 and Pyramid C2.
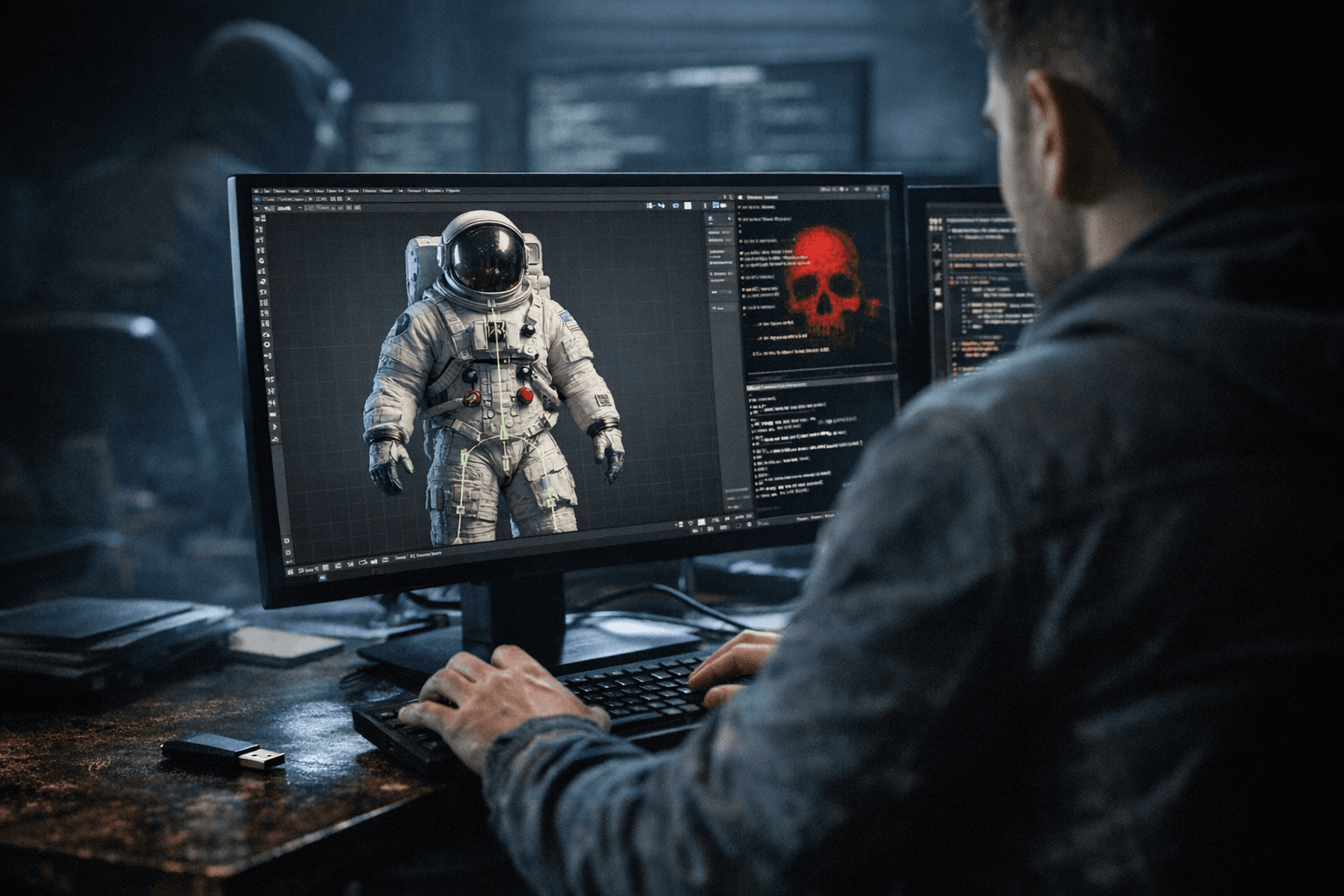
Marketplace lures are explicit: Renderhub highlights a “very complex rigged model of a NASA space suit, which was offered for free,” and Morphisec’s slides reference a free acs-orange-spacesuit model path on CGTrader as an example. Marketplaces generally lack the ability to inspect embedded Python in user-submitted .blend files, increasing exposure.
Immediate mitigation is straightforward and urgent: Disable Blender’s Auto Run Python Scripts unless the file source is trusted. “Keep Auto Run disabled unless the file source is trusted,” Morphisec advises. For defenders, Morphisec reports success in blocking multiple incidents: “In recent months, Morphisec has successfully prevented multiple sophisticated malware campaigns leveraging Blender Foundation files to deliver the notorious StealC V2 infostealer.” Verify any suspicious .blend against known sample hashes and query marketplace removals and Blender Foundation guidance before opening third-party assets.
Know something we missed? Have a correction or additional information?
Submit a Tip