Russian SIGINT system uses Meshtastic-Sniffer to geolocate Ukrainian meshes
A passive Meshtastic sniffer tied to Russian SIGINT can TDOA-geolocate Ukrainian meshes, a blunt warning that LoRa nodes are not anonymous.

A passive receiver described as meshtastic-sniffer is now being tied to Russian SIGINT work that can detect, analyze, and TDOA-geolocate Meshtastic meshes in Ukraine. For anyone treating Meshtastic as harmless, anonymous radio chatter, that is the wrong lesson.
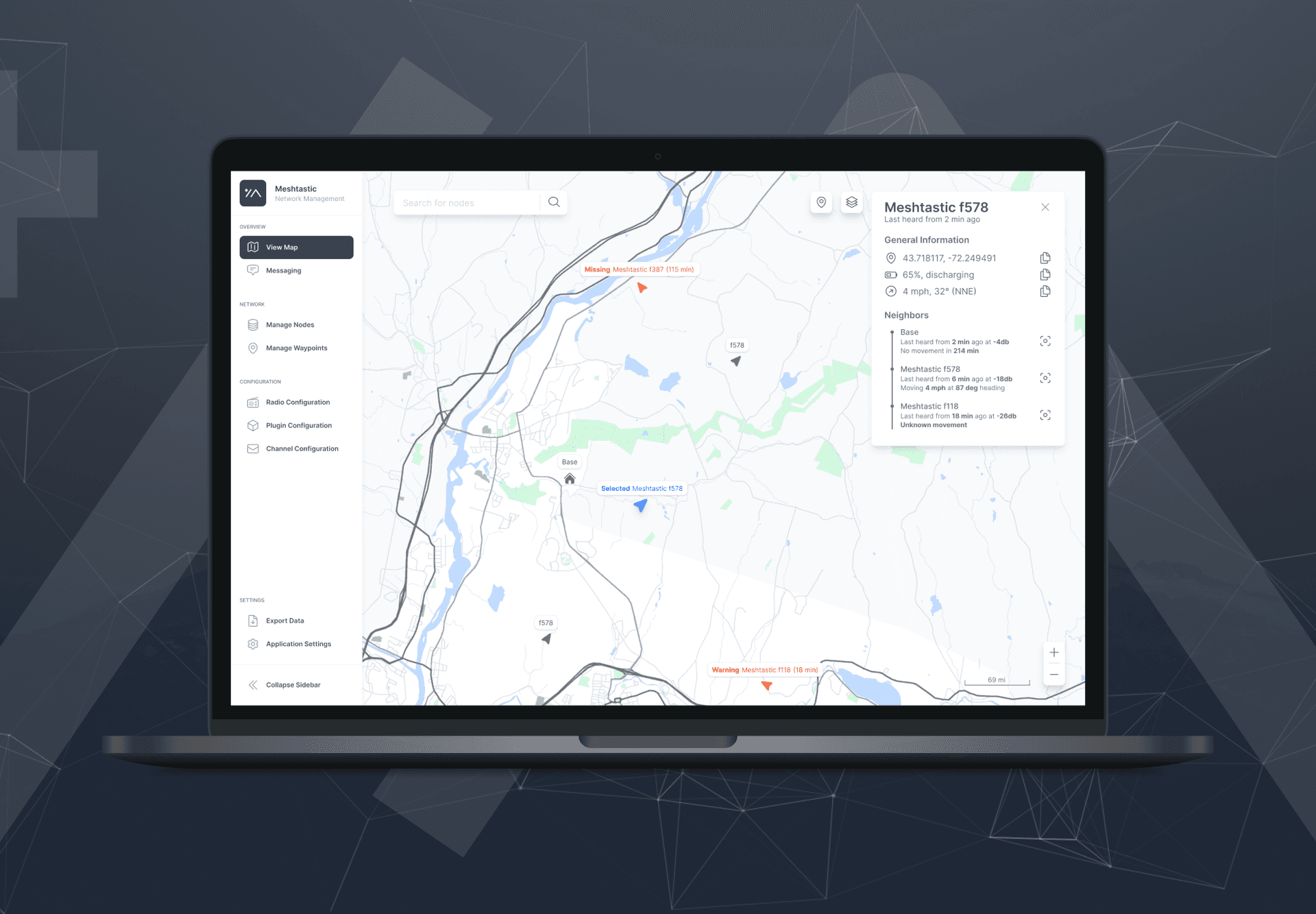
Meshtastic was built as an open-source, off-grid, decentralized mesh network for affordable, low-power devices. It runs over LoRa radios, works without cell towers or internet, and the project says it now supports more than 100 community-supported devices, 1,800-plus contributors worldwide, 26 LoRa regions, and 39 languages. That reach is a strength, but it also means a lot of different habits, firmware builds, and deployment styles are in the wild at once, which is exactly where operational security gets messy.
The sharpest warning here is not about encryption marketing or “hobby gear” assumptions. Meshtastic’s own stack includes optional GPS-based location features, and that alone makes careless use dangerous in contested environments. Add packet metadata, repeated beaconing, predictable node placement, and multiple listening stations, and a passive system can start drawing a map. Once a receiver can fuse data from more than one site, time difference of arrival becomes enough to turn a low-cost mesh into a geolocation problem.
That is what makes cemaxecuter’s GitHub listing especially relevant. The repository named meshtastic-sniffer is described as a wideband passive Meshtastic LoRa receiver with multi-station fusion and offline PSK recovery. In plain English, it is not a toy scanner. It is the kind of tool that can sit quietly, collect traffic, combine signals from several stations, and extract enough structure to make a mesh visible even when nobody is transmitting a GPS pin on purpose.
The warning lands harder because Meshtastic is already active in Ukraine. The Meshtastic Ukraine GitHub organization hosts work on firmware, mqtt-serial, grafana, rangebot, wiki, and firmware-patch-ua, which shows the ecosystem is being adapted for real use, not just lab demos. That also means the community has to think like a radio target, not a software user. If a node matters, assume it can be found. If a GPS feature is enabled, assume the location can leak. If the mesh is being used near a front line, assume passive collection, multi-station fusion, and sloppy defaults can expose the whole layout. Meshtastic is still a powerful off-grid tool, but this episode is a hard reminder that decentralized does not mean invisible.
Know something we missed? Have a correction or additional information?
Submit a Tip